Configuring Security Policies
Table of Contents
- What are security policies>
- What are the default security policies offered by Endpoint Central?
- How to configure security policies?
What are security policies?
Security policies refer to a framework of restrictions that are imposed upon the users and computers in the network to ensure that they comply with the security guidelines set within the organization.
What are the default security policies offered by Endpoint Central?
The Security Policies configuration in Endpoint Central provides three default policies namely:
- System Security Policies
- System
- MMC Snap-ins
- Task Scheduler
- Windows Installer
- Control Panel
Browser Security Policies
- Internet Explorer
- Network
- Desktop Security Policies
- Desktop
- Active Desktop
To know more about the security policies offered by Endpoint Central, click here
How to configure security policies?
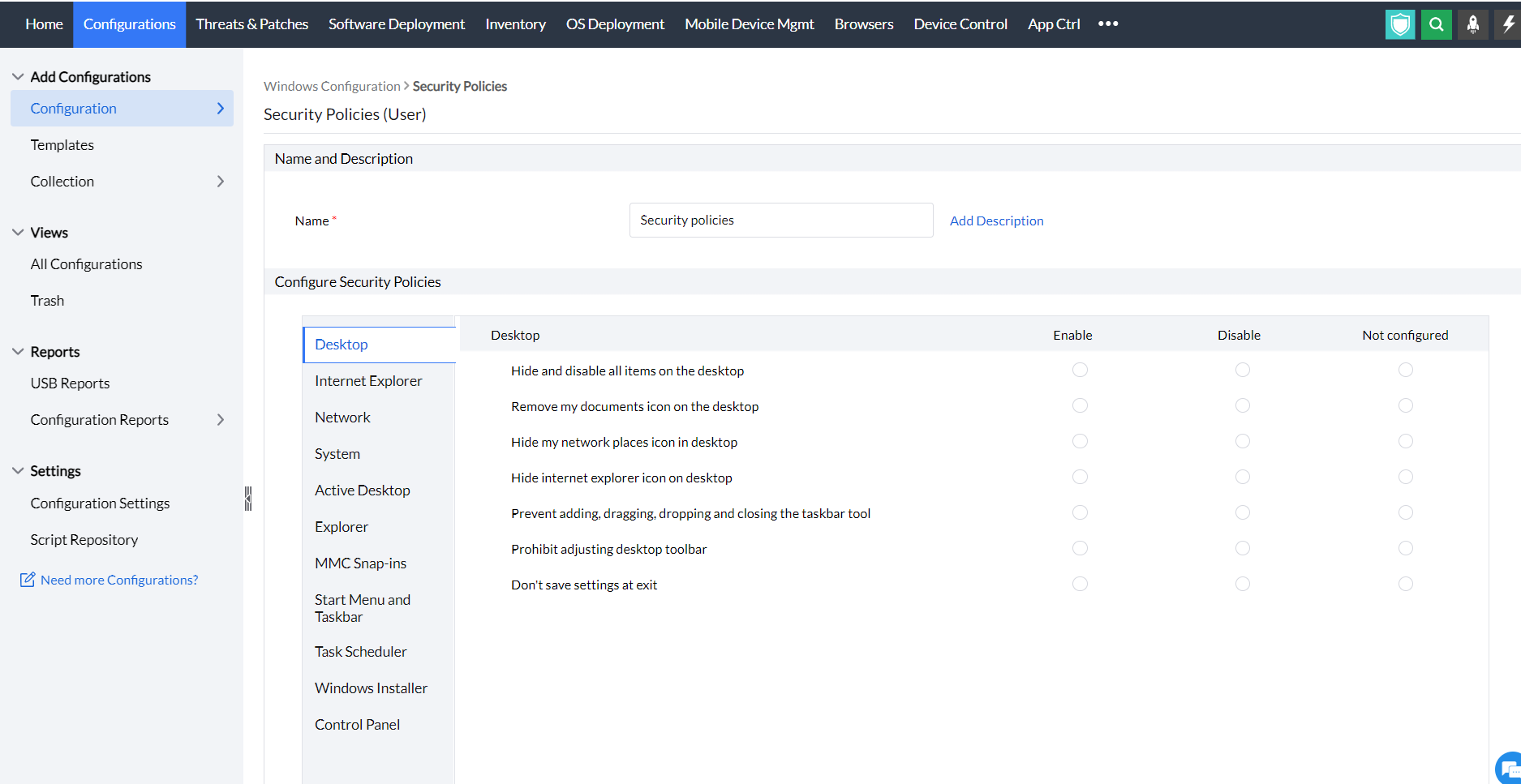
- In Endpoint Central Console, navigate to Configurations tab --> Add Configurations --> Configurations--> Windows
- Select Security Policies and choose User
- Specify the Name and Description for the configuration.
- In the configure security policies criteria, you have three options to enable, disable and not configure security policies for the default security policies.
- Define the Target
- Specify retry options if required and deploy the configuration.
- You can also enable notifications to receive emails based on the specified frequency.
- Click on the Deploy button to deploy the Security Policies configuration in all the targets.
- To save the configuration as draft, click Save as
You have successfully configured Security Policies for Windows machines




