Firewall rule impact analysis
Firewall Analyzer's Rule Impact Analysis feature does the following:
- Checks the proposed new rule against the existing rule base for anomalies (Firewall Ruleset Analyzer).
- Suggests an optimal rule order by analyzing the proposed new rule for rule complexity and anomalies.
- Identifies any overly permissive destination interfaces for the proposed new rule.
- Detects and reports on service, application, and interface-level threats.
- Singles out blacklisted IP addresses that are used in the proposed new rule.
- Provides risk assessment for relevant service, application, and interface ports.
With these reports, you can identify threats, understand firewall rule risk, remove anomalies, and optimize the proposed new rule. After running the rule impact analysis and clearing out all the complications, you can finally implement the rule in your firewall.
How does Firewall Analyzer help with rule impact analysis?
Firewall Analyzer's Rule Impact feature lets you perform in-depth impact analysis for a proposed new rule. Before you make the new rule live, you can use the Rule Impact feature to determine if the proposed new rule is going to impact the existing rule set negatively. Thus, Firewall Analyzer acts as an efficient firewall rule planning tool.
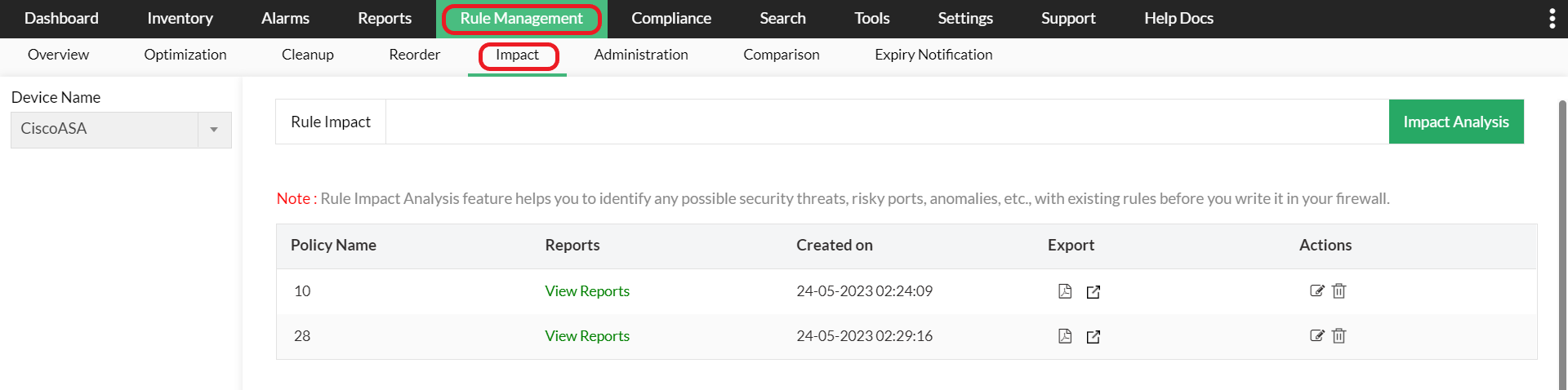
Rule impact analysis
Firewall rules play a crucial role in efficient network security management. Before adding a rule, it's vital to ensure that the proposed new rule won't negatively impact the network.
With firewall rule impact analysis, security admins get a detailed overview of the possible effects of adding a new rule. An important aspect of firewall rule impact analysis is that it's proactive in nature, as it works to prevent security loopholes in the network altogether.
Why should a security admin perform rule impact analysis?
The level of protection provided by a firewall directly depends on the quality of its policy. So, it's important that security admins constantly optimize firewall rules and adhere to a robust firewall policy design. However, configuring firewall rules is neither a one-time activity, nor is it a simple task.
An organization typically has hundreds of rules, and not all firewall rules are independent from each other. In fact, most rules have a distinct impact on a set of other rules and it is important to get the basic firewall policy design spot-on. The simplest error can trigger a massive security loophole that either allows malicious traffic to sneak in or blocks legitimate traffic and disrupts normal business.
This is why security admins need to thoroughly study the firewall rule design and measure the consequences of adding a new rule before making the changes live in the firewall (firewall policy rule planning and design).
Refer the 'Firewall Rule Administration' page for more details.
Refer Configure Firewall Rules page to know how to configure firewall rules.
Get started using Firewall Analyzer with a free, 30-day trial, and see for yourself how it can help with firewall policies and maintenance.
Featured links
Firewall Reports
Get a slew of security and traffic reports to asses the network security posture. Analyze the reports and take measures to prevent future security incidents. Monitor the Internet usage of enterprise users.
Firewall Compliance Management
Integrated compliance management system automates your firewall compliance audits. Ready made reports available for the major regulatory mandates such as PCI-DSS, ISO 27001, NIST, NERC-CIP, and SANS.
Firewall Log Management
Unlock the wealth of network security information hidden in the firewall logs. Analyze the logs to find the security threats faced by the network. Also, get the Internet traffic pattern for capacity planning.
Real-time Bandwidth Monitoring
With live bandwidth monitoring, you can identify the abnormal sudden shhot up of bandwidth use. Take remedial measures to contain the sudden surge in bandwidth consumption.
Firewall Alerts
Take instant remedial actions, when you get notified in real-time for network security incidents. Check and restrict Internet usage if banwidth exceeds specified threshold.
Manage Firewall Service
MSSPs can host multiple tenants, with exclusive segmented and secured access to their respective data. Scalable to address their needs. Manages firewalls deployed around the globe.