It is the responsibility of IT security administrators to monitor their networks closely and identify potential threats or indicators of attacks. A prominent security threat, abnormal login activities, can be detected by monitoring unusual logons in your network.
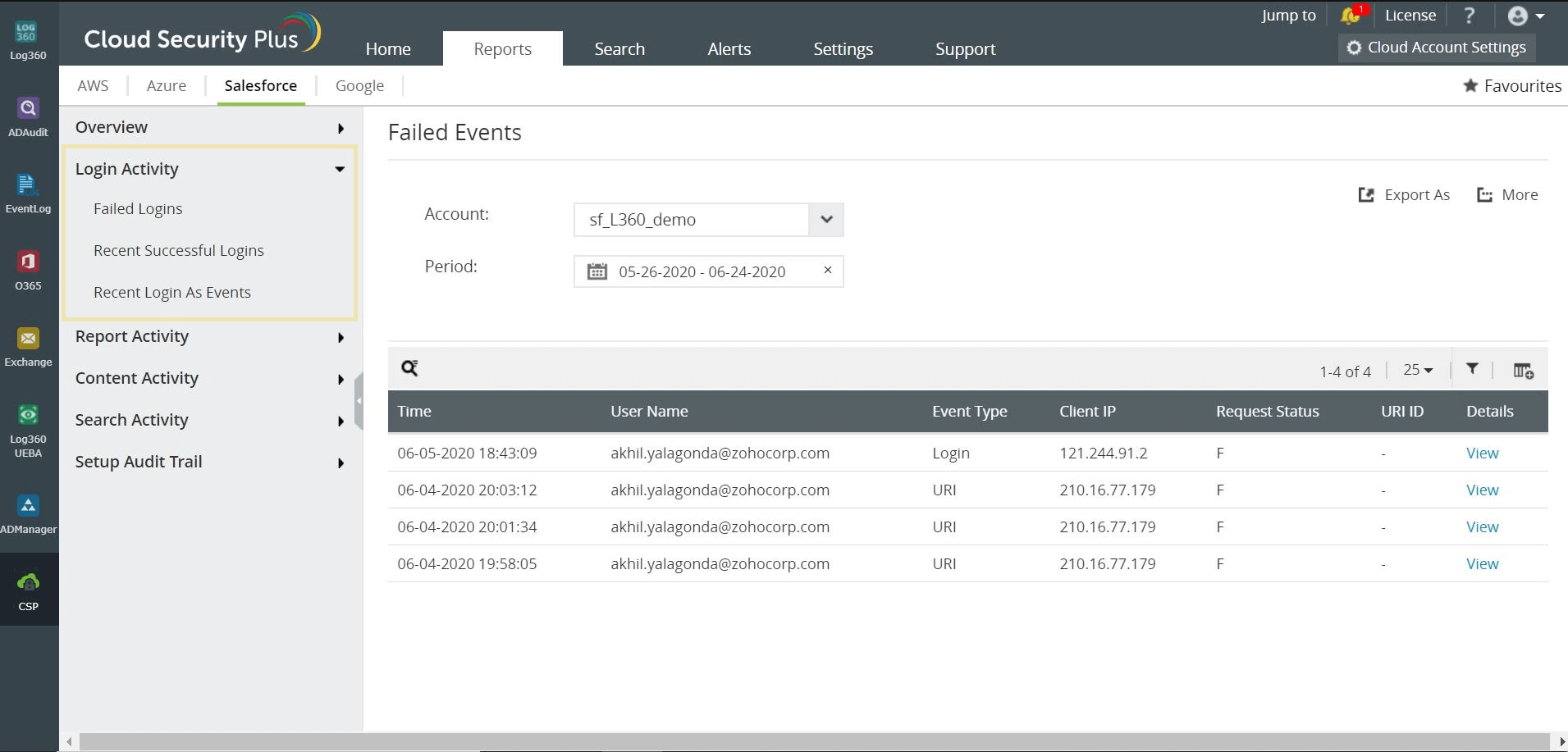
When it comes to a cloud platform, besides establishing strong security controls, user login activities should be monitored granularly, as these event might indicate a possible intrusion. ManageEngine Log360 tracks all Salesforce user login activities and provides detailed insights on who logged in from where and when.This solution also provides insights on the failed logins and recent successful logins to help IT admins obtain a snapshot of what's going in the Salesforce platform.
Log360 provides detailed information on recent successful login events, failed login events, and more. This helps IT security admins analyze user activity and detect misuse of privileges and unauthorized access attempts.
Here's a typical security use case on how Log360 can be beneficial for you in monitoring Salesforce login activities:
Assume that an employee tries to sabotage the organization's reputation by exfiltrating sensitive customer data. This unscrupulous user downloads the data by logging in and exporting the business-critical data from the Salesforce app. Log360 easily tracks suspicious events and alerts you in real time via email and SMS notifications.
The solution can also spot any unusual login activity based on time, pattern, or count. For instance, if the malicious insider is trying to login outside business hours, then the Log360's user entity behavior analytics (UEBA) capability easily detects and reports this irregular behavior to you.
If the login activity is typical but the user is trying to export a report that has confidential data, it can also be tracked using Log360. The solution provides detailed information for every report export operation, such as who did what activity and from when. These detailed security audit report helps security admins detect suspicious behaviors and investigate incidents quickly.
Click here to find out more details, or see it in action, right here.