Network Configuration Management (NCM) is a critical process applied to every device in the network throughout its lifecycle. It includes device discovery, inventory maintenance, configuration backup, monitoring configuration changes and compliance, tracking user activity, and troubleshooting by performing necessary network operations.
Managing network configuration manually can be tedious and time-consuming for administrators. However, automating network configuration management based on specific needs and requirements significantly enhances the efficiency of the network infrastructure while reducing the management overhead for administrators.
What is Network Configuration Manager?
Network Configuration Manager, which acts as a network configuration management tool, provides comprehensive network configuration management solutions that help you manage the entire life cycle of your network devices and configurations. It provides solutions for network configuration, change, and compliance management. Network Configuration Manager also assists you with crucial network operations like automating complex network operations, scheduling backups, tracking user activity, generating detailed reports, and a lot more.
Let's explore some of the key functions Network Configuration Manager that form an integral part of network configuration management (NCM).
Features of network configuration management (NCM)
Network Configuration Manager simplifies and automates the management of network devices, helping organizations maintain a secure, efficient, and compliant network environment. Its features address various critical aspects of device lifecycle management and operational reliability. Below are some key network configuration manager functions:
1. Network device discovery
Discovering your device and adding it to the inventory is the first step in network configuration management. It is important to keep records of your network devices and their hardware properties. Besides improving the network admin's visibility into the network devices, an informative inventory will help the admin conduct regular audits. The inventory gives a detailed view into the device specifics such as the serial numbers, interface details, port configurations, and hardware specifics of the device which will all prove useful while compiling audit reports.
2. Configuration backup
A network operator must always be ready for a network mishap, and the most fundamental element in becoming disaster-ready is taking network backups as it the most important network configuration management featuresA faulty change or update can cause problems like a network outage or a security breach. Any such events can immediately be dealt under network configuration management (NCM) with by overwriting the faulty configuration with a trusted version from the backup.
Most organizations manually take backups and save them as flat files. This is not recommended as it increases the risk and chances of being hacked. Remember to always encrypt and save your configurations.
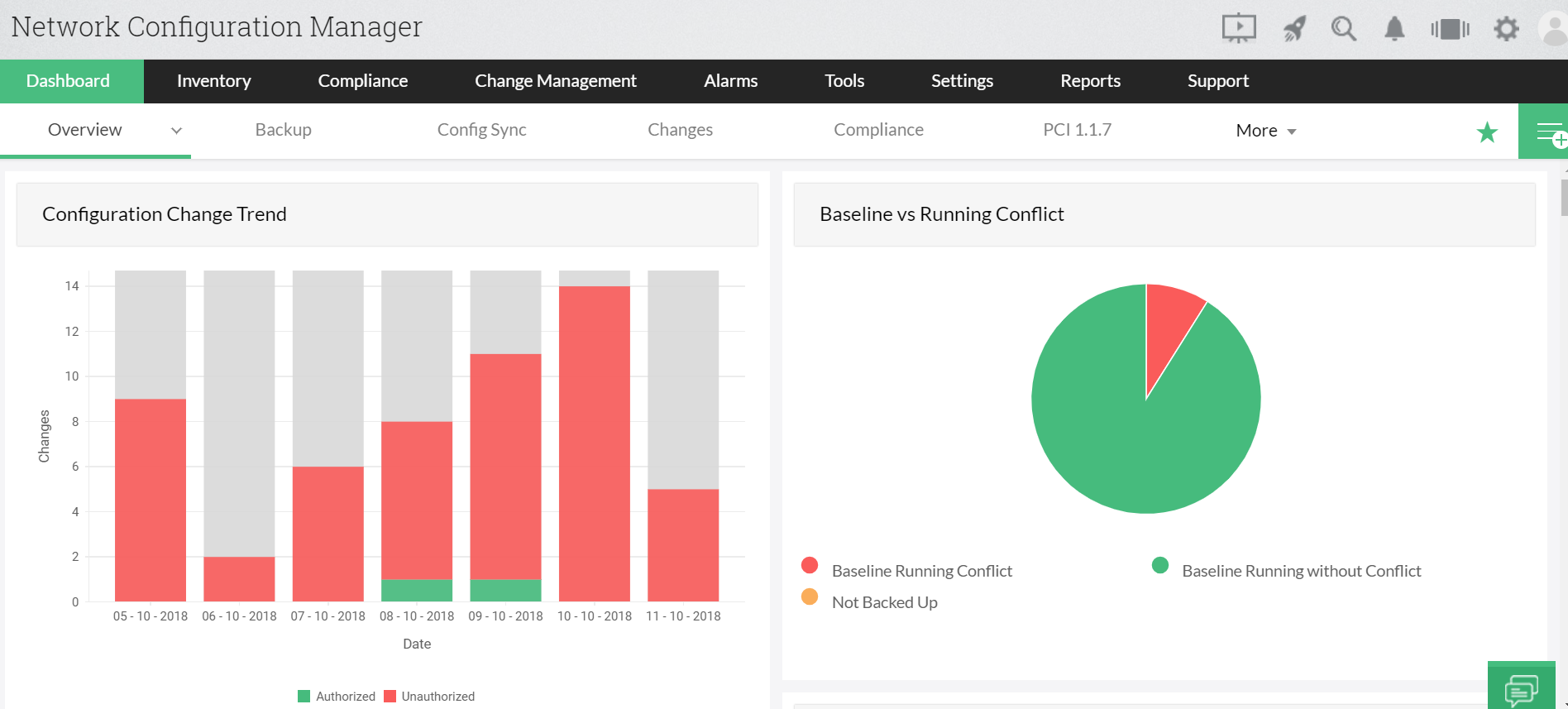
3. Configuration change management
It is recommended that you keep a record of your users to facilitate easier identification of configuration changes. In a network that houses multiple operators, it is crucial to avoid any unauthorized change that might bring about an unfavorable output. While these only cut down the chances of something going wrong on the network, they don't entirely eliminate the chances of it happening. This is where the configuration backups come into a play. You can readily upload a trusted version of the configuration and restore the device and ensure business continuity using Network Configuration Manager.
4. Executing complex network operations
Network Configuration Manager includes the execution of many network operations, and sometimes these can also be automated. For instance, if you need to change the password of all Cisco routers on a network, applying the change to every device individually would be a tedious process. This is where configuration templates that are commonly called 'Configlets' come into play. You can centrally execute this operation to all the devices using configlets. They also come with the added advantage of scheduling, which does not require the user to be around while the operation is being executed.
5. Network compliance to industry standards
There are some industry standards to which your network devices must comply to. This is to ensure that your data is secure and to keep your business away from the risk of dis reputation.
Let's look into a few examples of compliance requirements and their respective actions below:
CIS Cisco ASA Policy:
The CIS Cisco ASA Policy ensures that network devices running on the Cisco Adaptive Security Appliance (ASA) operating system are properly configured for security.
- Condition: A rule in the CIS Cisco ASA Policy requires to check if there is a local username and password in the configuration.
- Action Required: The network admin has to add a local username and password to the configuration.
By following this requirement, administrators can enhance the security of network devices running on Cisco ASA and ensure they meet best practice security standards.
PCI Compliance:
PCI Compliance applies to any company that handles cardholder data, ensuring secure payment processing and storage.
- Condition: There is a condition in the PCI Compliance Policy that requires the password of all devices to be reset every 6 months.
- Action Required: The network admin has to check if the password has been changed on time.
Adhering to PCI Compliance helps protect sensitive cardholder information and reduces the risk of data breaches or fraud.
Sox Compliance:
TSOX Compliance aims to protect investors and the public by improving the accuracy and reliability of financial reporting in organizations.
- Condition: A clause in the Sox compliance requires the user to be locked out once there is a particular number of failed login attempts.
- Action Required: The admin is supposed to set the maximum number of failed login attempts.
This requirement ensures that access to sensitive systems is controlled and helps prevent unauthorized access to critical financial data.
HIPAA Compliance:
HIPAA Compliance ensures that sensitive patient health information is protected and properly managed by healthcare organizations.
- Condition: HIPAA Compliance requires NBAR to be used to track traffic and block unwanted protocols. (NBAR is a mechanism that regulates and classifies bandwidth for network applications.)
- Action Required: The admin is supposed to check and enable NBAR.
By implementing NBAR, organizations ensure the integrity and security of health-related data and comply with federal privacy regulations.
Benefits of using Network Configuration Manager: A comprehensive network configuration management (NCM) software
Network Configuration Manager delivers powerful solutions to address the challenges of managing network device configurations in dynamic environments. Its capabilities are made to improve operational efficiency, ensure compliance with standards, and safeguard networks from potential risks. Here are the standout advantages of using a network config management software:
- Built-in multi-vendor device configurations.
- Take automated backups of your configuration files.
- Encrypt and store configuration files.
- Track configuration changes in real-time.
- Record a history of configuration changes.
- Recover from network disasters instantly.
- Enhanced network security by preventing unauthorized configuration changes and notifying the admin.
- Reduce configuration errors by regulating changes with change management.
- Automate both simple and complex network operations.
- Ensure device configuration compliance to industry standards.
- Save time spent on repetitive tasks.
- Roll-back mechanism when configuration changes are unsatisfactory.
- Generate insightful reports on changes, compliance, inventory, and other vital network parameters.
Ready to take control of your network configurations? Download Network Configuration Manager today and enjoy a 30-day free trial.
Learn everything you need to know about network configuration management (NCM) in detail.
Find out how Network Configuration Manager streamlines network device management for your organization.
