- Free Edition
- What's New?
- Key Highlights
- Suggested Reading
- All Capabilities
-
Log Management
- Event Log Management
- Syslog Management
- Log Collection
- Agent-less Log Collection
- Agent Based Log collection
- Windows Log Analysis
- Event Log Auditing
- Remote Log Management
- Cloud Log Management
- Security Log Management
- Server Log Management
- Linux Auditing and Reporting
- Auditing Syslog Devices
- Windows Registry Auditing
- Privileged User Activity Auditing
-
Application Log Management
- Application Log Monitoring
- Web Server Auditing
- Database Activity Monitoring
- Database Auditing
- IIS Log Analyzer
- Apache Log Analyzer
- SQL Database Auditing
- VMware Log Analyzer
- Hyper V Event Log Auditing
- MySQL Log Analyzer
- DHCP Server Auditing
- Oracle Database Auditing
- SQL Database Auditing
- IIS FTP Log Analyzer
- IIS Web Log Analyzer
- IIS Viewer
- IIS Log Parser
- Apache Log Viewer
- Apache Log Parser
- Oracle Database Auditing
-
IT Compliance Auditing
- ISO 27001 Compliance
- HIPAA Compliance
- PCI DSS Compliance
- SOX Compliance
- GDPR Compliance
- FISMA Compliance Audit
- GLBA Compliance Audit
- CCPA Compliance Audit
- Cyber Essentials Compliance Audit
- GPG Compliance Audit
- ISLP Compliance Audit
- FERPA Compliance Audit
- NERC Compliance Audit Reports
- PDPA Compliance Audit reports
- CMMC Compliance Audit
- Reports for New Regulatory Compliance
- Customizing Compliance Reports
-
Security Monitoring
- Threat Intelligence
- STIX/TAXII Feed Processor
- Threat Whitelisting
- Real-Time Event Correlation
- Log Forensics
- Incident Management System
- Automated Incident Response
- Linux File Integrity Monitoring
- Detecting Threats in Windows
- External Threat Mitigation
- Malwarebytes Threat Reports
- FireEye Threat Intelligence
- Application Log Management
- Security Information and Event Management (SIEM)
- Real-Time Event Alerts
- Privileged User Activity Auditing
-
Network Device Monitoring
- Network Device Monitoring
- Router Log Auditing
- Switch Log Monitoring
- Firewall Log Analyzer
- Cisco Logs Analyzer
- VPN Log Analyzer
- IDS/IPS Log Monitoring
- Solaris Device Auditing
- Monitoring User Activity in Routers
- Monitoring Router Traffic
- Arista Switch Log Monitoring
- Firewall Traffic Monitoring
- Windows Firewall Auditing
- SonicWall Log Analyzer
- H3C Firewall Auditing
- Barracuda Device Auditing
- Palo Alto Networks Firewall Auditing
- Juniper Device Auditing
- Fortinet Device Auditing
- pfSense Firewall Log Analyzer
- NetScreen Log Analysis
- WatchGuard Traffic Monitoring
- Check Point Device Auditing
- Sophos Log Monitoring
- Huawei Device Monitoring
- HP Log Analysis
- F5 Logs Monitoring
- Fortinet Log Analyzer
- Endpoint Log Management
- System and User Monitoring Reports
-
Log Management
- Product Resources
- Related Products
- Log360 (On-Premise | Cloud) Comprehensive SIEM and UEBA
- ADManager Plus Active Directory Management & Reporting
- ADAudit Plus Real-time Active Directory Auditing and UBA
- ADSelfService Plus Identity security with MFA, SSO, and SSPR
- DataSecurity Plus File server auditing & data discovery
- Exchange Reporter Plus Exchange Server Auditing & Reporting
- M365 Manager Plus Microsoft 365 Management & Reporting Tool
- RecoveryManager Plus Enterprise backup and recovery tool
- SharePoint Manager Plus SharePoint Reporting and Auditing
- AD360 Integrated Identity & Access Management
- AD Free Tools Active Directory FREE Tools
What is PDPA compliance?
The Philippines Data Privacy Act (PDPA) is a privacy law that aims to protect the personal information of the public. This compliance regulation requires organizations that handle the personal data of Filipino citizens to maintain secure systems for storing and managing it. ManageEngine EventLog Analyzer, a comprehensive log management and IT compliance management solution, can help you protect the personal data your organization holds and easily meet PDPA requirements.
This PDPA compliance tool helps organizations meet PDPA requirements by detecting security threats, data breach attempts, and unauthorized or unwanted modifications to personal data. Read on to learn more about how EventLog Analyzer's features can be leveraged to meet compliance requirements easily.
Related Content
- Compliance hub
- What is security compliance?
- What is a compliance audit?
- Risks of regulatory non-compliance
- Compliance management software
Become PDPA-compliant with EventLog Analyzer
Audit user sessions
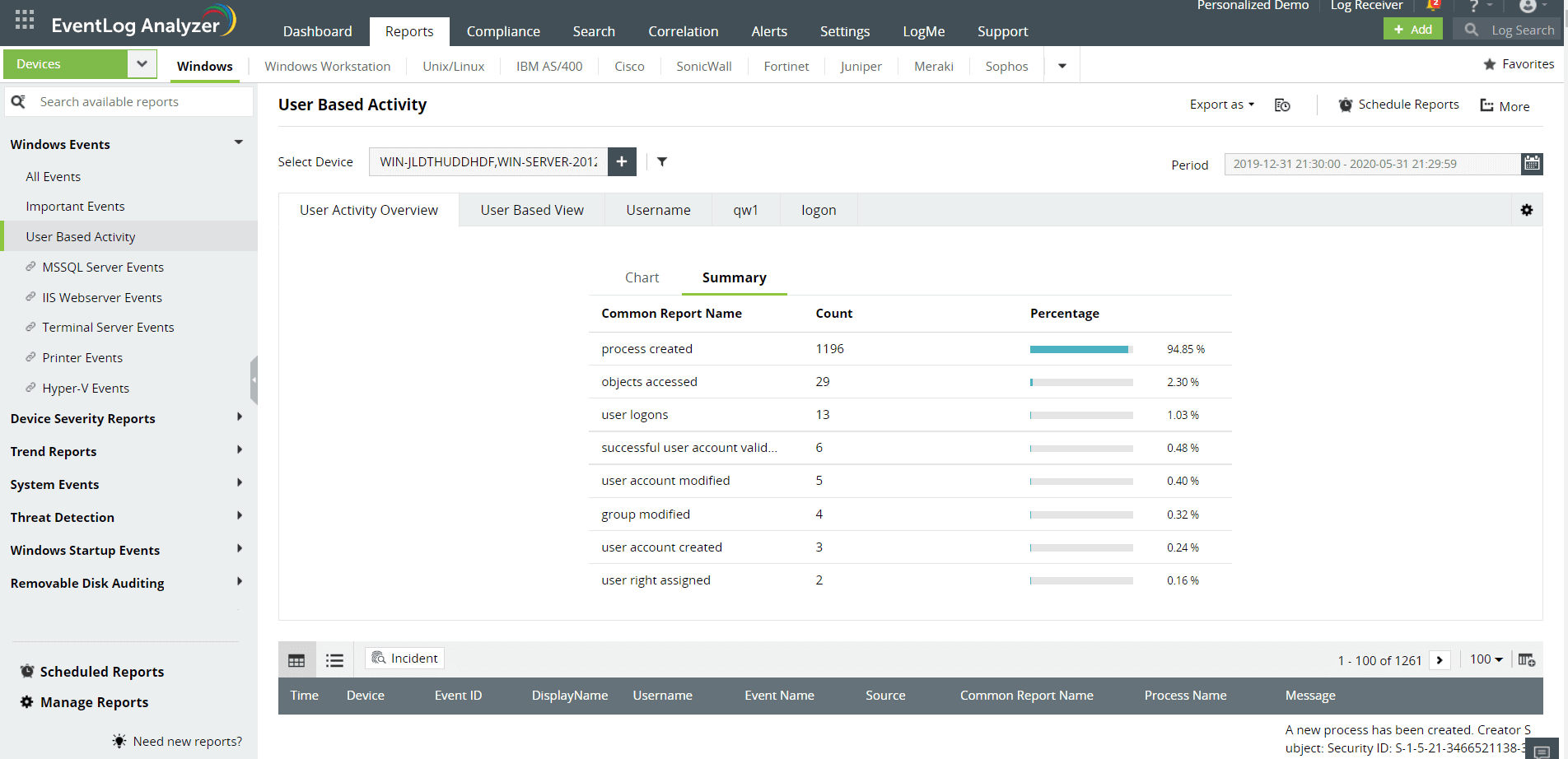
The PDPA mandates the protection of personal information stored and processed by organizations. To ensure personal information security, you need to monitor the user activity in the systems where your data is stored. EventLog Analyzer helps satisfy this requirement with its continuous user session and activity monitoring. It monitors every user action, analyzing the deviations or anomalies in user behaviors to detect any compromise of personal information.
This IT compliance solution creates exhaustive user audit trails and provides precise information on user logons and logoffs, audit policy changes, accessed objects, user account changes, and successful audit log clearance. These reports will help you determine if the personal information is secured or compromised.
Monitor file integrity
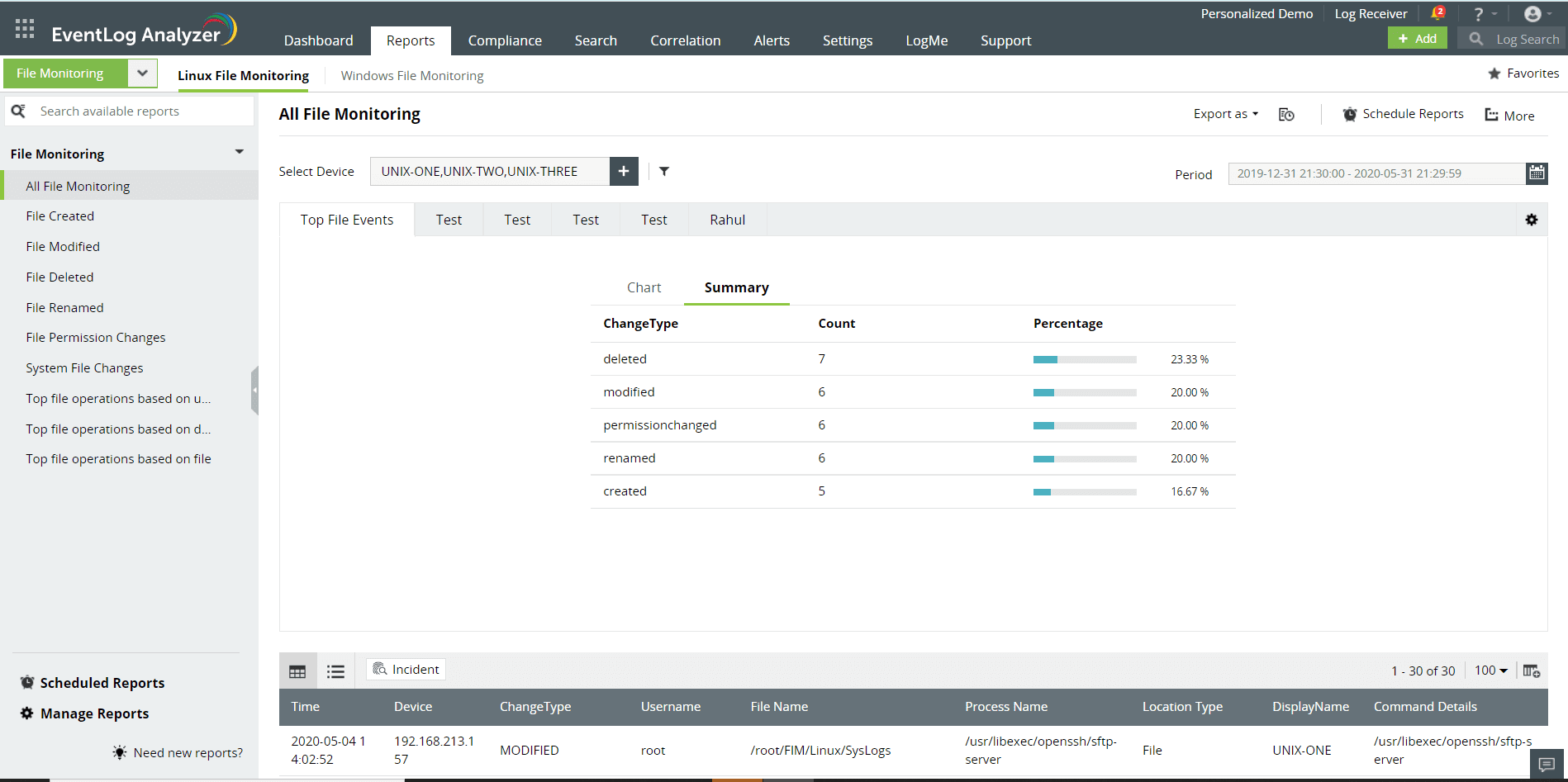
Ensuring the integrity of stored personal information is a critical requirement of the PDPA. With EventLog Analyzer's file integrity monitoring feature, understand who accessed personal information, what operations were performed on it (file modifications), from where, and how. This visibility helps you ensure the integrity of the stored personal information. Additionally, you get notified when critical changes take place in sensitive files and folders.
This solution ensures total file integrity by scanning each file's attributes, ownership, permissions, and size. It also provides complete disclosure to identify the source, hostname, time, and location for all anomalous file events.
Manage database logs
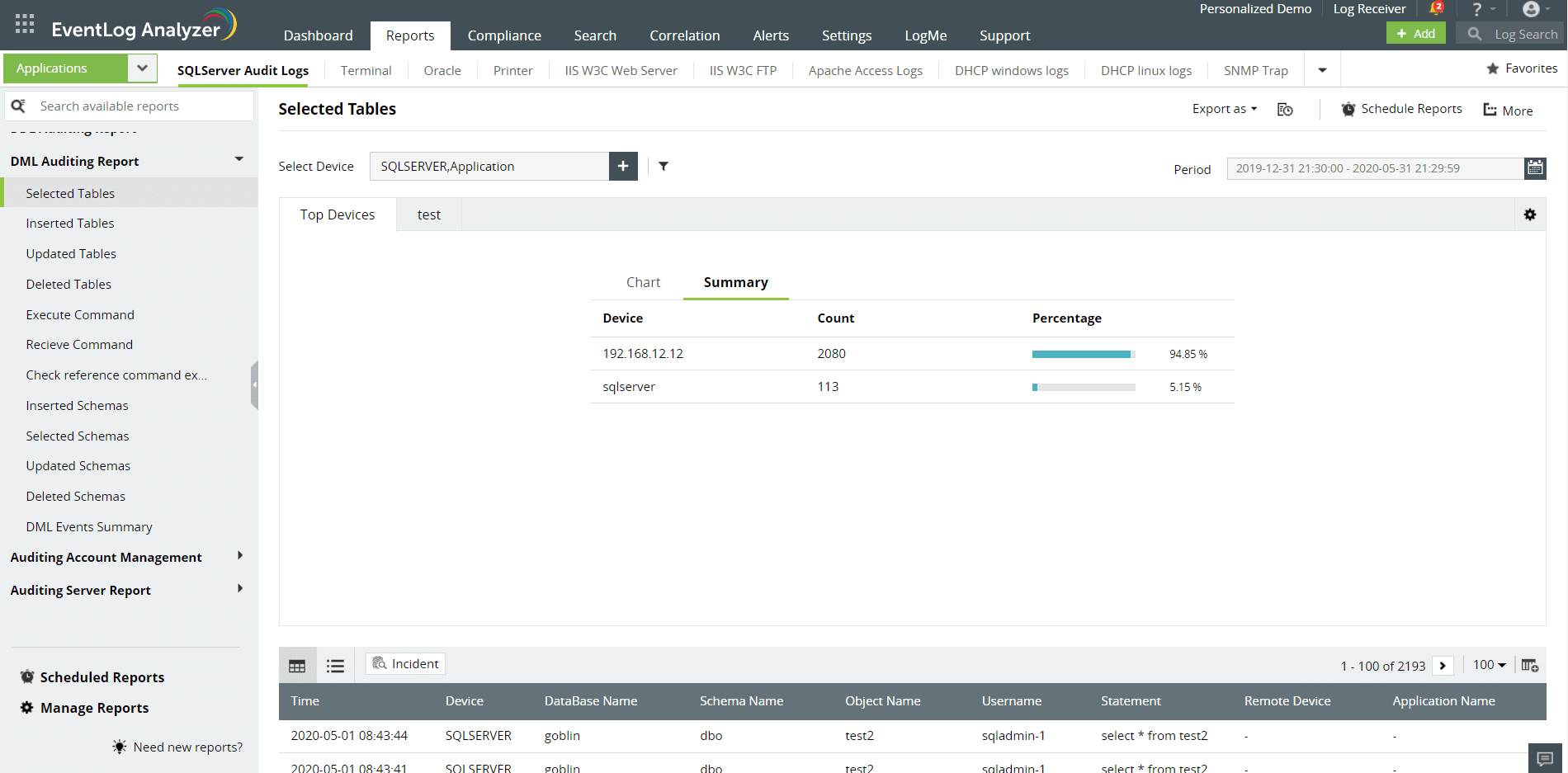
Auditing database logs helps you understand attempts to access and modify the sensitive data stored in the database, which is important to satisfy the PDPA's data protection requirements. EventLog Analyzer's database and activity monitoring provides a complete audit trail to help you detect unauthorized access to confidential data.
EventLog Analyzer monitors user activity, database transactions, account management, server security, and more. You can also identify common attack patterns like injection attacks or denial-of-service attacks with a powerful correlation engine that correlates network activities.
Detect privilege abuse
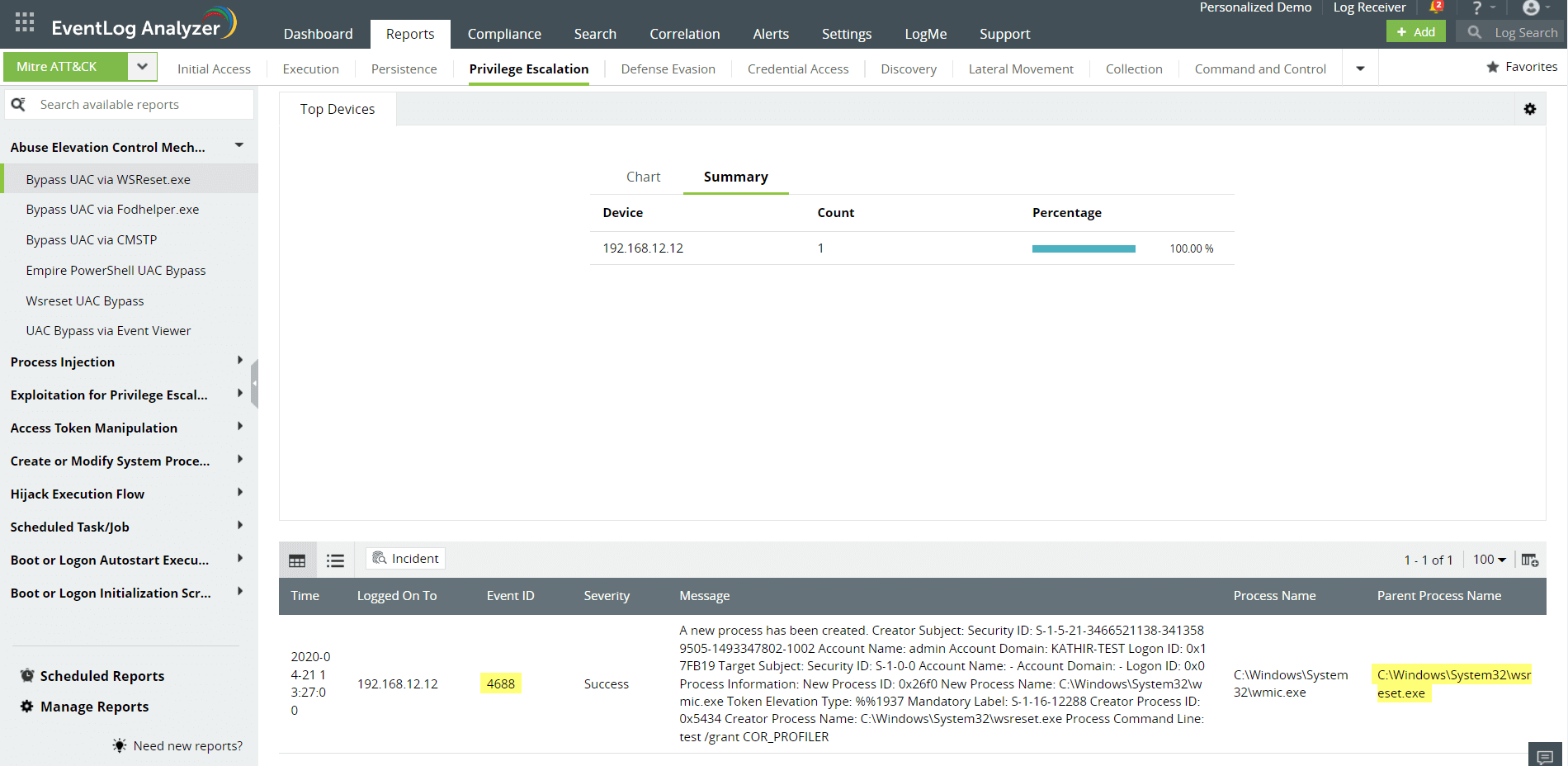
The privileged users in any network have enhanced access to protected data, systems, and applications. Monitor privileged user activity and detect privilege abuse and identity theft with EventLog Analyzer's privileged user monitoring and auditing.
It allows you to generate reports for device-wise user activities and user-wise activities. You gain key insights on privileged activities like configuration changes, software installations, and sensitive data access and changes.
Automate your incident response
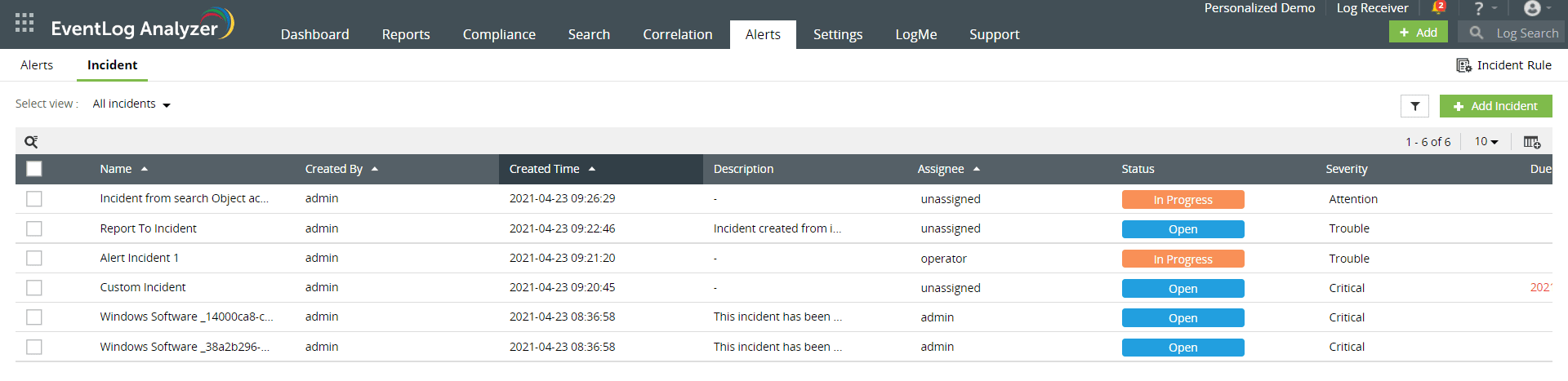
The PDPA expects organizations to have an incident management system in place to quickly mitigate attacks. EventLog Anayzer's incident response and management module automatically assigns incident workflows when a breach is detected.
This PDPA compliance solution supports integrations with external help desk software to assign tickets to security admins to speed up the resolution process. You also get notified when compliance gaps are identified in the network to help you prevent penalties.
Take a look at some PDPA rules and learn how EventLog Analyzer can help you comply with these requirements easily
| PDPA rule | Action required | What EventLog Analyzer can do |
|---|---|---|
| Rule VI Section 25 |
Personal information controllers and processors are mandated to implement appropriate physical, technical, and organizational security measures to protect personal data. |
|
| Rule VII Section 30 |
All personal information maintained by government, agencies, and instrumentalists should be secure with the use of the most appropriate standard as recognized by the information and communication industry. |
Other solutions offered by EventLog Analyzer
Event log correlation
Discover sequences of logs that indicate well-known cyberattacks by correlating logs from various sources in your network.
Contextual threat intelligence
Detect attacks at the first sign of trouble with regularly updated threat feeds using our global IP threat database and advanced threat analytics.
IT compliance management
Simplify IT compliance auditing using predefined, audit-ready report templates for various regulatory mandates, including the PCI DSS, the GDPR, HIPAA, FISMA, SOX, and ISO/IEC 27001.
Log forensics
Drill down to the raw log events and carry out root cause analysis on any network breach with ease. EventLog Analyzer provides the specific details of the attack, including the entry point, time, and extent of the damage caused in the network by recreating the crime scene.
5 reasons to choose EventLog Analyzer as your PDPA compliance solution
1. Comprehensive log management
Ensure that every segment of your network complies with the PDPA. EventLog Analyzer supports over 750 log sources, ensuring complete log management. You can automate the process of collecting, monitoring, analyzing, and reporting on network logs.
2. In-depth auditing and reporting
Generate PDPA audit reports for your organization with EventLog Analyzer's predefined compliance templates. The solution also supports other prominent regulatory mandates, including the PCI DSS, the GDPR, HIPAA, SOX, and FISMA.
3. A powerful correlation engine
Detect anomalies in your network by identifying complex sequences of events occurring in various sources. EventLog Analyzer's powerful correlation engine holds over 30 predefined correlation rules and detects known malicious patterns by analyzing activities across the network.
4. Automated incident management
Implement a reliable system to detect and prevent malicious activity in your network. The solution has an integrated incident response and management console that assigns tickets when critical security events are detected to speed up incident resolution.
5. Augmented threat intelligence
Ensure that no malicious source enters your network with the advanced threat intelligence feeds. Detect malicious IP addresses, URLs, and domain interactions with the built-in global IP threat intelligence database and the STIX and TAXII feed processor.
Frequently asked questions
The PDPA of 2012 (The Republic Act 10173) is a law that protects the personal and privileged information of the public from being misused or mishandled. The act is designed to protect the personal information of citizens, and it also regulates how companies can collect and use personal information.
The law requires organizations that handle personal data to maintain secure systems for storing and handling it and to provide users with means by which they can access their data and correct any errors in it. The PDPA is divided into nine chapters:
- General Provisions
- Collection of Personal Data by Private Parties
- Use of Personal Data
- Security Safeguards for Personal Data
- Disclosure of Personal Data
- Policy Management
- Non-monetary Remedies for the Violation of Rights Under This Act
- Jurisdiction and Venue of Actions Under This Act
- Transitory Provision
The Implementing Rules and Regulations (IRR) provision of the PDPA is a set of guidelines created to ensure that the act is being followed properly. These rules require companies that use or store the personal information of customers to:
- Have an information security program in place that meets certain standards and includes incident response planning and training, data classification schemes, and database access control policies.
- Have a privacy officer who ensures the company is complying with all applicable laws and regulations related to data privacy.
The PDPA must be followed by all private companies, government agencies, and other institutions based in the Philippines. It also applies to any person who processes personal data on behalf of an entity covered by this law.











