- Free Edition
- What's New?
- Key Highlights
- Suggested Reading
- All Capabilities
-
Log Management
- Event Log Management
- Syslog Management
- Log Collection
- Agent-less Log Collection
- Agent Based Log collection
- Windows Log Analysis
- Event Log Auditing
- Remote Log Management
- Cloud Log Management
- Security Log Management
- Server Log Management
- Linux Auditing and Reporting
- Auditing Syslog Devices
- Windows Registry Auditing
- Privileged User Activity Auditing
-
Application Log Management
- Application Log Monitoring
- Web Server Auditing
- Database Activity Monitoring
- Database Auditing
- IIS Log Analyzer
- Apache Log Analyzer
- SQL Database Auditing
- VMware Log Analyzer
- Hyper V Event Log Auditing
- MySQL Log Analyzer
- DHCP Server Auditing
- Oracle Database Auditing
- SQL Database Auditing
- IIS FTP Log Analyzer
- IIS Web Log Analyzer
- IIS Viewer
- IIS Log Parser
- Apache Log Viewer
- Apache Log Parser
- Oracle Database Auditing
-
IT Compliance Auditing
- ISO 27001 Compliance
- HIPAA Compliance
- PCI DSS Compliance
- SOX Compliance
- GDPR Compliance
- FISMA Compliance Audit
- GLBA Compliance Audit
- CCPA Compliance Audit
- Cyber Essentials Compliance Audit
- GPG Compliance Audit
- ISLP Compliance Audit
- FERPA Compliance Audit
- NERC Compliance Audit Reports
- PDPA Compliance Audit reports
- CMMC Compliance Audit
- Reports for New Regulatory Compliance
- Customizing Compliance Reports
-
Security Monitoring
- Threat Intelligence
- STIX/TAXII Feed Processor
- Threat Whitelisting
- Real-Time Event Correlation
- Log Forensics
- Incident Management System
- Automated Incident Response
- Linux File Integrity Monitoring
- Detecting Threats in Windows
- External Threat Mitigation
- Malwarebytes Threat Reports
- FireEye Threat Intelligence
- Application Log Management
- Security Information and Event Management (SIEM)
- Real-Time Event Alerts
- Privileged User Activity Auditing
-
Network Device Monitoring
- Network Device Monitoring
- Router Log Auditing
- Switch Log Monitoring
- Firewall Log Analyzer
- Cisco Logs Analyzer
- VPN Log Analyzer
- IDS/IPS Log Monitoring
- Solaris Device Auditing
- Monitoring User Activity in Routers
- Monitoring Router Traffic
- Arista Switch Log Monitoring
- Firewall Traffic Monitoring
- Windows Firewall Auditing
- SonicWall Log Analyzer
- H3C Firewall Auditing
- Barracuda Device Auditing
- Palo Alto Networks Firewall Auditing
- Juniper Device Auditing
- Fortinet Device Auditing
- pfSense Firewall Log Analyzer
- NetScreen Log Analysis
- WatchGuard Traffic Monitoring
- Check Point Device Auditing
- Sophos Log Monitoring
- Huawei Device Monitoring
- HP Log Analysis
- F5 Logs Monitoring
- Fortinet Log Analyzer
- Endpoint Log Management
- System and User Monitoring Reports
-
Log Management
- Product Resources
- Related Products
- Log360 (On-Premise | Cloud) Comprehensive SIEM and UEBA
- ADManager Plus Active Directory Management & Reporting
- ADAudit Plus Real-time Active Directory Auditing and UBA
- ADSelfService Plus Identity security with MFA, SSO, and SSPR
- DataSecurity Plus File server auditing & data discovery
- Exchange Reporter Plus Exchange Server Auditing & Reporting
- M365 Manager Plus Microsoft 365 Management & Reporting Tool
- RecoveryManager Plus Enterprise backup and recovery tool
- SharePoint Manager Plus SharePoint Reporting and Auditing
- AD360 Integrated Identity & Access Management
- AD Free Tools Active Directory FREE Tools
What is Cyber Essentials?
The UK government developed Cyber Essentials, a cybersecurity certification program, to aid organizations in safeguarding themselves against cyberthreats and demonstrating their dedication to cybersecurity. The compliance protects organizations by ensuring secure configuration, controlling user access, preventing malware, managing security updates, and using firewalls to block cyberthreats.
It applies to organizations of all sizes and sectors that aim to strengthen their cybersecurity measures and protect against common online threats
Related Content
- Compliance hub
- What is security compliance?
- What is a compliance audit?
- Risks of regulatory non-compliance
- Compliance management software
- Cyber essentials
Simplifying compliance management
- Collect, correlate, analyse, and archive logs from across the network and simplify log management with a unified view of log data.
- Analyse logs in real time, and automatically trigger alerts and notifications when critical events occur to detect and respond to security events promptly.
- Generate detailed and accurate compliance reports to demonstrate conformity to Cyber Essentials during audits and assessments.
Here's how EventLog Analyzer simplifies adherence to Cyber Essentials compliance
Privileged user monitoring
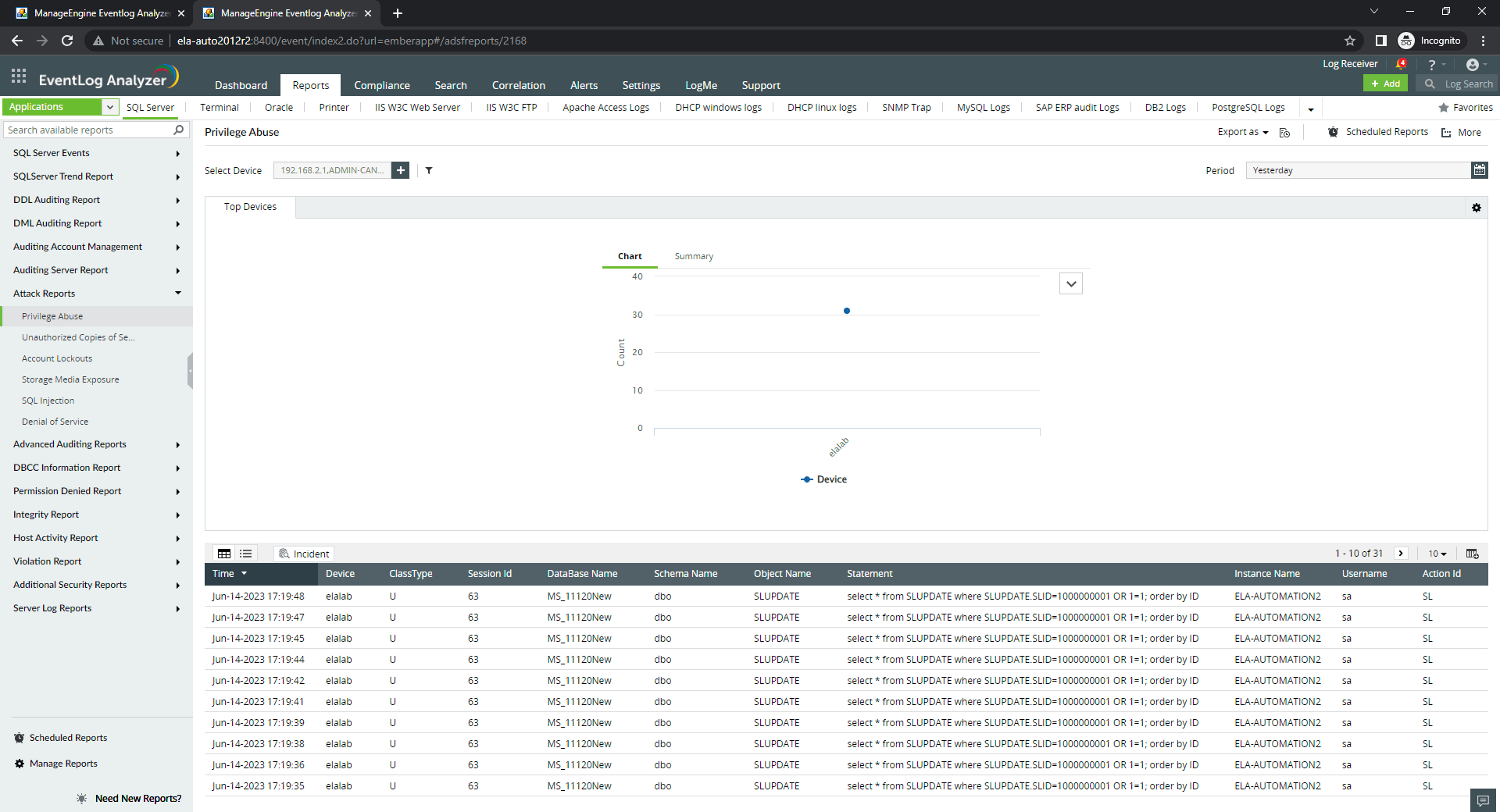
Monitor the activities performed by users with elevated access privileges. By tracking and auditing the actions performed by privileged users, you can detect and respond to misuse of privileged accounts, reduce the risk of data breaches, and provide evidence of compliance with various regulatory standards, including Cyber Essentials requirements for privileged user monitoring and access control.
Account lockout monitoring
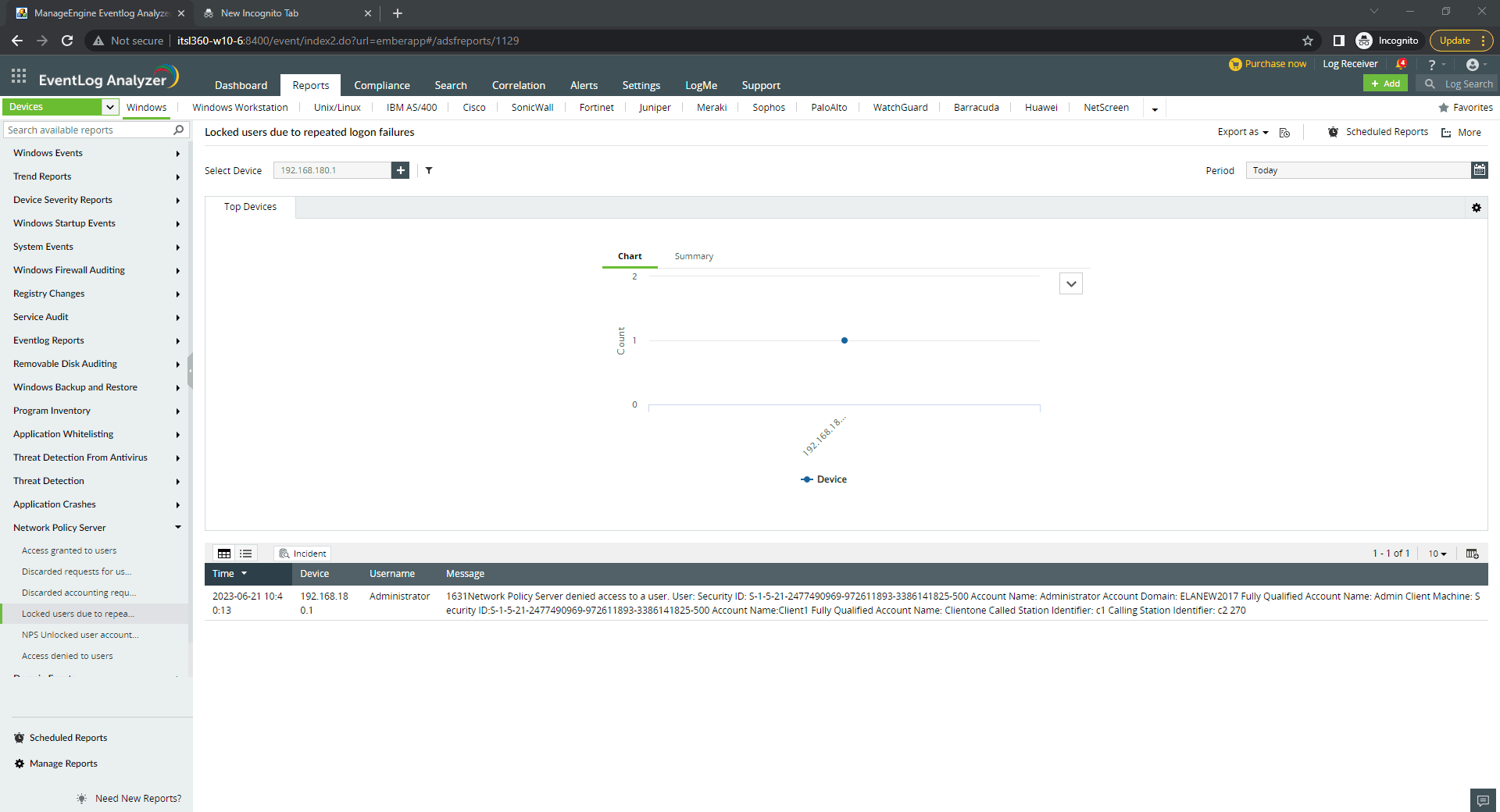
Monitor and capture account lockout events, which occur when a user's account is locked out after multiple failed login attempts. By tracking account lockouts and providing real-time alerts, EventLog Analyzer helps you to identify potential security threats like brute-force attacks, account compromise, denial of service (DoS), or unauthorized access attempts. This feature monitors user sessions and allows you to address account lockouts and helps you meet Section D.2 of Cyber Essentials requirements for account lockout and password policy management.
Vulnerability assessment and remediation
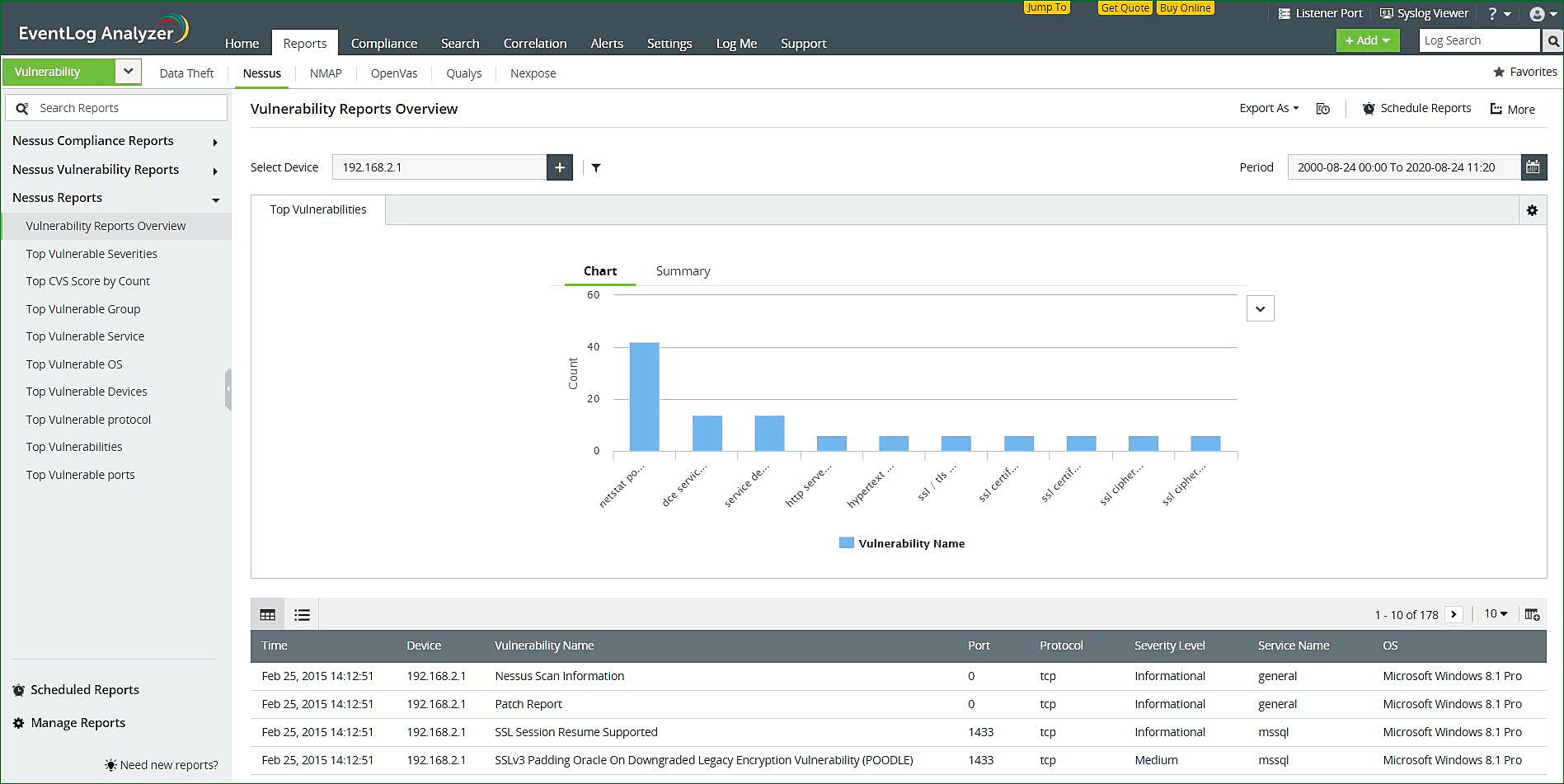
Identify and prioritise security vulnerabilities across your network with EventLog Analyzer's sophisticated vulnerability assessment capabilities. It can process log data from vulnerability scanners such as Nessus, Qualys, OpenVAS, and NMAP and deliver actionable reports to begin remediation efforts. The data from the vulnerability scanners can be fed into the correlation engine to discover complex attack patterns.
You can meet the Cyber Essentials patch management requirements of Section D.3 for vulnerability management and risk reduction. With EventLog Analyzer's comprehensive vulnerability assessment solution, organizations can reduce security risks and maintain a secure environment.
Incident response automation
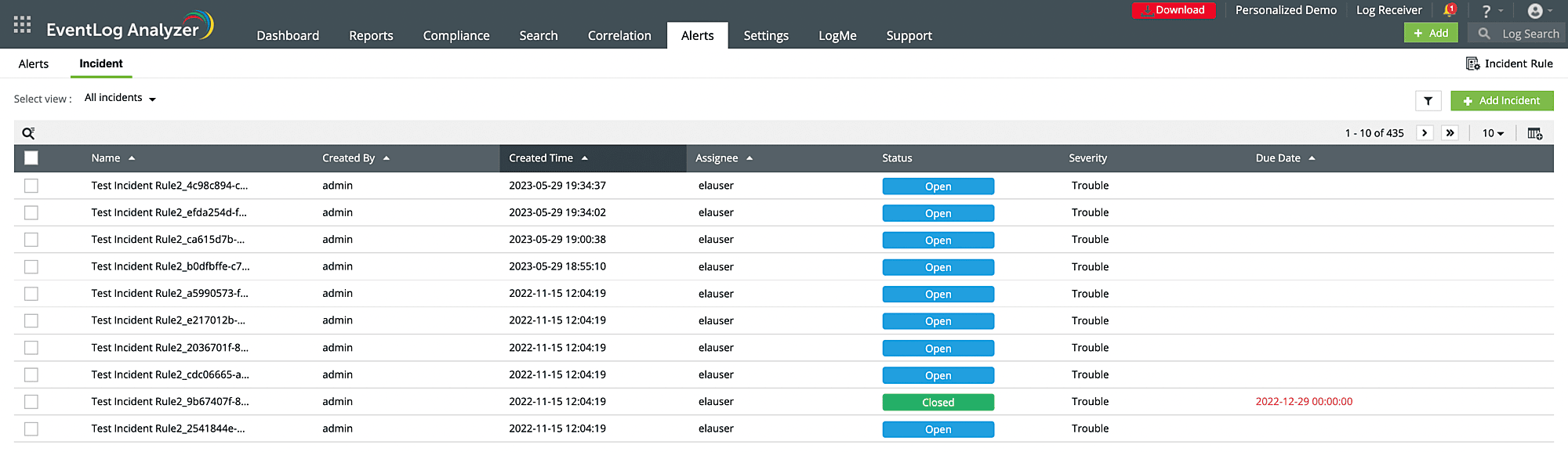
Streamline incident handling processes, reduce response times, and ensure consistent and effective incident response practices with the incident response automation feature. This feature allows you to facilitate swift and coordinated responses to security incidents. It can raise a ticket to the concerned security teams in real time for quick analysis and action. EventLog Analyzer helps organizations meet the Cyber Essentials requirements of Section D.4 for user access control by automating your first response to any security incident with predefined workflows and automated response actions triggered by preset criteria.
How does EventLog Analyzer meet Cyber Essentials requirements?
| Cyber Essentials requirements | Requirement description | EventLog Analyzer reports |
|---|---|---|
| D.1 Boundary firewalls and internet gateways | Organizations should protect every device in scope with a correctly configured firewall (or network device with firewall functionality). |
|
| D.2 Secure Configuration | Proper configuration of computers and network devices should be carried out to minimize inherent vulnerabilities and ensure that only the services needed to carry out their designated tasks are available. |
|
| D.3 Patch Managaement | Maintain the latest security patches and updates on the software utilised on computers and network devices. |
|
| D.4 User access control | Authorized individuals should be the only ones assigned user accounts, especially those with special access privileges, like administrative accounts, and effective management should be implemented to prevent the misuse of such privileges. |
|
| D.5 Malware Protection | The use of malware protection software is necessary to safeguard computers in an organization that are connected to the internet, and it is essential to implement strong malware protection measures on these devices. |
|
What else does EventLog Analyzer offer?
Log collection and consolidation
Collect and consolidate log data from various sources, such as servers, applications, and network devices. This allows you to centralise your log data in a single platform, making it easier to search, analyse, and monitor logs for troubleshooting.
Threat intelligence
Identify and respond to emerging threats instantly with threat intelligence feeds that provide real-time information about known malicious entities, IP addresses, domains, and indicators of compromise (IOCs).
Cloud infrastructure monitoring
Monitor all AWS EC2 instances in real time, and detect suspicious activities with timely alerts, enhancing the network security of your system.
Log forensics and investigation
Investigate security event with EventLog Analyzer's powerful search, log correlation, and log visualisation capabilities. It allows security teams to reconstruct incidents, trace activities, and identify the root cause of security breaches or system failures.
Frequently asked questions
Cyber Essentials compliance applies to organizations of all sizes and sectors that aim to strengthen their cybersecurity measures and protect against common online threats. The scheme applies to businesses, non-profit organizations, and government entities in the United Kingdom and beyond.
Cyber Essentials is not mandatory for businesses, but organizations that work with the UK government and organizations that bid for government contracts are required to be compliant with Cyber Essentials.











