Microsoft 365 (formerly Office 365) is being widely adopted among organizations in recent times. While doing so, the users of the organization are burdened with remembering yet another username and password. This not only causes password fatigue but also increases the number of help desk tickets requesting a password reset. Is your organization looking for a solution to overcome such challenges?
ADSelfService Plus offers secure single sign-on (SSO) that provides users with seamless, consistent access to all cloud applications, including Microsoft 365. It provides SSO by integrating your on-premises Active Directory (AD) with Microsoft 365 and other SAML-enabled applications. So, when users try to log in to Microsoft 365, ADSelfService Plus authenticates them using their Windows AD domain credentials to sign them in automatically—they don't have to re-enter their username or password.
ADSelfService Plus also supports secure AD-based SSO for over one hundred other SAML-, OAuth-, and OpenID-enabled enterprise applications such as Dropbox, Google Workspace, Salesforce, and ServiceNow.
ADSelfService Plus eliminates the complicated process of setting up AD-based Microsoft 365 SSO via Microsoft's Active Directory Federation Services (ADFS) and Azure AD Connect (formerly DirSync). It uses the widely-adopted industry standard SAML 2.0, which allows you to securely utilize the identities in your existing AD infrastructure for SSO.
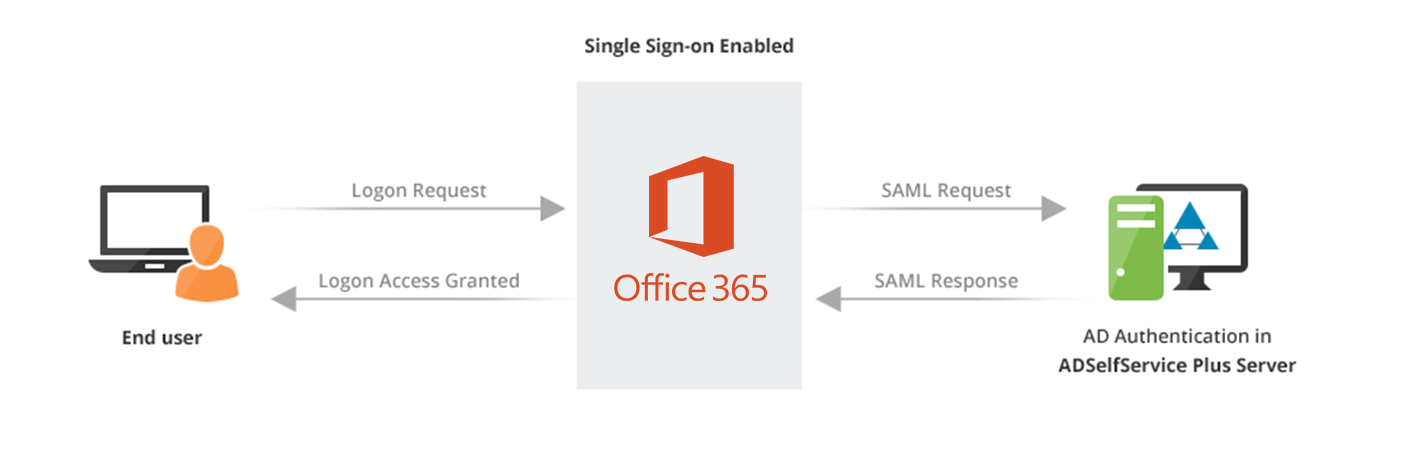
ADSelfService Plus supports both identity provider (IdP)- and service-provider (SP)-initiated SSO flows for Microsoft 365. The diagram below depicts the SP-initiated SAML SSO flow for Microsoft 365 where a user initially requests access to the application and is then redirected to ADSelfService Plus to complete authentication. Once authenticated, the user is given access to Microsoft 365. In the IdP-initiated SAML SSO flow, the user first logs in to ADSelfService Plus after being authenticated and then gets one-click access to Microsoft 365 from their dashboard of assigned applications.
With ADSelfService Plus, you can granularly control who has access to Microsoft 365 based on OUs and groups in AD. You can also create multiple policies to ensure that only specific users have access to Microsoft 365 and its business-critical services.
ADSelfService Plus lets you add an extra layer of protection for Microsoft 365 SSO by enabling MFA. Besides AD credentials, you can configure other authentication factors for your users accessing Microsoft 365. Below are some of the authentication factors that ADSelfService Plus offers:
Find the complete list of supported authenticators here.
Relieve your users from having to remember different usernames and passwords for various enterprise applications.
Streamline access using policies which ensure that only specific users have access to certain applications based on AD OUs and groups.
Deploy SSO to enhance your users' productivity by giving them simple and secure access to the resources they need.
As an administrator, you can enable one or more MFA authentication methods for users during Microsoft 365 SSO for added security.
Free Active Directory users from attending lengthy help desk calls by allowing them to self-service their password resets/ account unlock tasks. Hassle-free password change for Active Directory users with ADSelfService Plus ‘Change Password’ console.
Get seamless one-click access to 100+ cloud applications. With enterprise single sign-on, users can access all their cloud applications with their Active Directory credentials. Thanks to ADSelfService Plus!
Intimate Active Directory users of their impending password/account expiry by mailing them these password/account expiry notifications.
Synchronize Windows Active Directory user password/account changes across multiple systems, automatically, including Office 365, G Suite, IBM iSeries and more.
Ensure strong user passwords that resist various hacking threats with ADSelfService Plus by enforcing Active Directory users to adhere to compliant passwords via displaying password complexity requirements.
Portal that lets Active Directory users update their latest information and a quick search facility to scout for information about peers by using search keys, like contact number, of the personality being searched.