SAML Authentication
Security Assertion Markup Language (SAML) is an XML-based standard that exchanges authentication credentials between a service provider (SP) and an identity provider (IdP). It eliminates the need for multiple passwords and, with the help of single sign-on (SSO) functionality, offers a secure, easy way to access multiple applications with common login credentials.
Service provider: The SP is an application or a third-party entity that provides service to an end user. SPs need authentication from the IdP to facilitate authentication for the user. Examples: ManageEngine OpManager and ManageEngine Desktop Central.
Identity provider: The IdP is an entity that stores user identities or resources such as usernames, passwords, and SSH keys. Examples: Okta, Microsoft ADFS, Auth0, CyberArk, and Azure SSO.
SAML authentication in OpManager
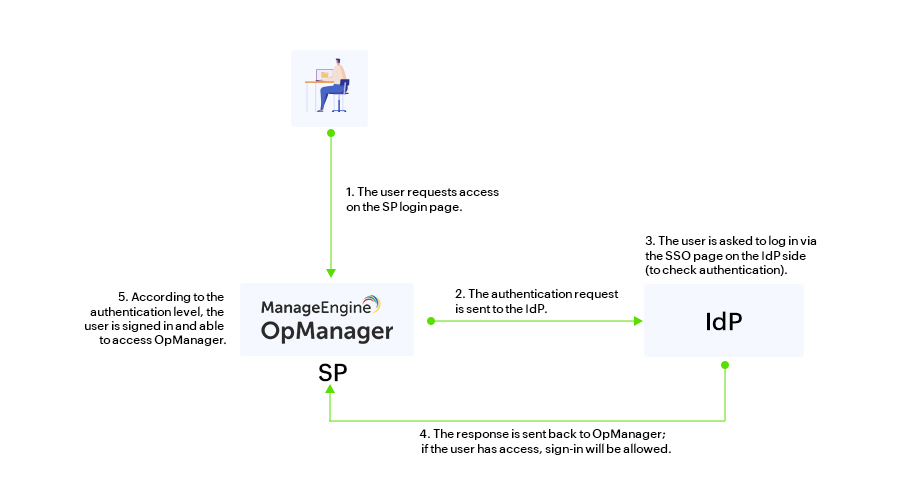
Users can now log into OpManager with SAML. During sign-in, a request is sent to the IdP and checked for the necessary authentication credentials for that particular user. The response is then communicated back to OpManager, and the user gains access.
For example, once SAML is configured, users will have an option on OpManager's login page to connect them to the SSO login page on the IdP side. Once signed in, the user will be redirected back to OpManager and logged in using the authentication given by the IdP, assuming the user account is available. If the user can’t be authenticated, their access will be denied and they will be returned to the OpManager login page.
Configuring SAML in OpManager
SAML requires two different configuration processes. The service provider i.e OpManager and the Identity provider should be configured in-order to successfully configure SAML. The SP and IdP can be configured in two ways, either manually by providing the necessary credentials, or automatically by uploading the XML metadata file. To know more about configuring IdP and SP for SAML in OpManager, visit our SAML help page.
Service provider details
The following Service provider details are required if you opt to configure SAML manually,
- Entity ID
- Assertion Consumer URL
- SSO Logout URL
- SP certificate file
This information is available in the OpManager UI, and can be used to add OpManager as a supported application in your IdP. You can also download the SP metadata file directly from OpManager and import it on the IdP side. This metadata file will have all the above-mentioned details in XML format.To learn more about SAML configuration in OpManager, click here.
Identity provider details
Similar to the SP details configuration, you can either configure the IdP details manually or upload the metadata file fetched from the IdP side.
Click the corresponding IdP name to see the steps to configure SAML between OpManager and that IdP.