Patch Management Architecture
Table of contents
The Patch Management Architecture
The Patch Management architecture consists of the following components:
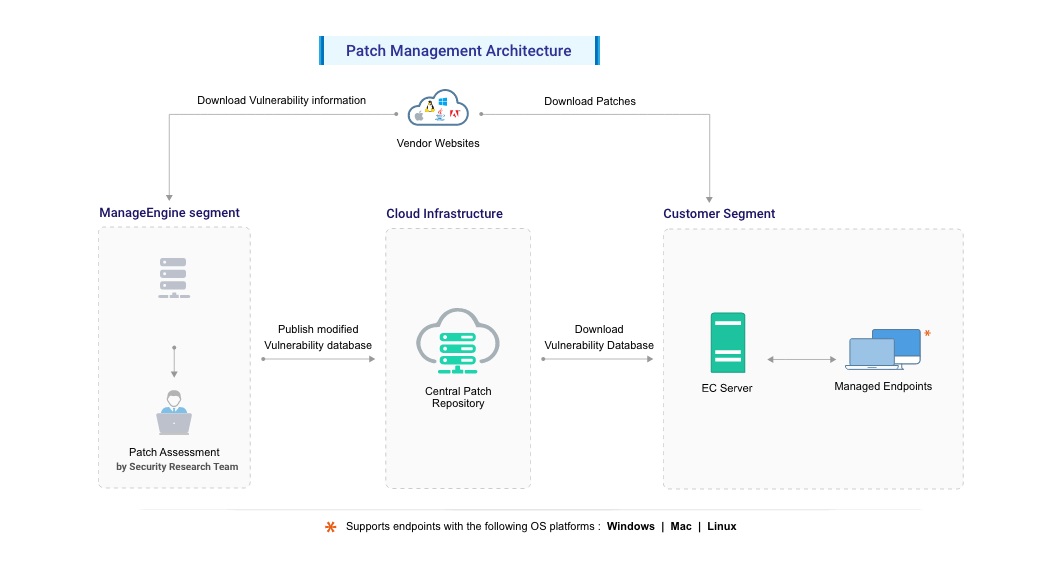
Fig: Patch Management Architecture
.....
To configure Patch Management, follow this link.
The Patch Management architecture consists of the following components:
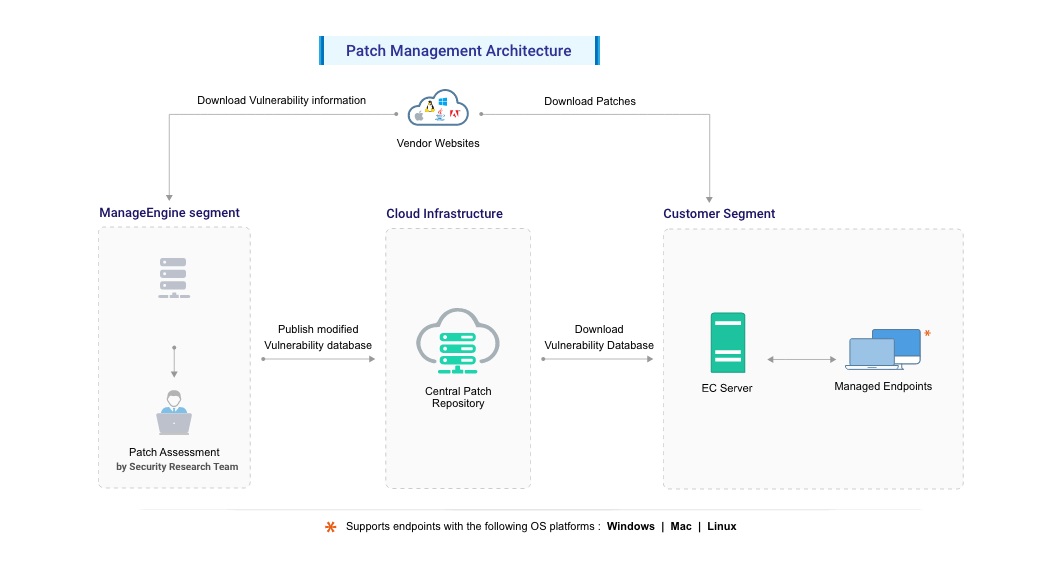
Fig: Patch Management Architecture
To configure Patch Management, follow this link.




