- Key features
- FAQs
- Useful resources
Key features
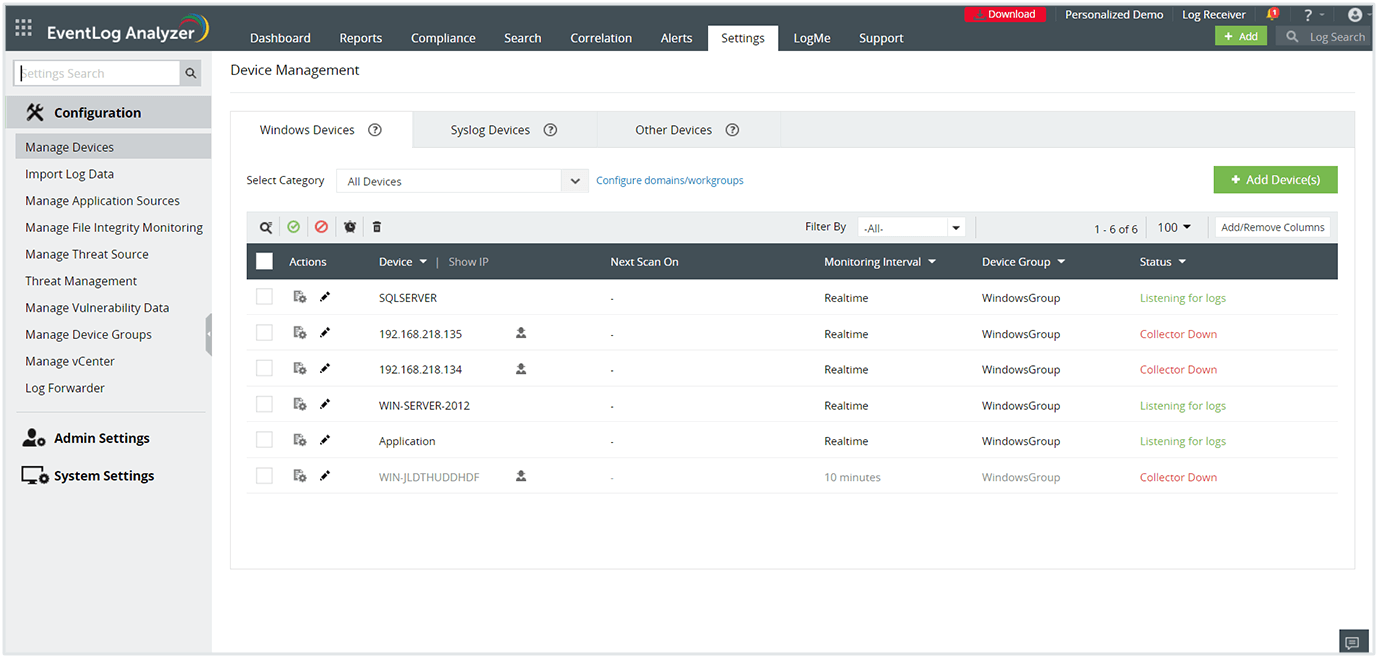
Auto discovery and collection of Windows event logs
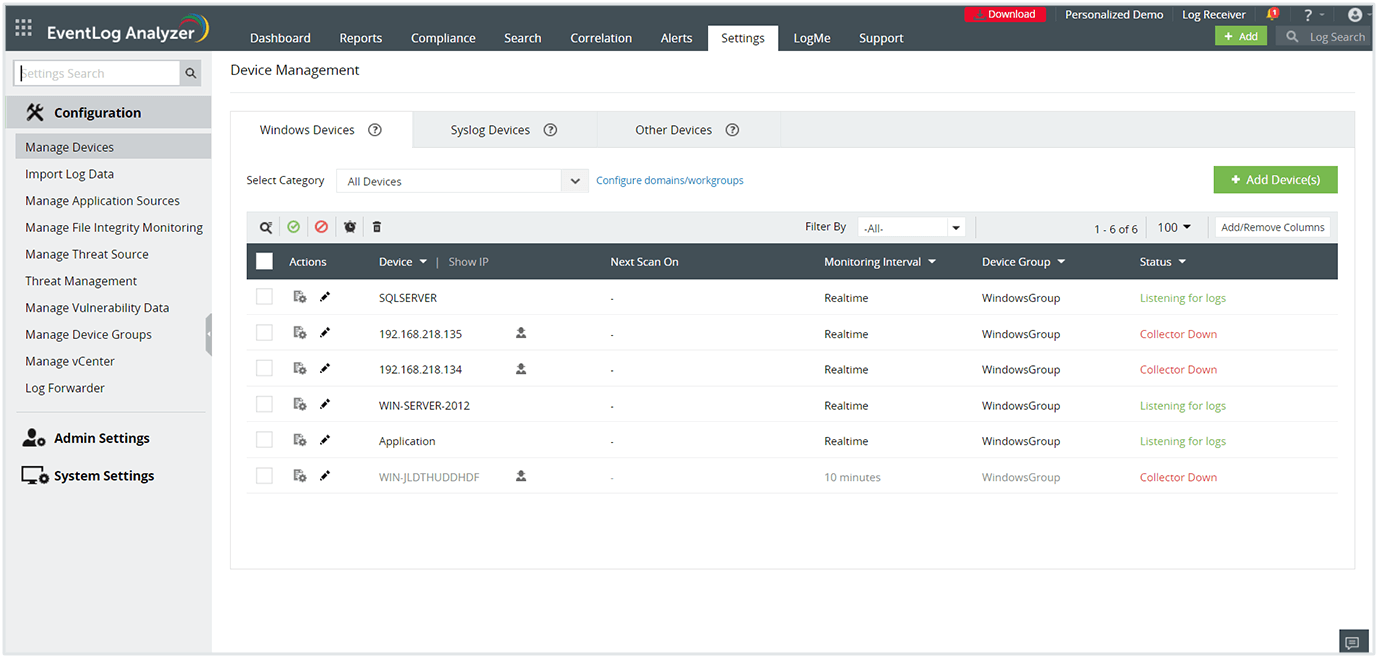
Identify all Widows log sources in your domain and start collecting Windows event logs easily with EventLog Analyzer's autodiscover option. The feature detects Windows workstations, firewalls, IIS servers, and SQL servers automatically. Simply select the critical sources and automate log file management to fortify your network.

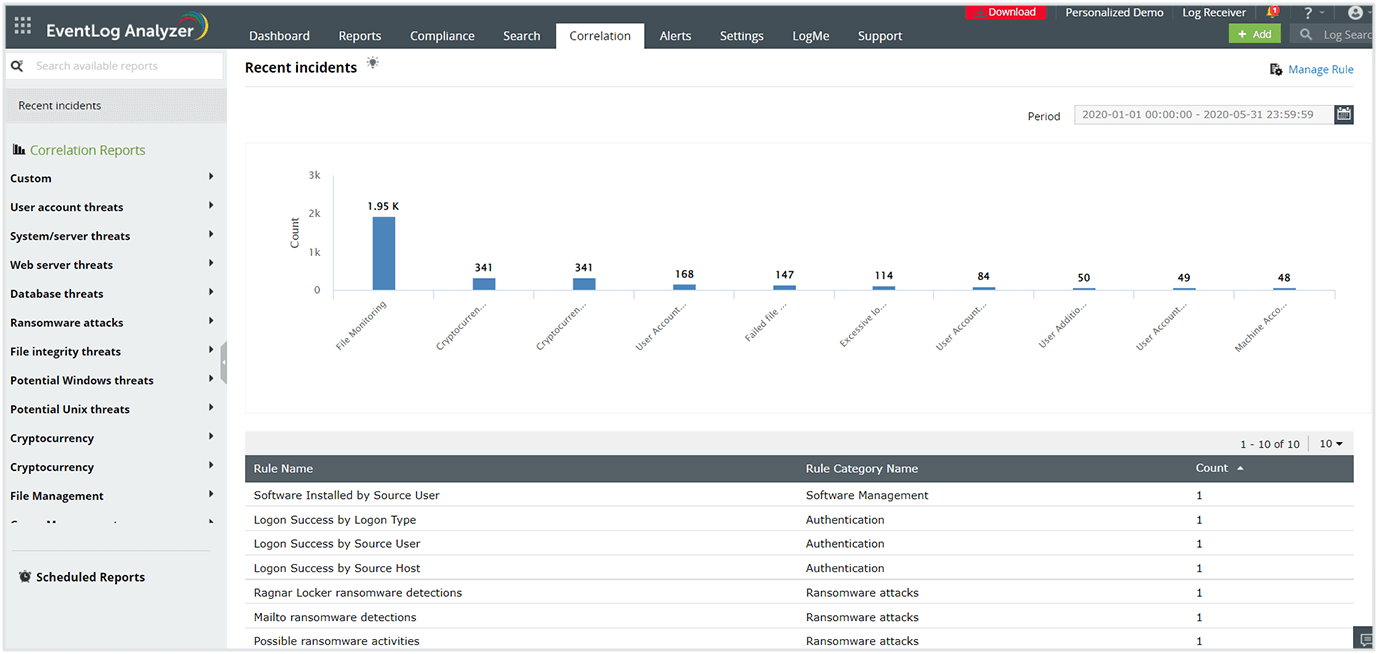
In-depth log analysis with a powerful correlation engine
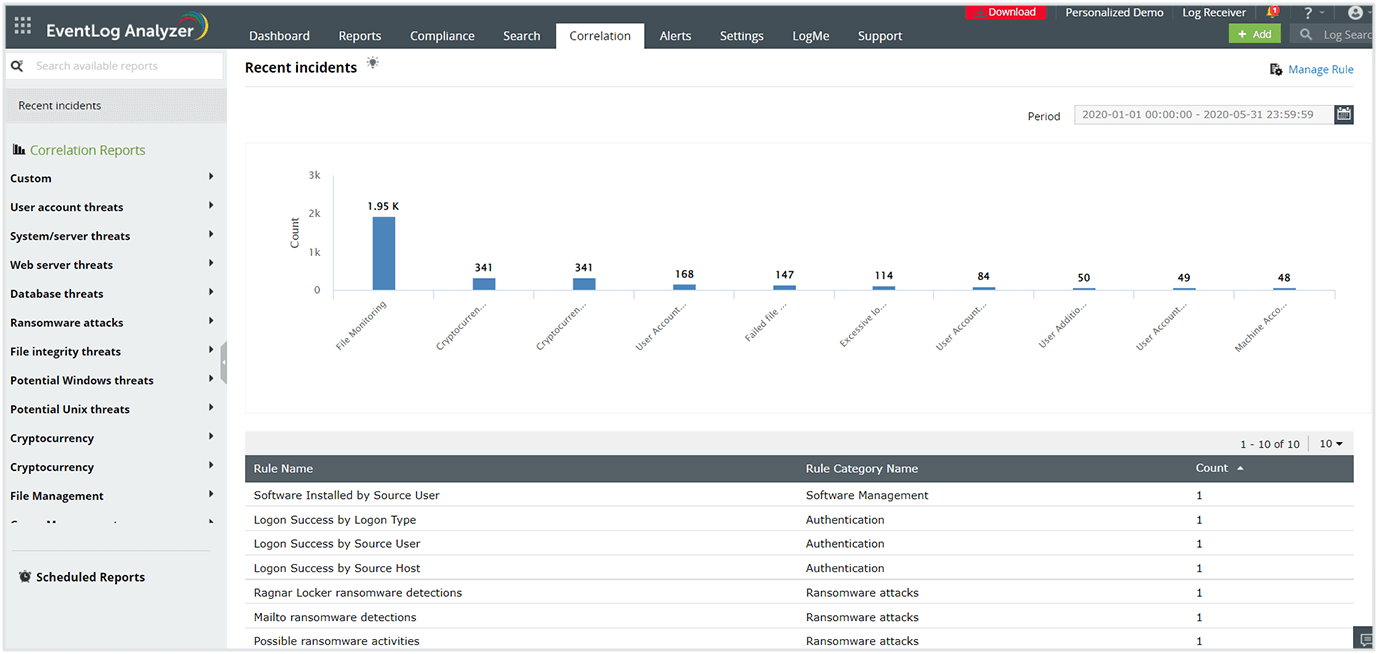
Utilize the powerful correlation engine to gain comprehensive insights by making sense of log data from all the log sources present in the network. The Windows log monitoring tool contains over 40 pre-built correlation rules to detect the most common cyberattacks like SQL injection, DoS, and brute-force. You also have the option to build custom rules to detect more complex patterns.
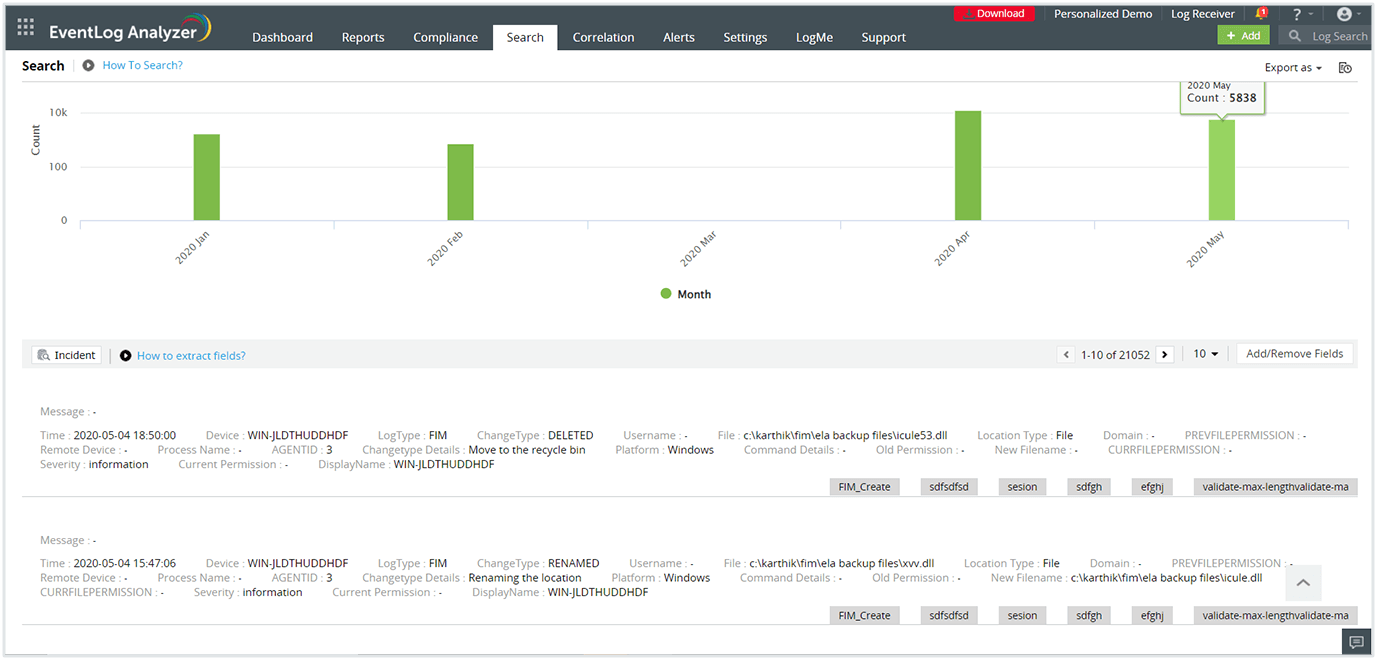
Threat detection through log forensics
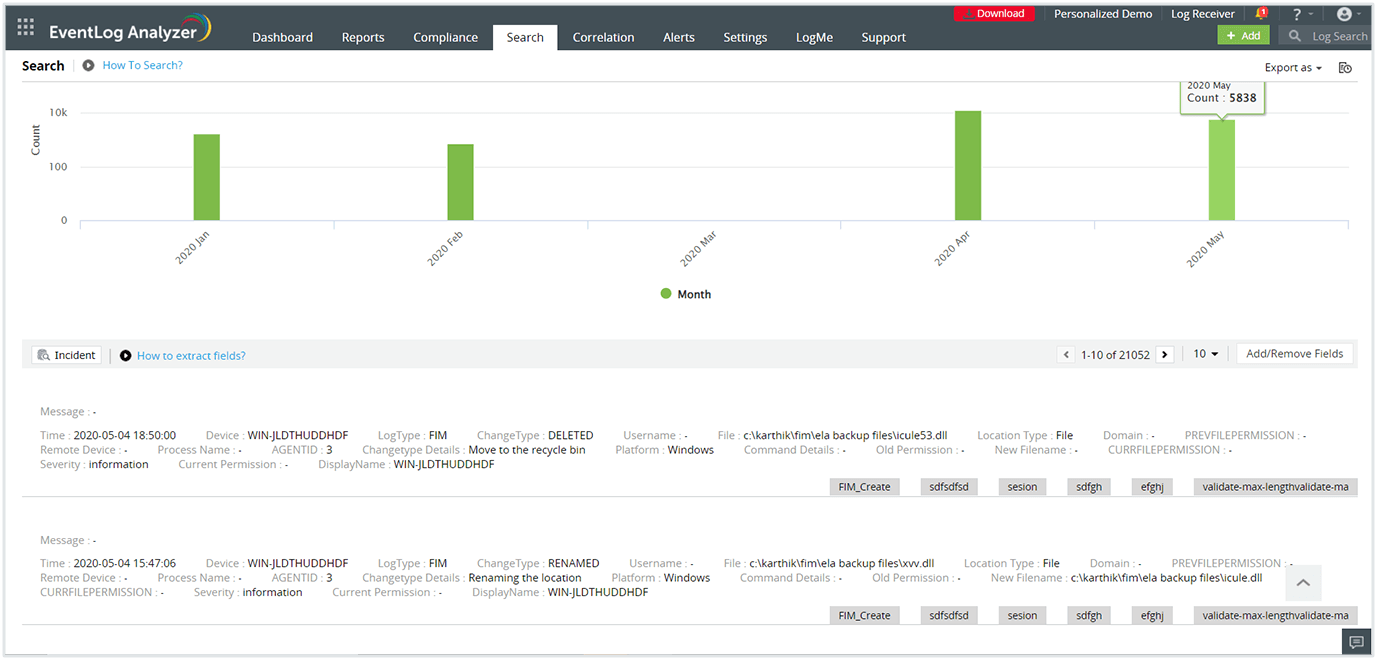
Conduct root cause analysis for any security event in your network in minutes. EventLog Analyzer monitors Windows activity in real-time, allowing you to search through raw event logs and pinpoint the exact log entry that caused a security incident. The solution makes it easy for you to find mission-critical information about the detected incident, including severity level, time, location, and the user who initiated the event. This helps you take the required countermeasures within a short timeframe to speed up incident resolution.
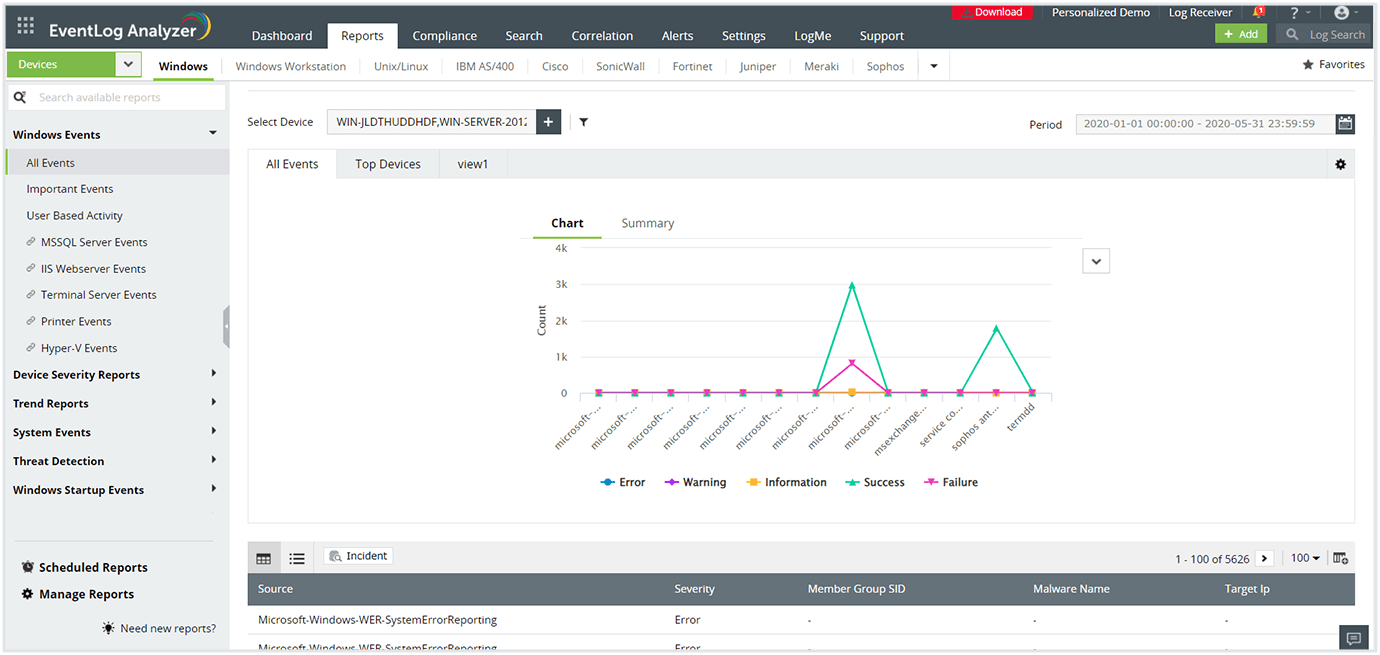
Reporting from Windows servers and workstations
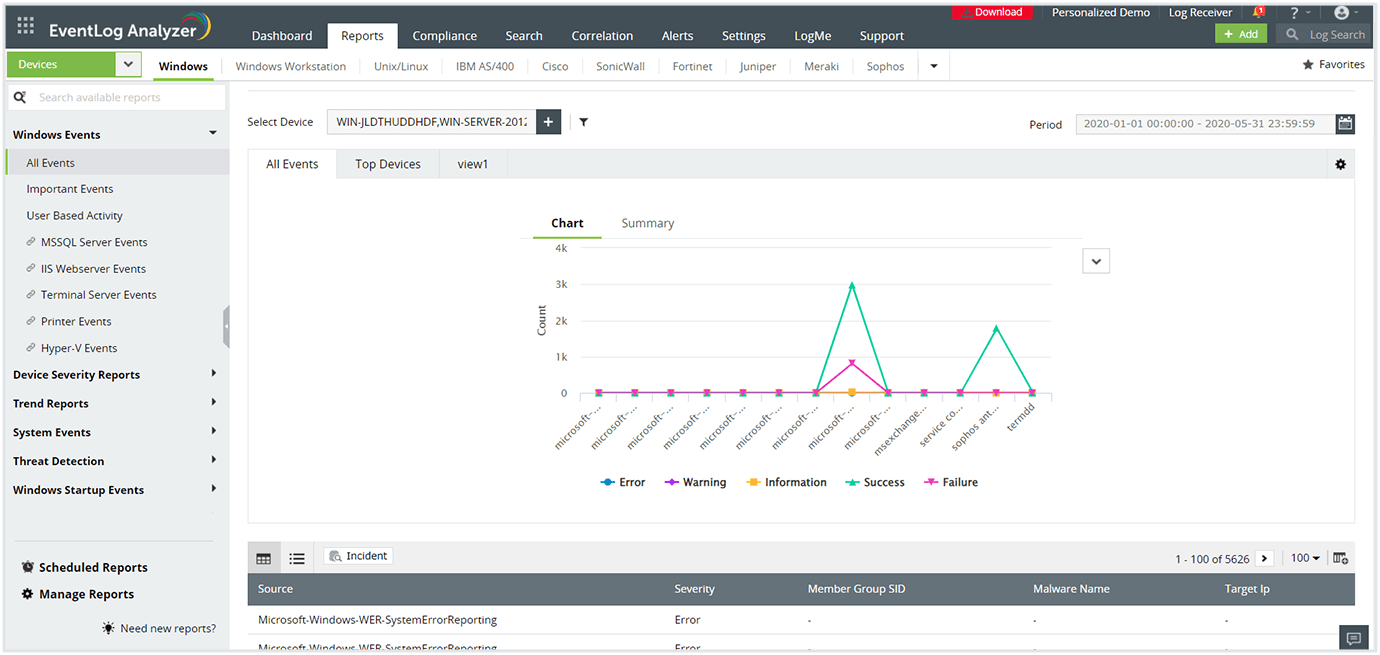
Generate detailed reports based on event logs from Windows servers and workstations. EventLog Analyzer contains numerous Windows-specific report templates for security events like failed logons, account lockouts, and security log tampering. The solution also contains compliance-ready report templates for regulatory mandates like PCI DSS, SOX, HIPAA, the GDPR, and FISMA. You can also build custom reports to meet internal audit policies.
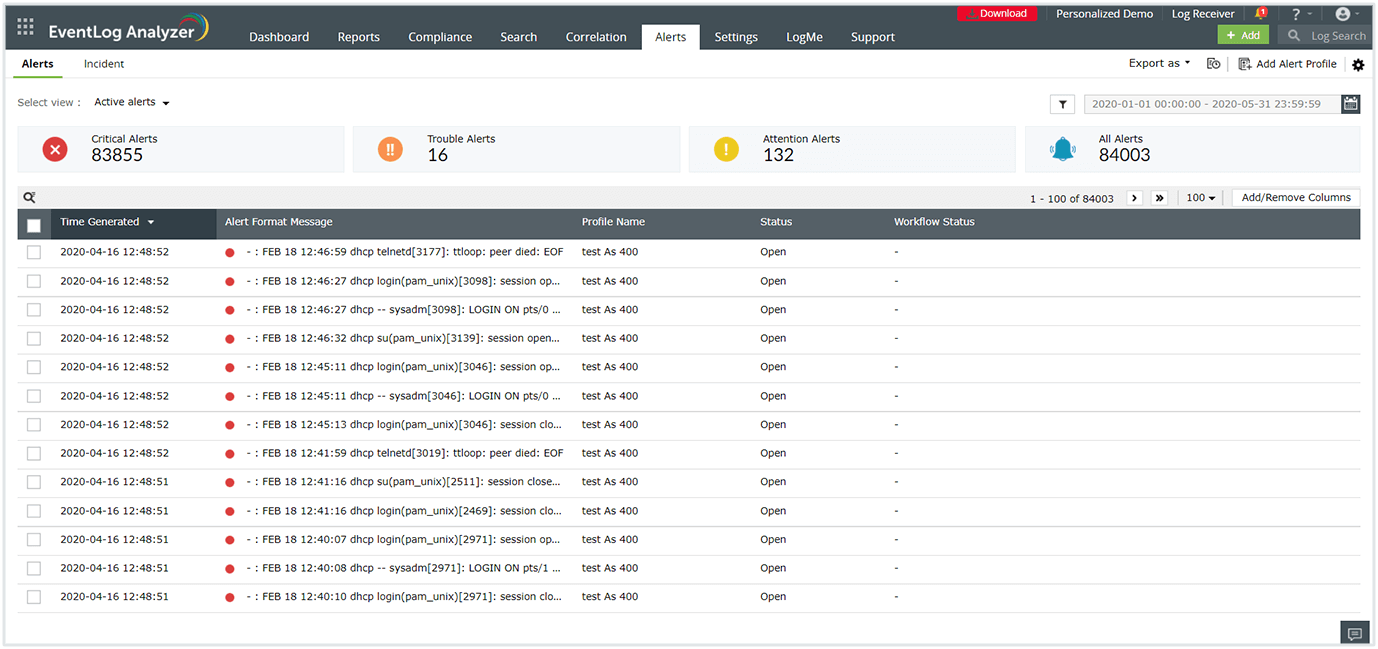
Instant alerting for Windows events
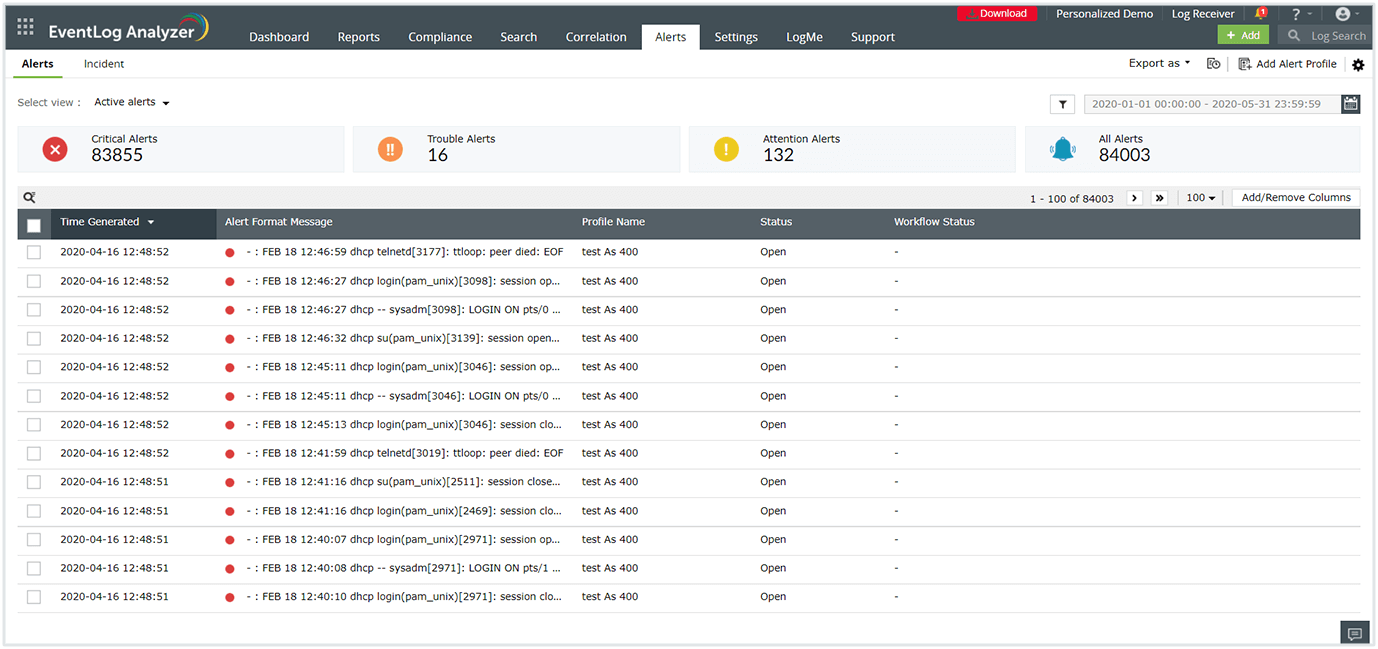
Detect security events happening in your network instantly and expedite the troubleshooting process. You can configure EventLog Analyzer to send real-time alerts to manage incidents based on logs generated with a specific log type, event ID, log message, or severity. It also supports integration with help desk software, so tickets can be raised automatically in your help desk software.
Frequently asked questions
What are Windows event logs?
Windows event logs are files that record all the activities taking place on a Microsoft system. In a Windows environment, events are logged for systems, security, and the applications hosted on the system. Event logs provide context with detailed information on the events, including the date, time, event IDs, source, event type, and the user who initiated it.
How does monitoring security logs help in mitigating cyberattacks?
Security event logs contain records of all the security-related events specified by the system's audit policy. This may include login and logoff attempts, modification of privileged information, and more. Windows uses event IDs to define the type of event. You should monitor the following event IDs for security-related incidents:
- 4740: Locked user account
- 4625: Failed account logons
- 4719: Changed system audit policy
- 1102: Cleared audit logs
- 4728, 4732, 4756: Added member to security global, local, and universal group
- 4777: Failed validation of account credentials by domain controller
- 4663: Attempt to access object
By monitoring Windows security logs at a granular level, you can spot anomalies, suspicious activities, and data breaches at the earliest stages to avoid full-blown cyberattacks.
How does EventLog Analyzer monitor Windows events?
EventLog Analyzer is a comprehensive log management tool that supports Windows event logs along with other log sources on a single console. The solution automates log collection through agent-based and agentless methods. Once the log is collected on a central server; it parses, analyzes, correlates, and archives the log data to complete the process. The insights drawn from the logs are presented in the form of intuitive dashboards and exhaustive reports.
EventLog Analyzer's wide range of features make it easy for network administrators to detect cyberattacks well in advance and play a vital role in keeping the network safe and sound.
Comprehensive Windows event log monitoring made easy.
Thanks!
Your download is in progress and it will be completed in just a few seconds!
If you face any issues, download manually here
Other features
EventLog Analyzer offers log management, file integrity monitoring, and real-time event correlation capabilities in a single console that help meeting SIEM needs, combat security attacks, and prevent data breaches.
Analyze event log data to detect security events such as file/folder changes, registry changes, and more. Study DDoS, Flood, Syn, and Spoof attacks in detail with predefined reports.
Analyze application log from IIS and Apache web servers, Oracle & MS SQL databases, DHCP Windows and Linux applications and more. Mitigate application security attacks with reports & real-time alerts.
Monitor all types of log data from Active Directory infrastructure. Track failure incidents in real-time and build custom reports to monitor specific Active Directory events of your interest.
Monitor and track privileged user activities to meet PUMA requirements. Get out-of-the-box reports on critical activities such as logon failures, reason for logon failure, and more.
Perform in-depth forensic analysis to backtrack attacks and identify the root cause of incidents. Save search queries as alert profile to mitigate future threats.
Need Features? Tell Us
If you want to see additional features implemented in EventLog Analyzer, we would love to hear. Click here to continue