Amazon Aurora relational database (DB) has to be monitored continuously to secure the confidential data it holds. Maintaining an audit trail of all database events is not only a key factor in passing an IT audit, but also helps in identifying and mitigating potential threats. Log360, a comprehensive SIEM solution, ensures that all Aurora DB logs are analyzed and recorded.
Log360 can collect Aurora DB logs from the AWS CloudTrial console and AWS S3 server, and store them in a central location, which makes it easy to analyze the logs and get insights on error events, alteration events, and permission changes carried out in the database.
Log360 can monitor all changes made to Aurora relational databases such as additions, deletions, or modifications done to the schema and tables. It can also help track modifications made to database user permissions, privilege escalations, and data exfiltration attempts.
To ensure cloud data security and to comply with the regulatory mandates, you need to periodically audit your Aurora database logs. Audit reports generated by Log360 present the error events, access denied events, security group configuration change events, and snapshot events in the form of intuitive dashboards featuring graphs for quicker analysis.
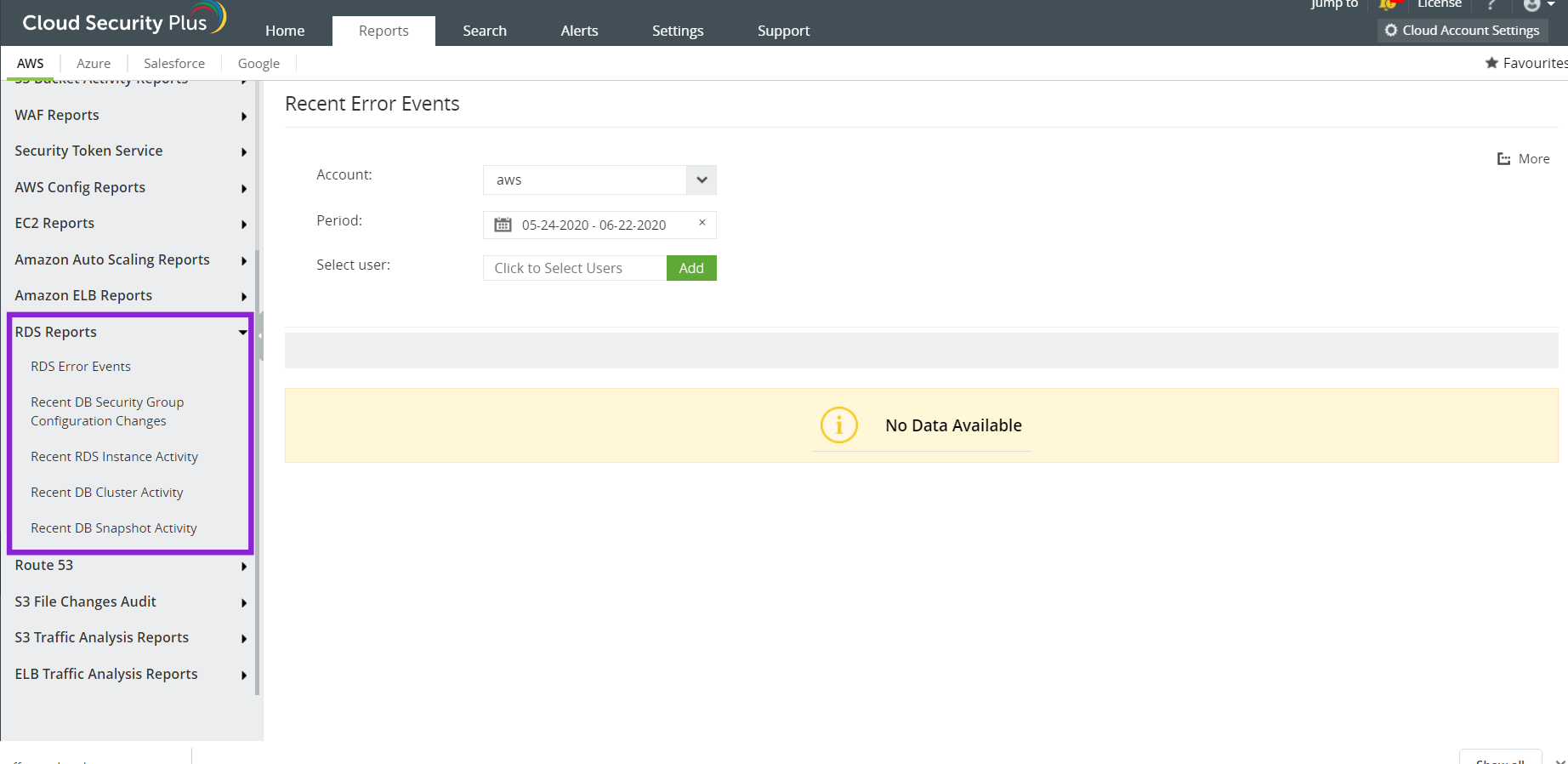
Log360 can audit all database events and generate insightful reports. These reports are presented as interactive dashboards to help you understand all your database events at a glance.
Consider that an attacker has already obtained access to your database. The attacker now wants to access a critical server, which contains highly confidential information. When the attacker tries to access a privileged user account at an unusual hour and makes multiple attempts to login, this is considered a potential threat. This activity will be recorded by Log360 and flagged as a threat for multiple logon failures and anomalous user behavior.
To top it all off, you can also configure alerts so you're instantly notified of anomalous activities via SMS and email. You can also initiate incident response workflows for incidents to mitigate threats at the earliest stages.