The neural system of most of the enterprises is the network. With the emergence of social networking, video streaming, peer-to-peer technology, cloud computing and SaaS, it's safe to say that modern enterprises are only as good as their networks especially in terms of the bandwidth and security they provide. Be it banks securing their data against thefts or business organizations securing their network against security threats and attacks, the lurking threat of getting breached, compromised and damaged by an unknown zero-day intruder is always relevant. Moreover, continuous evolution of intrusion techniques has made the task of ensuring network security increasingly difficult in spite of becoming all the more critical.
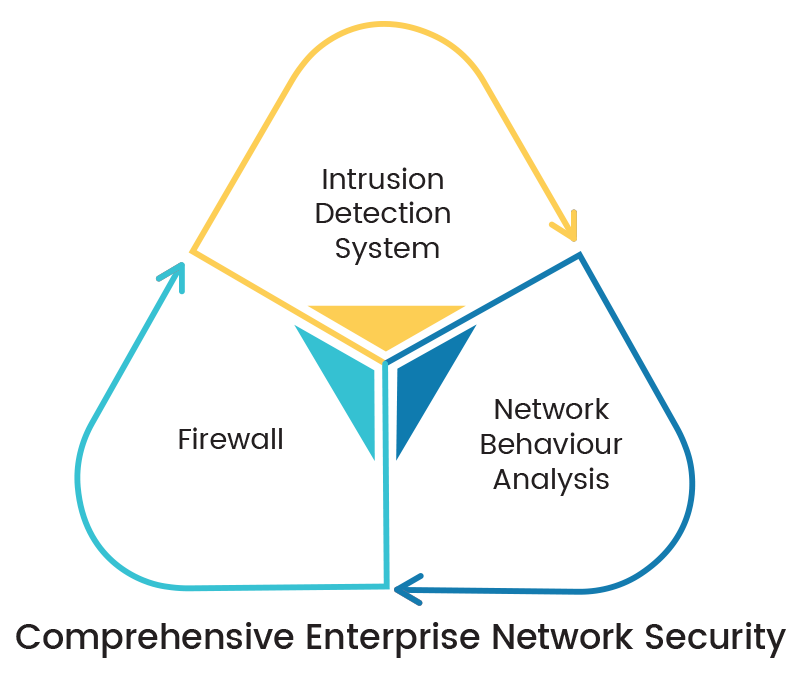
Predominantly, the security systems are classified into three types. They are (i) Firewall Systems, (ii) Intrusion Detection/Prevention (IDS/IPS) Systems and (iii) Network Behavior Analysis (NBA) Systems also known as Network Behavior Anomaly Detection (NBAD) Systems. While all three of them have their own unique strengths and weaknesses, they complement each other to form a holistic network security strategy. However, the first two are widely prevalent and perceived as essential components, the third is not so. This leaves the network vulnerable to several zero-day attacks, unknown worms, internal threats, etc., as well as letting them lag behind in terms of overall traffic visibility, access policy decisions, security posture assessment and a reasonably sure confirmation of network security.
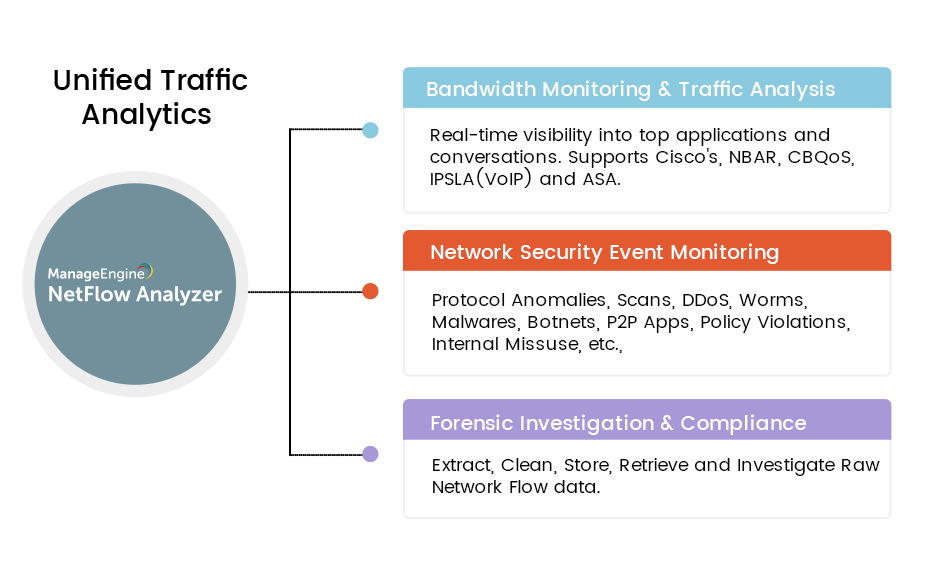
Bandwidth monitoring & traffic analysis and network security analytics & behavior anomaly detection are interdependent and complementary by nature. NetFlow Analyzer, coupled with the Security module, unifies these complementary solutions to provide a holistic and reliable decision support system in a single user-friendly interface. While NetFlow Analyzer gives you an in-depth visibility in to your network traffic and bandwidth utilization, the Security module offers continuous network security monitoring and network anomaly detection capabilities.
NetFlow Analyzer’s Security Analytics is powered by machine learning and built on the MITRE ATT&CK framework, giving your network security an intelligent edge. Instead of just flagging obvious threats, it continuously studies network behavior and connects the dots between smaller, seemingly harmless activities. When pieced together, these patterns could reveal a hidden attack that might otherwise go unnoticed.
For example, imagine an employee’s workstation making a few harmless-looking DNS requests. On their own, they wouldn’t raise suspicion. But when correlated with unusual outbound traffic and failed login attempts, Security Analytics detects the bigger picture, i.e., a possible data exfiltration attempt. That’s when it raises an event, scores it based on severity, and helps security teams prioritize what to fix first.
With over 119 MITRE ATT&CK–aligned detection rules, adaptive learning to cut down noise and false positives, and asset-based monitoring (not just IP-based), Security Analytics gives security teams context-rich insights. Instead of overwhelming them with alerts, it provides clarity, enabling faster and more confident responses to potential threats.
Download 30-day free trial | Request Demo
- Fred Hassard Sr. Network Engineer in Adventist Health
Featured links
View how enterprise network bandwidth is used. Allocate enough bandwidth for applications critical to business.
Get real-time visibility into your network traffic using NetFlow Analyzer. Know who your top talkers are on the network in real-time.
Monitor critical factors affecting VoIP, Video performance and ensure best-class service levels. Ensure seamless WAN connectivity through WAN RTT monitoring.
Validate the effectiveness of your QoS policies using CBQoS reports from NetFlow Analyzer. Prioritize your network traffic accordingly.
Assess future network requirements based on capacity planning reports.