Staged Update Deployment Strategy
Table of contents
Agent updates are essential for staying ahead of emerging threats, improving detection capabilities and maintaining a strong security posture. Since NGAV operates at a deep system level, even small updates can affect endpoint behavior. To help you roll out these updates safely, a staged deployment model is used. Updates are deployed in controlled groups, known as rings.
By introducing updates in stages, any unexpected issues can be resolved early, minimizing risk exposure and ensuring the rollout remains stable as it reaches a wider set of endpoints.
Note: This staged rollout process applies to Malware Protection Plus, Ransomware Protection Plus and Malware Protection add-on in Endpoint Central.
Understanding the Ring Framework
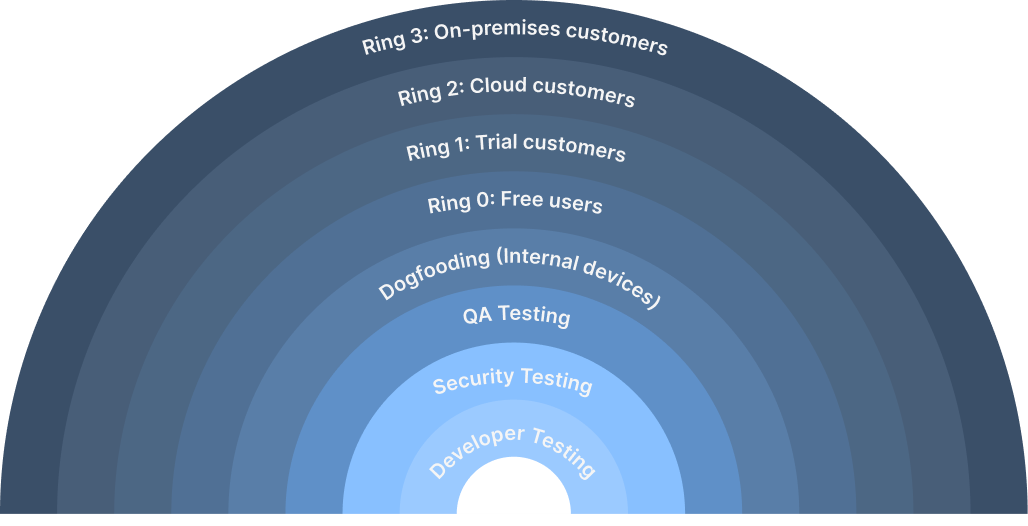
A ring-based rollout structure is used to ensure agent updates, definition updates and new feature releases are deployed safely. Each ring represents a defined group of customer environments that receive the update in a controlled, sequential order. The goal is to start with controlled groups, validate stability and then move confidently toward larger sets of endpoints.
Before entering the deployment rings, all updates undergo developer testing, security testing and QA testing to ensure that new features and fixes are stable and safe for customer environments. As a final internal validation step, updates undergo dogfooding to ensure they work as expected in real world before entering customer deployment rings.
After internal rings are validated, the rollout expands to customer environments in a staged manner. The updates move sequentially from free users and trial customers to cloud customers and finally to on-premises customers. Throughout the rollout, update performance is continuously monitored to enable rapid issue mitigation, including reverting or reissuing update packages when needed.
The ring model ensures that:
- Updates and new features are deployed safely with minimal risk
- Issues are detected early
- Roll-outs can be paused if any ring report unusual behavior
- Promotion to wider rings is based on tracked success metrics, not arbitrary schedules
- Trigger updates for a particular ring rather than all at once
Staged Agent Deployment
The staged deployment process ensures NGAV agent updates and new features are rolled out safely and predictably across all customer environments. This approach helps minimize risk, ensures consistent update behavior and maintains a reliable security posture across all endpoints.
- Updates are introduced in the ring framework. Each ring represents a specific group of endpoints or organizations.
- Server evaluates whether the endpoints meet the eligibility criteria for the current rollout stage.
- All eligible endpoints trigger the update and report success or failure status.
- The ring framework assesses the overall results within the current ring.
- If the success rate meet the defined threshold, the update progresses to next ring.
- If threshold is not met, the update is marked as failure and the rollout is halted.
- Only if the previous ring meets the success criteria does the update move to the next ring, where remaining endpoints reassess eligibility. Additionally, the engineering team monitors the health of the applications, and if any issue arise, the rollout is halted.
- This cycle continues until the update is successfully deployed to all endpoints across all rings or a failure condition stops the rollout.
Security Intelligence and Detection Updates
To stay ahead of emerging threats, the agent receives security intelligence and detection updates periodically. These updates ensure that the latest threat indicators, malware signatures, behavioral detection patterns and exploit techniques are continuously added to the detection engine.
Like feature and agent updates, security intelligence updates are deployed using the ring-based rollout framework described earlier. Updates begin with internal validation and then move sequentially through customer rings, provided each stage meets the defined success threshold. This ensures that updates are safely validated in controlled environments before reaching all endpoints, maintaining timely protection while minimizing the risk of unforeseen issues.
Controlled Update Deployment Options
In future releases, organizations will have the flexibility to defer update rollouts based on their internal policies or maintenance windows. Organizations can temporarily delay an update even when it becomes applicable to a specific ring. This deferral is allowed only for a limited period; once the update reaches the end of the ring framework, it will be applied automatically. While this provides flexibility, it is generally recommended to avoid delaying updates, as timely deployment of new features, security enhancements and detection improvements is essential for maintaining strong protection against emerging threats.




