Apex batch processes and queries follow an order of execution in Salesforce. If there are multiple Apex triggers executing INSERT, UPDATE, and DELETE commands in the Oracle database hosted by Salesforce or any other external databases linked to it, the flow of saving changes made to the database also depends on the order of execution.
Track when anyone modifies, accesses, or views records from databases using Apex Salesforce Object Query Language (SOQL) and Salesforce Object Search Language (SOSL) queries to ensure no malicious changes are made to sensitive information hosted in your databases.
All changes carried out using Apex query languages, triggers, and batch processes are recorded as logs in Salesforce. Though any changes made in Salesforce using Apex can be tracked by the Log Inspector tool, it can be a tedious task to access the Developer Console of Apex to view this log information, interpret it, and identify anomalies.
Log360 helps you audit all Salesforce Apex execution activities, analyze them, and identify deviant and malicious activities that could be potential threats to your organization. It extracts the event logs and debug logs from the Salesforce instance, and monitors:
Consider that a normal user, without any privileges, raises an Apex request to retrieve records from your database that contains confidential information. The user raises the request from a class called "Without Sharing," which executes all queries in the System mode.
Running queries in this mode will return all records requested by the user, violating object permissions, sharing rules, and field-level security specified for that user. This event can result in a data exfiltration incident, which can be prevented using Log360. Log360 allows you to configure alerts for processes initiated in the System mode by normal users to avoid such security hazards.
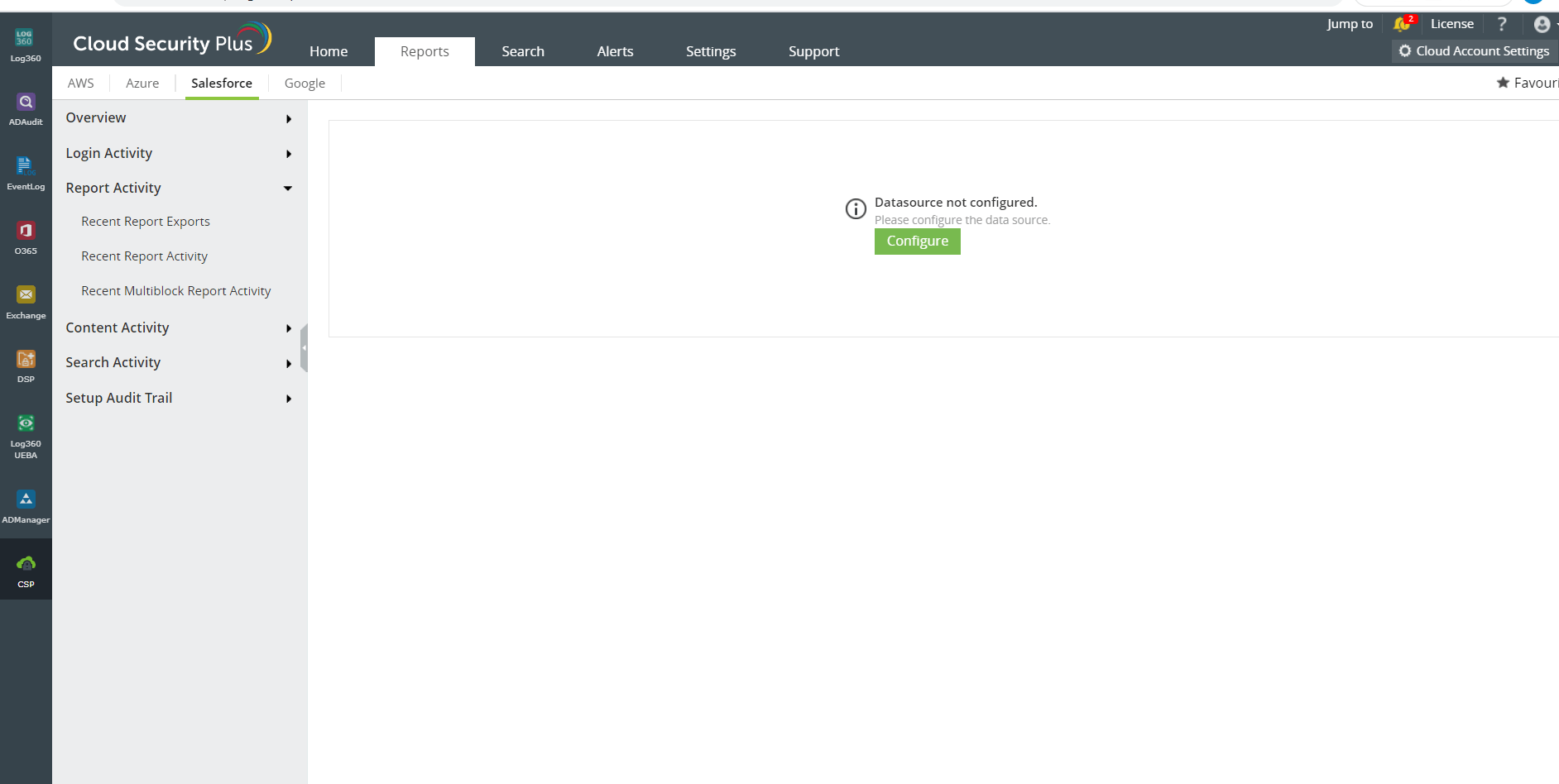
Log360 generates interactive reports in the form of graphs and charts after analyzing logs obtained from Salesforce. It reports on logon and logoff activities, report export activities, and recent content change and distribution activities to help you spot anomalies and take necessary action.
Using Log360, you can configure alerts for malicious activities to get notified via SMS and email about impending attacks.
Salesforce auditing has never been easier. See for yourself.