ADSelfService Plus supports Active Directory (AD)-based single sign-on (SSO) for Salesforce and any other SAML-enabled application. Upon enabling SSO for Salesforce in ADSelfService Plus, all users have to do is simply log in to their Windows machines using their AD domain credentials. Once logged in, users can securely access Salesforce in one click without having to enter their username and password again.
ADSelfService Plus supports both Identity Provider (IdP) and Service Provider (SP)-initiated SSO for Salesforce.
IdP-initiated SSO for Salesforce: Users need to log in to the ADSelfService Plus self-service portal first, and then click on the Salesforce icon on the Applications dashboard to access Salesforce.
SP-initiated SSO for Salesforce: Users can access their Salesforce domain via a URL or bookmark. They will automatically be redirected to the ADSelfService Plus portal for login. Once they've signed on, they'll be automatically redirected and logged into the Salesforce portal.
Download and install ADSelfService Plus if you haven’t already.
With ADSelfService Plus, you can use the existing AD domain credentials of users for authentication during SSO. So, first you need to configure an AD domain in ADSelfService Plus to enable SSO for Salesforce.
ADSelfService Plus will try to automatically add all the domains that it can discover in your network. If your domains are automatically added, skip to Step 9; otherwise, follow Steps 1-8 to add them manually.
Getting the SAML details from ADSelfService Plus
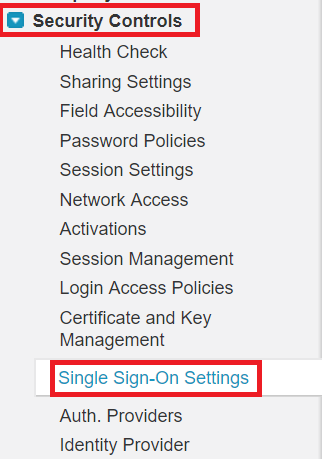
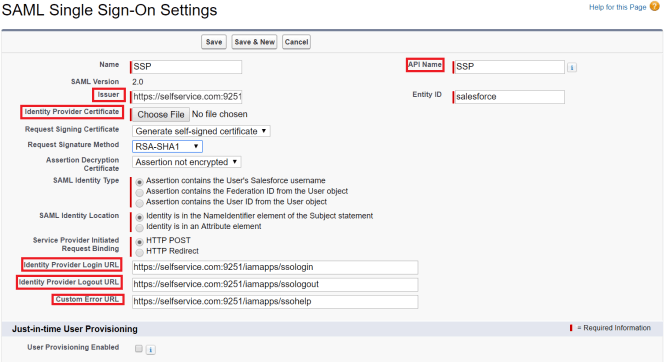
Configuring SSO settings in Salesforce.
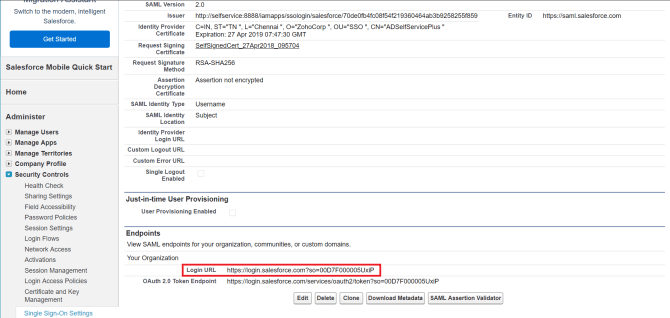
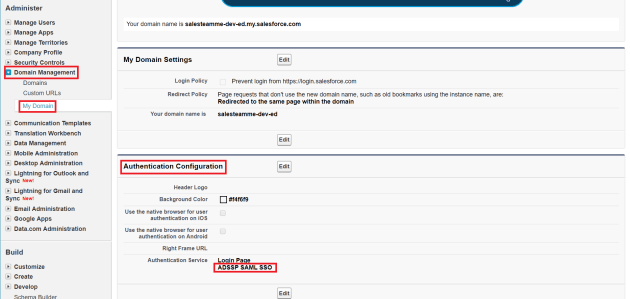
Adding your Salesforce domain in ADSelfService Plus and enabling SSO
Note: ADSelfService Plus allows you to create OU and group-based policies for your AD domains. To create a policy, go to Configuration → Self-Service → Policy Configuration → Add New Policy. Click Select OUs/Groups, and make the selection based on your requirements. You need to select at least one self-service feature. Finally, click Save Policy.
Your users can now log into their Salesforce accounts automatically using single sign-on.
Free Active Directory users from attending lengthy help desk calls by allowing them to self-service their password resets/ account unlock tasks. Hassle-free password change for Active Directory users with ADSelfService Plus ‘Change Password’ console.
Get seamless one-click access to 100+ cloud applications. With enterprise single sign-on, users can access all their cloud applications with their Active Directory credentials. Thanks to ADSelfService Plus!
Intimate Active Directory users of their impending password/account expiry by mailing them these password/account expiry notifications.
Synchronize Windows Active Directory user password/account changes across multiple systems, automatically, including Office 365, G Suite, IBM iSeries and more.
Ensure strong user passwords that resist various hacking threats with ADSelfService Plus by enforcing Active Directory users to adhere to compliant passwords via displaying password complexity requirements.
Portal that lets Active Directory users update their latest information and a quick search facility to scout for information about peers by using search keys, like contact number, of the personality being searched.