- Free Edition
- What's New?
- Key Highlights
- Suggested Reading
- All Capabilities
-
Log Management
- Event Log Management
- Syslog Management
- Log Collection
- Agent-less Log Collection
- Agent Based Log collection
- Windows Log Analysis
- Event Log Auditing
- Remote Log Management
- Cloud Log Management
- Security Log Management
- Server Log Management
- Linux Auditing and Reporting
- Auditing Syslog Devices
- Windows Registry Auditing
- Privileged User Activity Auditing
-
Application Log Management
- Application Log Monitoring
- Web Server Auditing
- Database Activity Monitoring
- Database Auditing
- IIS Log Analyzer
- Apache Log Analyzer
- SQL Database Auditing
- VMware Log Analyzer
- Hyper V Event Log Auditing
- MySQL Log Analyzer
- DHCP Server Auditing
- Oracle Database Auditing
- SQL Database Auditing
- IIS FTP Log Analyzer
- IIS Web Log Analyzer
- IIS Viewer
- IIS Log Parser
- Apache Log Viewer
- Apache Log Parser
- Oracle Database Auditing
-
IT Compliance Auditing
- ISO 27001 Compliance
- HIPAA Compliance
- PCI DSS Compliance
- SOX Compliance
- GDPR Compliance
- FISMA Compliance Audit
- GLBA Compliance Audit
- CCPA Compliance Audit
- Cyber Essentials Compliance Audit
- GPG Compliance Audit
- ISLP Compliance Audit
- FERPA Compliance Audit
- NERC Compliance Audit Reports
- PDPA Compliance Audit reports
- CMMC Compliance Audit
- Reports for New Regulatory Compliance
- Customizing Compliance Reports
-
Security Monitoring
- Threat Intelligence
- STIX/TAXII Feed Processor
- Threat Whitelisting
- Real-Time Event Correlation
- Log Forensics
- Incident Management System
- Automated Incident Response
- Linux File Integrity Monitoring
- Detecting Threats in Windows
- External Threat Mitigation
- Malwarebytes Threat Reports
- FireEye Threat Intelligence
- Application Log Management
- Security Information and Event Management (SIEM)
- Real-Time Event Alerts
- Privileged User Activity Auditing
-
Network Device Monitoring
- Network Device Monitoring
- Router Log Auditing
- Switch Log Monitoring
- Firewall Log Analyzer
- Cisco Logs Analyzer
- VPN Log Analyzer
- IDS/IPS Log Monitoring
- Solaris Device Auditing
- Monitoring User Activity in Routers
- Monitoring Router Traffic
- Arista Switch Log Monitoring
- Firewall Traffic Monitoring
- Windows Firewall Auditing
- SonicWall Log Analyzer
- H3C Firewall Auditing
- Barracuda Device Auditing
- Palo Alto Networks Firewall Auditing
- Juniper Device Auditing
- Fortinet Device Auditing
- pfSense Firewall Log Analyzer
- NetScreen Log Analysis
- WatchGuard Traffic Monitoring
- Check Point Device Auditing
- Sophos Log Monitoring
- Huawei Device Monitoring
- HP Log Analysis
- F5 Logs Monitoring
- Fortinet Log Analyzer
- Endpoint Log Management
- System and User Monitoring Reports
-
Log Management
- Product Resources
- Related Products
- Log360 (On-Premise | Cloud) Comprehensive SIEM and UEBA
- ADManager Plus Active Directory Management & Reporting
- ADAudit Plus Real-time Active Directory Auditing and UBA
- ADSelfService Plus Identity security with MFA, SSO, and SSPR
- DataSecurity Plus File server auditing & data discovery
- Exchange Reporter Plus Exchange Server Auditing & Reporting
- M365 Manager Plus Microsoft 365 Management & Reporting Tool
- RecoveryManager Plus Enterprise backup and recovery tool
- SharePoint Manager Plus SharePoint Reporting and Auditing
- AD360 Integrated Identity & Access Management
- AD Free Tools Active Directory FREE Tools
Firewalls are an important line of defense against malicious attack attempts on an organization's network. By blocking various attack types, firewalls allow network communications to continue seamlessly. But it is also important to take stock and understand what attacks are attempted on a network and who is trying to disrupt the network. This can be done by auditing security logs, which provide information on all attack attempts and aid in security-related decision making. EventLog Analyzer helps organizations efficiently audit security logs and take steps to improve network security.
Since Palo Alto Networks firewalls are equipped to deal with specific attack types, auditing their security logs provides detailed information about these attacks. Some scenarios in which auditing Palo Alto Networks security logs are useful include:
- When users need to identify highly targeted devices that are attacked repeatedly. This may necessitate tightening security measures for the host, such as encrypting the host data, or backing up device data more frequently.
- When users need to extract information about specific attack attempts. For instance, admins can identify a denial of service attack, where the attacker tries to flood a server with requests, and block the source from future attack attempts.
- When users need to review threats detected by the Palo Alto Networks Wildfire environment to discover and keep pace with the latest threats.
- When users need to monitor which blocked sites employees are attempting to access using URL filtering logs.
- When users need to identify trends to develop a deeper understanding of the pattern of attacks that an organization faces.
Palo Alto Networks firewall security auditing reports
Two groups of security auditing reports are available: system event reports and threat reports. System event reports detail the various software packages that are installed or upgraded on the firewall.
Threat reports provide information regarding various security-related dangers to the network. Specifically, threat reports include:
- An overview report that presents a summary of the various threats averted.
- A trend report that describes threat trends over time.
- Top N reports, which identify the source or destination devices which are the most frequent cause (or target) of attacks.
- Various threat-specific security reports, namely: flood attack detection, spyware download detection, Wildfire signature feed, and vulnerability exploit detection.
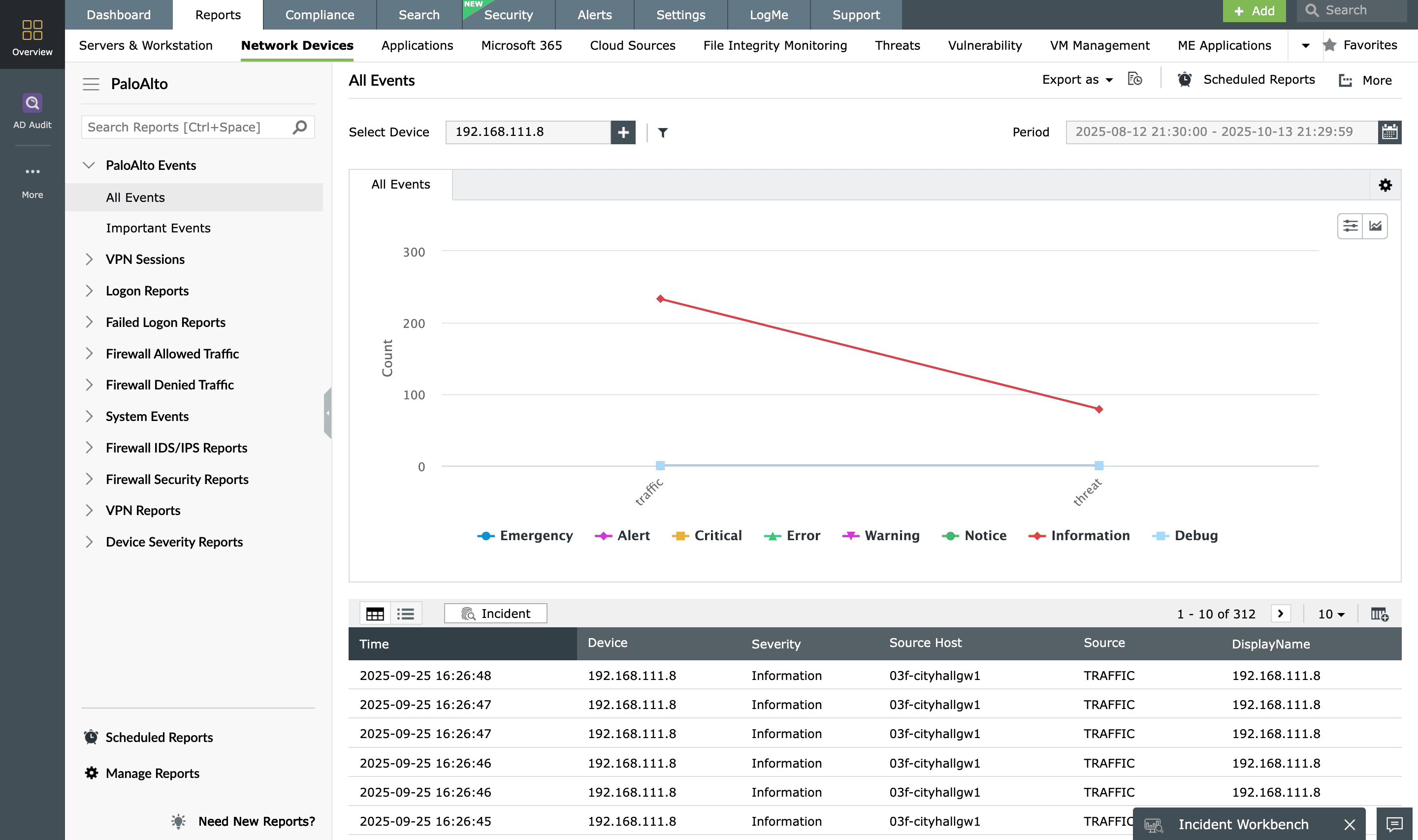
Available Reports
Package Installed | Package Upgraded | Possible Attacks | Critical Attacks | Top Attacks based on Source | Top Attacks based on Destination | Attacks Trend Scan Detection | Flood Detection | URL Filtering Log | Spyware Phone Home Detection | Spyware Download Detection | Vulnerability Exploit Detection | Filetype Detection | Data Filtering Detection | Virus Detection | Wildfire Signature Feed | DNS Botnet Signatures
EventLog Analyzer efficiently analyzes, reports, and alerts on Palo Alto Networks security logs, ensuring that no attack attempts are missed and the network is constantly protected.











