Analyzing and reporting on FortiGate firewalls
As gatekeepers for all the traffic entering your network resources, firewalls play a crucial role in network security. Analyzing your firewall logs can help you detect and prevent possible cyberattacks in your organization network. With the help of a log analysis solution you can audit and manage your FortiGate firewalls easily and get real-time alerts on any suspicious network behavior.
Monitor and analyze firewall traffic using EventLog Analyzer
Your Fortinet firewall's intrusion prevention system monitors your network by logging events that seem suspicious. EventLog Analyzer completes the next step in that process by collecting and analyzing your FortiGate firewall logs in real time, generating reports and alerts so you can instantly identify threats and mitigate network attacks. EventLog Analyzer can also help ensure that only authorized personnel gain access to your network resources.
You can thoroughly track and analyze firewall traffic being allowed or denied based on the source, destination, port, protocol, and traffic trends to detect anomalous activity. For example, if EventLog Analyzer detects repeated denied connections by your firewall within a short period of time, you will be alerted in real time.
Configure alerts to be sent whenever suspicious events occur with EventLog Analyzer's predefined alert profiles for FortiGate firewalls. In addition to this, EventLog Analyzer's predefined incident response workflows can automatically take mitigating action to neutralize threats detected in your FortiGate firewall to keep your network safe and secure.
Stay on top of network threats with FortiGate log reports
EventLog Analyzer includes a wide range of predefined reports that provide actionable insights for your network security, including reports for antivirus solutions, applications servers, intrusion detection system (IDS) and intrusion protection system (IPS) devices, and more. That way, you can recognize attacks in your network instantly and audit them based on their source, destination, and severity.
What's more, the product also correlates the logs from all these devices, analyzes them, and identifies suspicious attack patterns in the events occurring across your network. (Related video: Identify remote, unauthorized software installations using event correlation.)
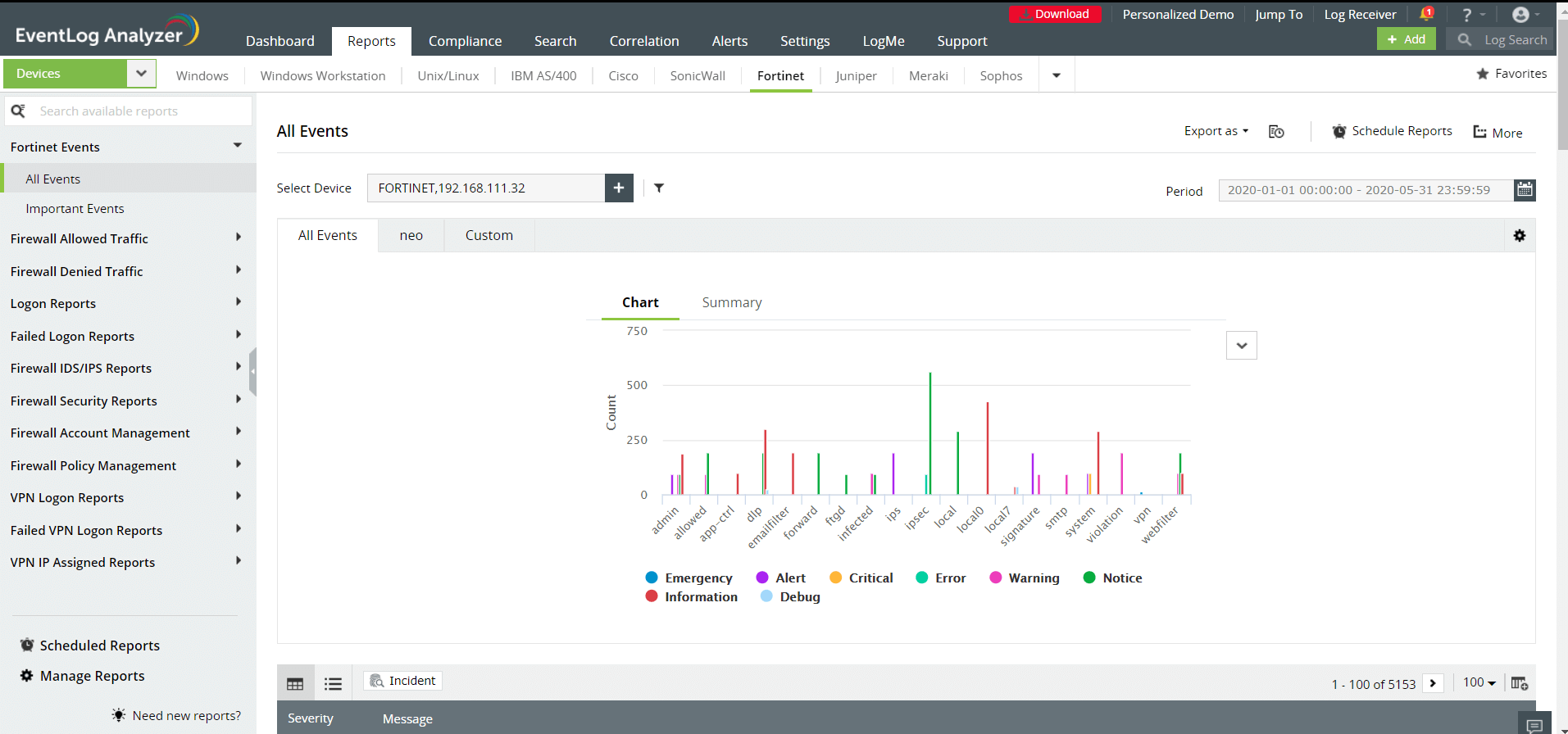
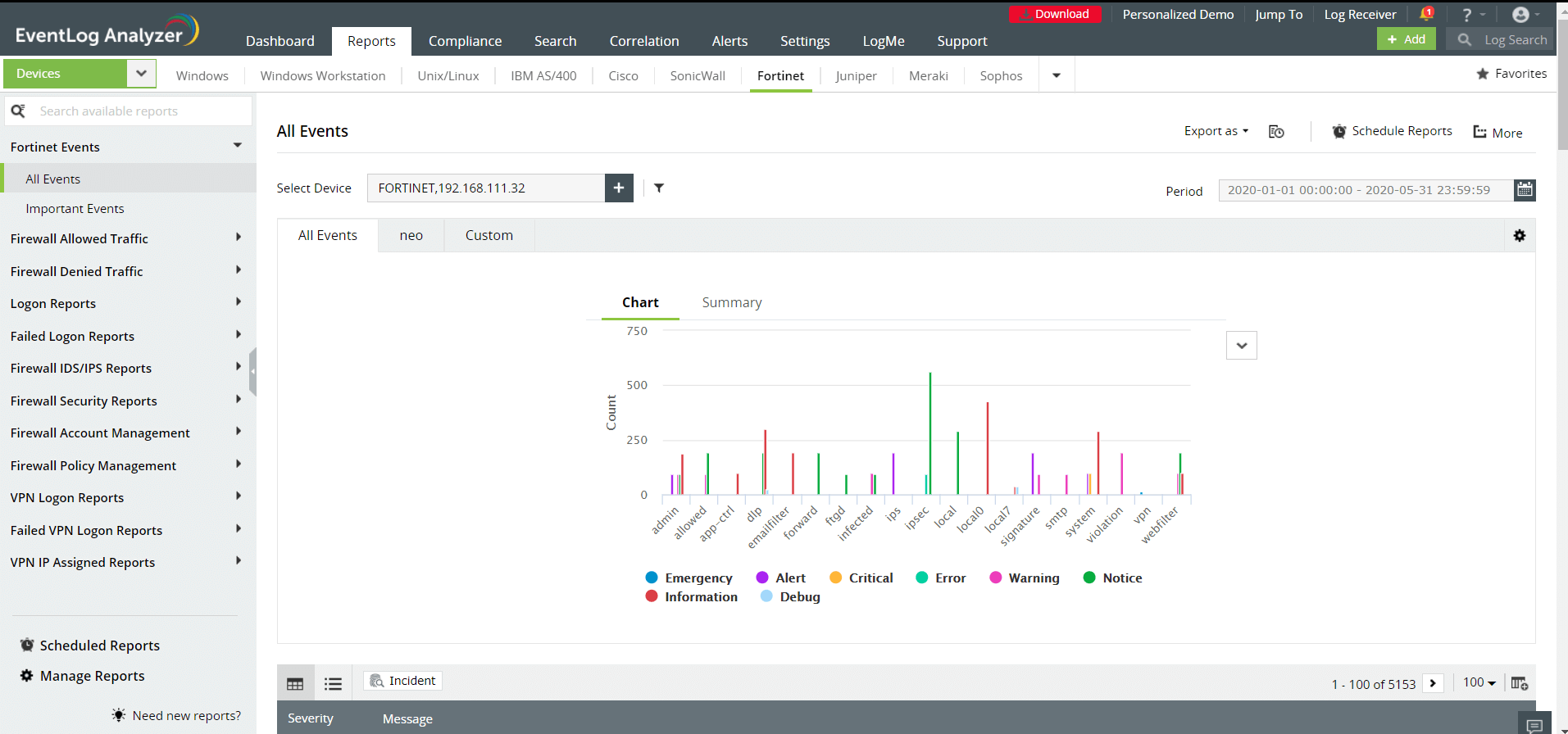
FortiGate firewall monitoring log reports
EventLog Analyzer provides the following reports for Fortinet devices:
- Fortinet Events
- Firewall Allowed Traffic
- Firewall Denied Traffic
- Logon Reports
- Failed Logon Reports
- Firewall IDS/IPS Reports
- Firewall Security Reports
- Firewall Account Management
- Firewall Policy Management
- VPN Logon Reports
- Failed VPN Logon Reports
- VPN IP Assigned Reports
- System Events
- Device Severity Reports
To learn more about EventLog Analyzer's FortiGate firewall reports, click here.
Using these log reports, you can find the source of a particular event, severity of the event, details about the traffic that has been allowed or denied, information regarding user logons, details of possible attacks, critical attacks and attack trends, web filtering reports, and more.
EventLog Analyzer has a powerful search function that can help you conduct a thorough forensic investigation of an incident with a range of advanced search options like Boolean, wildcard, range, and more . Whether you're scanning for network threats or responding to a security incident, EventLog Analyzer has you covered.