Cisco Firewall Rules, Configuration & Logs Analyzer
A versatile combination of feature packed Cisco firewall and a firewall analyzer unearthing the full potential of the firewall is a best defense against network threats. Firewall Analyzer's Cisco management module helps you with:
- Cisco firewall rule management
- Cisco firewall change management
- Cisco firewall compliance reports
- Cisco firewall security audits
- Cisco firewall alerts
- Cisco firewall exclusive
Cisco firewall rule management
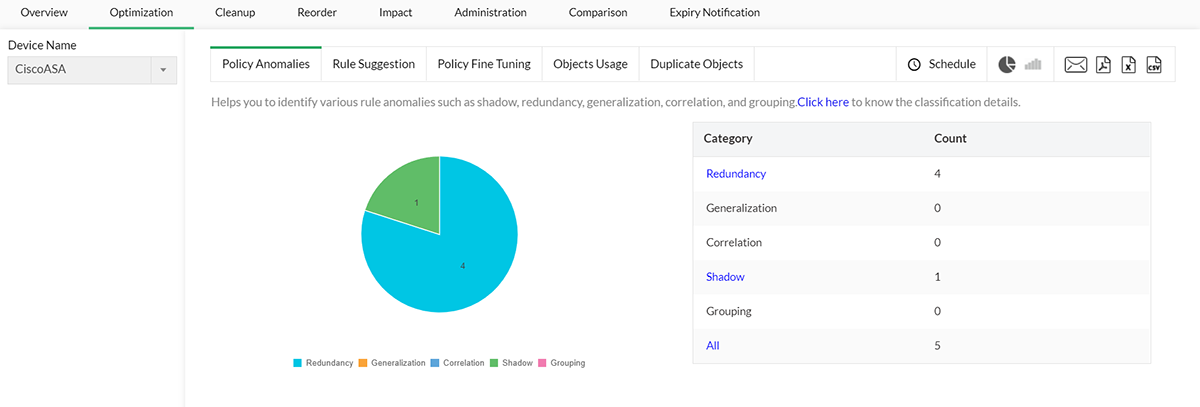
The efficiency of your Cisco firewall rules is a key factor that determines how effective your Cisco firewall appliance is. Firewall Analyzer helps with firewall rule review by providing visibility on all the existing rules. It allows you to see how effective your firewall rules are and also identifies rule anomalies such as shadow, redundancy, generalization, correlation, and grouping. Firewall Analyzer (Cisco Firewall Rule Analyzer) helps optimize your firewall by providing suggestions on rule position. By correlating the number of rule hits with rule complexity and anomalies, it can also suggest changes to improve the firewall's performance. Thus, Firewall Analyzer helps with adhering to firewall best practices.
Cisco firewall change management
Firewall Analyzer generates configuration change management reports that help you find who made what changes, when, and why. Not only that, it sends real-time alerts to your mobile phone when changes happen. This report ensures that security admins have tight control over the firewall change request process. Firewall Analyzer is a Cisco firewall monitoring tool, meaning all the configurations and subsequent changes made in the firewall device are captured and stored in the database. Reports can also be generated periodically (daily, weekly, monthly, ect.).

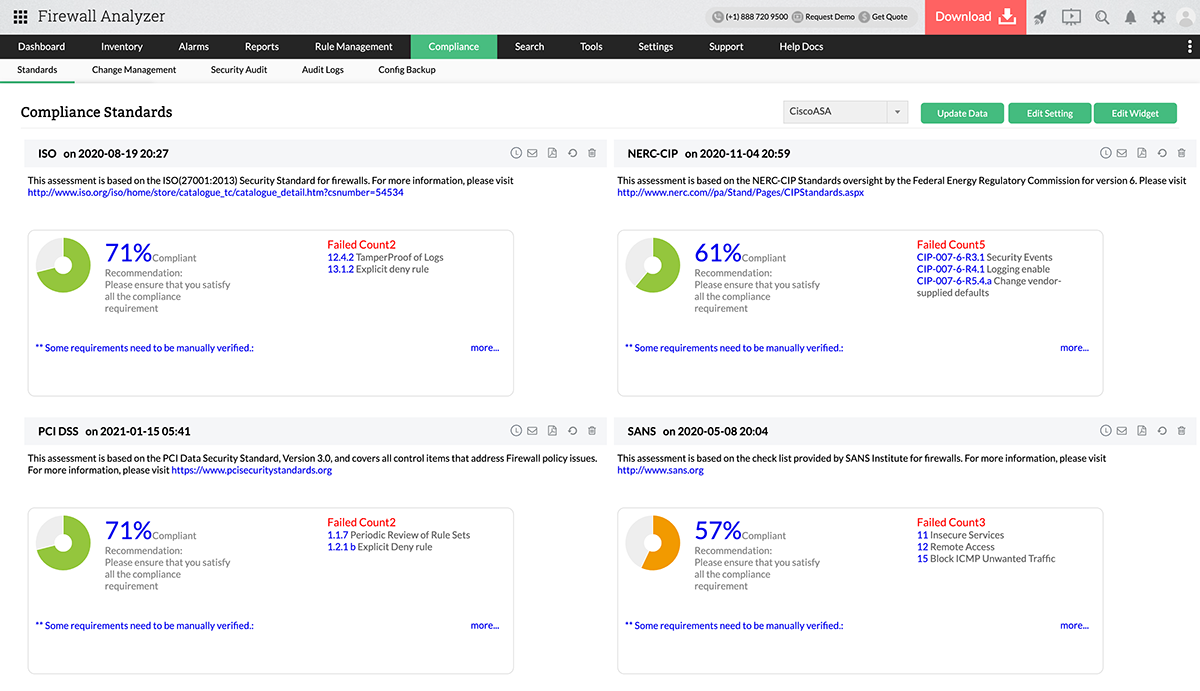
Cisco firewall compliance reports
Firewall Analyzer acts as a firewall compliance tool and generates out-of-the-box compliance reports on the latest regulatory standards. This firewall compliance software generates compliance reports for the following security mandates:
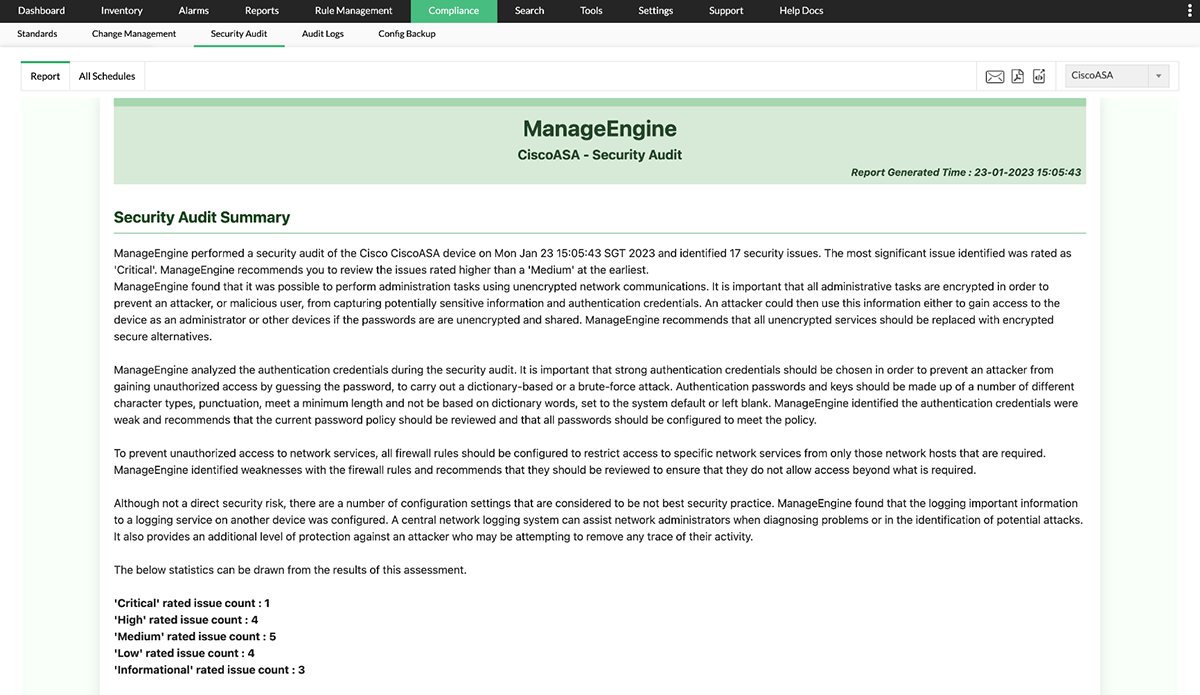
Cisco firewall security audits
Firewall Analyzer performs security audits and reports on the manual configuration errors in your Cisco firewall device. This Cisco firewall audit tool helps you identify the security issues in your device. Firewall Analyzer provides a firewall security audit checklist with an overall security rating. The impact each issue has on device security is rated by severity and the difficulty level in fixing the issue is assessed. Based on these results, the report recommends firewall security best practices.
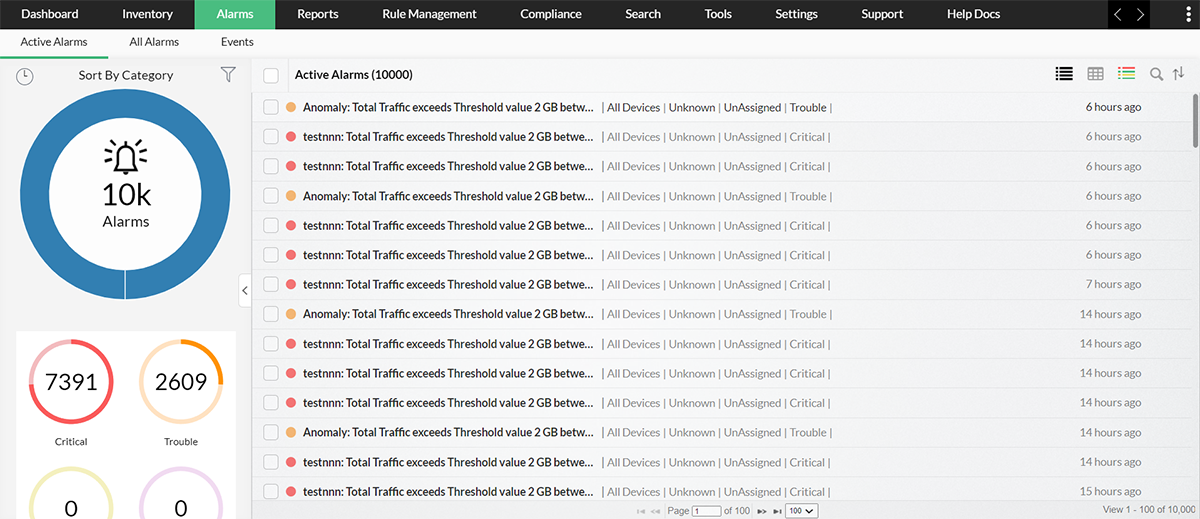
Cisco firewall alerts
Apart from exhaustive firewall reports on network security, Firewall Analyzer offers a comprehensive alarm management module. Alarms are generated for anomalous security and bandwidth events. Any alarm that is generated is recorded in the product UI. These alarms can be sent in real time via email and SMS. Alarms can also trigger scripts and mitigate security events the very moment an attack is detected.
Security and traffic reports.
Firewall Analyzer performs firewall log analysis and provides the following reports:
Cisco firewall exclusive
Support for Cisco virtual firewalls
Firewall Analyzer also supports virtual firewalls and thus acts as an extensive Cisco firewall management software. The virtual firewalls are dealt like normal firewalls and all the reports, alarms and other features are offered.
Search for Cisco firewall security events
Extensive indexing of Cisco firewall logs makes search for security events easy and helps strengthen Cisco firewall security.
Supported Devices
| Company | Devices | WELF Certified | Other log format |
|---|---|---|---|
| Cisco | Cisco Pix Secure Firewall v 6.x, 7.x |  | |
| Cisco ASA - Virtual Contexts supported |  | ||
| Cisco IOS 3005, 1900, 2911, 3925 |  | ||
| Cisco FWSM - Virtual Contexts supported |  | ||
| Cisco VPN Concentrator |  | ||
| Cisco CSC-SSM Module v6.3.x or higher |  | ||
| Cisco SSL WebVPN or SVC VPN |  | ||
| Cisco IronPort Proxy |  | ||
| Cisco Botnet module |  | ||
| Cisco Meraki |  | ||
| Cisco SourceFire |  |  |
Steps to Configure
For detailed steps on how to configure Firewall Anlayzer with your Cisco firewall appliance please refer to this link (here).
ManageEngine Cisco Firewall Analyzer tool offers a comprehensive solutions for gaining in-depth visibility into your cisco firewall management operations and greatly aids in dealing with complex firewall rules, assessing risky policies, ensuring compliance with industry standards and more.
Try our Cisco Firewall Analyzer with a free 30-day trial or sign up for a personalized demo to see the solution in action.
Featured links
Firewall Reports
Get a slew of security and traffic reports to asses the network security posture. Analyze the reports and take measures to prevent future security incidents. Monitor the Internet usage of enterprise users.
Firewall Compliance Management
Integrated compliance management system automates your firewall compliance audits. Ready made reports available for the major regulatory mandates such as PCI-DSS, ISO 27001, NIST, NERC-CIP, and SANS.
Firewall Rule Management
Manage your firewall rules for optimum performance. Anomaly free, properly ordered rules make your firewall secured. Audit the firewall security and manage the rule/config changes to strengthen the security.
Real-time Bandwidth Monitoring
With live bandwidth monitoring, you can identify the abnormal sudden shhot up of bandwidth use. Take remedial measures to contain the sudden surge in bandwidth consumption.
Firewall Alerts
Take instant remedial actions, when you get notified in real-time for network security incidents. Check and restrict Internet usage if banwidth exceeds specified threshold.
Manage Firewall Service
MSSPs can host multiple tenants, with exclusive segmented and secured access to their respective data. Scalable to address their needs. Manages firewalls deployed around the globe.