Every Linux system has multiple log files that store important events that happen on the device or network. Some of the most important files are:
- /var/log/auth.log - Stores the status of all authentication attempts, whether successful or not.
- /var/log/wtmp.log - Stores all login, logout, and reboot information.
- /var/log/lastlog.log - Stores the details of the last time each user on the system logged in.
You can manually analyze Linux logs by using a few commands to get the information you need in the bash command line. Some of the commands are:
- cd /var/log/ - Changes working directory to the folder mentioned.
- head -n 20 ex.log - Displays the first 20 lines of the file.
- tail -n 20 ex..log - Displays the last 20 lines of the file.
- grep "changed" ex.log (most used) - Searches for the string "changed" within the ex.log file and prints the lines that contain the string.
You can also take it one step further and use Python to create tools to automate and simplify log analysis.
Challenges in manual analysis
- It's a pretty boring and unnecessary job to do when you have a lot of other important things on your plate.
- It's easy to miss the important stuff.
- As your organization scales up, it can become difficult to manage the logs generated from hundreds of devices in the network.
- You can't know what's right or wrong at a glance due to the lack of visualization.
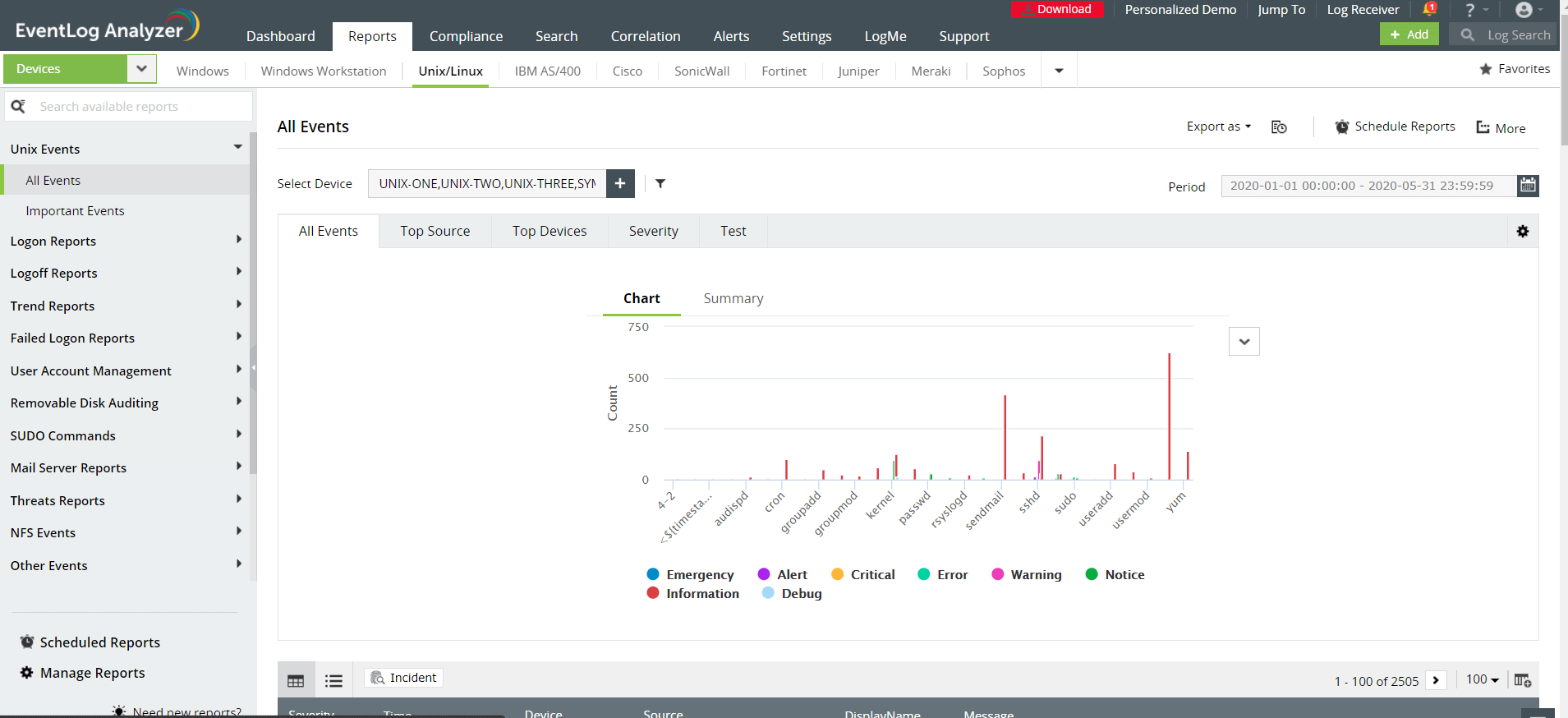
Analyzing Linux logs using EventLog Analyzer
Managing logs with EventLog Analyzer can fix all the above mentioned problems. Here are some of the capabilities that can help you:
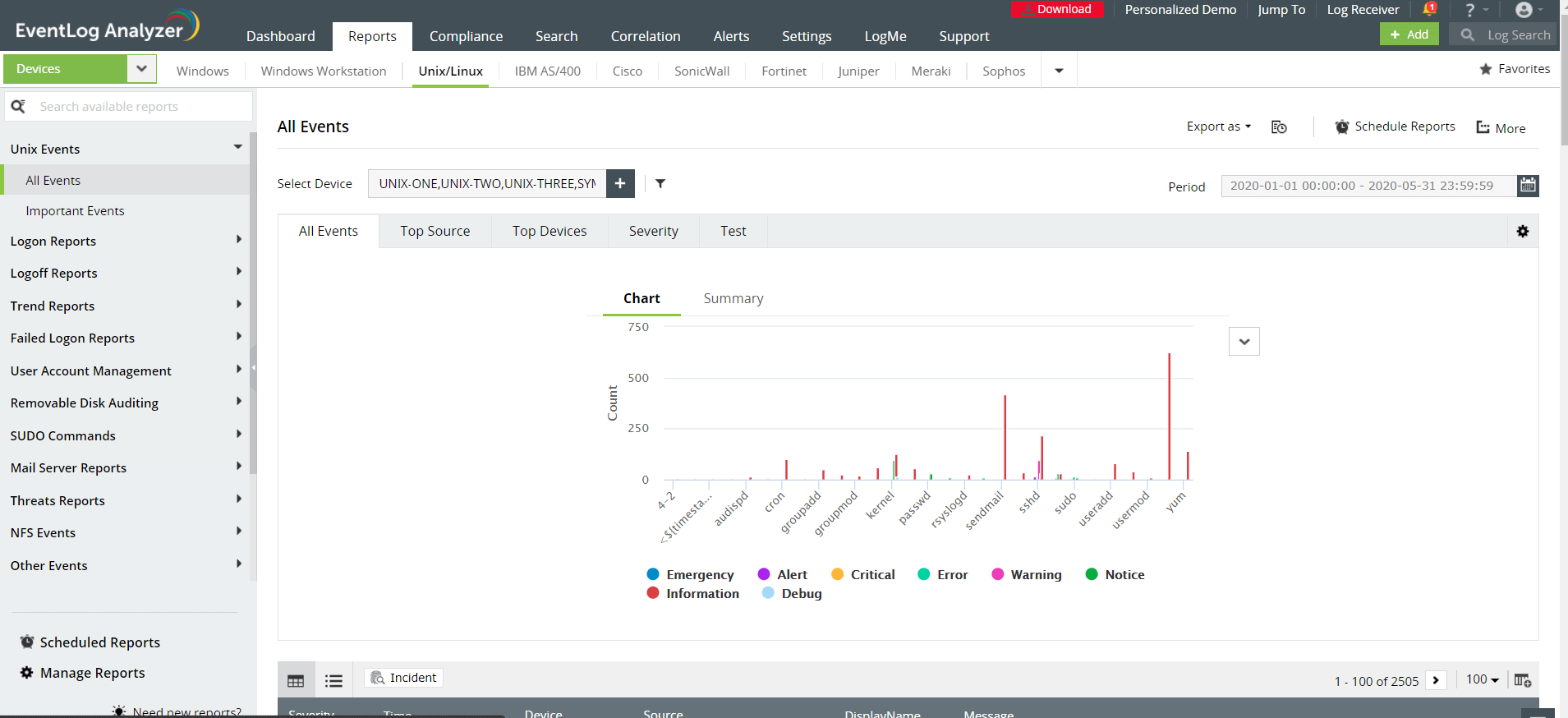
- Log collection and management for thousands of devices in your network.
- Complete control over Linux log management.
- Over 100 predefined Linux reports, including su command executions, FTP server events, user account management, and more.
- Intuitive dashboards for making quick decisions.
- Instant email or SMS notifications for critical events in real time.
- Customizable correlation rules to alert you when specific events happen in a sequence.
- Automated incident response to prevent further damage when a specific threat is detected.
Managing Linux logs is easier with EventLog Analyzer
EventLog Analyzer enables system administrators to centralize logs from multiple devices in the network. You can set up alerts to immediately get notified of any possible security threats. The built-in incident response system enables administrators to take immediate actions during a possible breach. View Linux logs in action.
To access the Linux device reports in the demo:
- Navigate to the Reports tab from the top navigation bar.
- Click on the Unix/Linux tab to open the Linux device reports.
- Choose the report you want to view from the left pane.
Other features
EventLog Analyzer collects and analyzes log data from Linux/Unix servers to provide on-the-fly reports that help detecting suspicious behaviors, anomalous syslog activities, and more.
Analyze application log from IIS and Apache web servers, Oracle & MS SQL databases, DHCP Windows and Linux applications and more. Mitigate application security attacks with reports & real-time alerts.
Monitor all types of log data from Active Directory infrastructure. Track failure incidents in real-time and build custom reports to monitor specific Active Directory events of your interest.
Monitor and track privileged user activities to meet PUMA requirements. Get out-of-the-box reports on critical activities such as logon failures, reason for logon failure, and more.
Monitor and audit print server with detailed reports on documents printed, attempts to print documents without proper permission, failed print jobs and their causes, and more
Comply with the stringent requirements of regulatory mandates viz., PCI DSS, FISMA, HIPAA, and more with predefined reports & alerts. Customize existing reports or build new reports to meet internal security needs.
Need Features? Tell Us
If you want to see additional features implemented in EventLog Analyzer, we would love to hear. Click here to continue