Network incident management is integral to run an organization's IT network. The end goal of network incident management is simple; restore the service or functionality as quickly as possible in the event of an outage.
Fast outage detection is the ability to identify network incidents in real time using intelligent monitoring and anomaly detection. With fast outage detection in ManageEngine OpManager, IT teams can instantly detect disruptions, reduce mean time to resolution (MTTR), and minimize downtime impact.
Incident management sounds simple enough, but to do it efficiently and consistently, an IT operations team needs to be on their toes, constantly abreast of the network happenings, and have to follow a set of procedures systematically.
Get to know:
- What is network incident management
- Pros of network incident management
- Types of incidents
- The network incident management process
- OpManager: The definitive answer to all of your network management needs
What is network incident management?
Going by pure definition, incident management is the process of minimizing the overall impact of an incident by restoring full functionality as quickly as possible. From a network standpoint, an incident can be an unforeseen network disruption, an inconsistency in the quality of service (like fluctuating bandwidth), or an event that may impact service to the user or customer in the future.
Pros of network incident management
- Network incident management creates a record of past incidents. Correct documentation can help a team improve their network management practices going forward.
- Documentation of past incidents also ensure repetitive incidents are avoided or swiftly resolved.
- Efficient communication and incident management go hand in hand. The outcome is improved transparency with all concerned stakeholders in an organization.
- The incident data collected can be used for analyzing trends and patterns.
- The systems in place drastically reduce the risk of network outages.
- Faster turnaround time, from the incident to service restoration, ensures increased customer satisfaction.
Types of incidents
Incidents can be classed according to the network components they affect.
Hardware: Network devices can go down, or experience slowness or an outage. Critical hardware like servers, CPUs, routers, monitors, and printers are all prone to outages.
Software: Software-related issues can affect internal applications that are critical to an organization. This can also include issues affecting the antivirus or operating system, which can potentially slow down the network.
Security: Incidents related to security are active and potential threats to the network, which can lead to a data breach and compromise the entire infrastructure.
Network: At the network level, incidents can happen relevant to protocols, critical network devices, or other infrastructure components that are integral to normal network functioning. Examples are incidents affecting DHCP, VPNs, IP addresses, the DNS, and so on.
Database: Databases are foundational to networks. Incidents in this area can be related to DB2, Oracle, MS SQL Server, or other databases experiencing bottlenecks.
The network incident management process
A sound incident management framework sets up the foundation for efficient incident management in practice. With a process in place, an organization can achieve perfect synergy and clarity between teams. The severity of the issue, which team should handle the incident, and the optimum turnaround time to resolve the issue are all key factors that determine the efficiency of the whole process.
1. Identify and record the incident
When a member of the IT operations team inevitably identifies that something is going wrong in the network, it should be logged and tracked. With the right tools to report and document issues, incidents can be quickly detected by technical staff. Network monitoring tools can also detect and report incidents automatically, and communicate with end users.
2. Prioritize the incident
After the incidents are duly logged in the system, it's vital to segment and prioritize tasks. This lets you quickly determine the time needed to troubleshoot the issue, if escalation is needed, and which team will handle the incident. Categories can be created according to the layer or area of the network where the incident has happened, i.e., network, cloud, or virtual.
Categorization helps create a knowledge base of past incidents, helping you analyze incidents independently to prevent future incidents. Moreover, incidents can also be denoted according to severity, like high, medium, or low. Prioritizing incidents bring order and allows them to be sorted, enabling the IT team to automate low priority or repetitive incidents and pool all efforts into resolving higher severity incidents.
In most organizations, incidents are classified based on severity, like L1, L2, and L3.
- L1 (Level 1) incident: Incidents that fall under this category are those that happen in higher volumes but are also quickly resolvable. IT operations personnel choose to automate the majority of L1 tasks so they can focus on resolving more critical incidents.
- L2 (Level 2) incident: L2 incidents are more complex issues that can disrupt the network and put a roadblock on its smooth functioning. L2 incidents hence require involvement of skilled staff with specific knowledge in the area.
- L3 (Level 3) incident: L3 incidents are issues that happen on a larger scale in the network. Major incidents like these rarely happen, but when they do, the damage they can cause to the infrastructure is huge. L3 incidents require expertise and coordination, which is why they need the attention of personnel with significant specialization in the area.
3. Investigate and respond to the incident
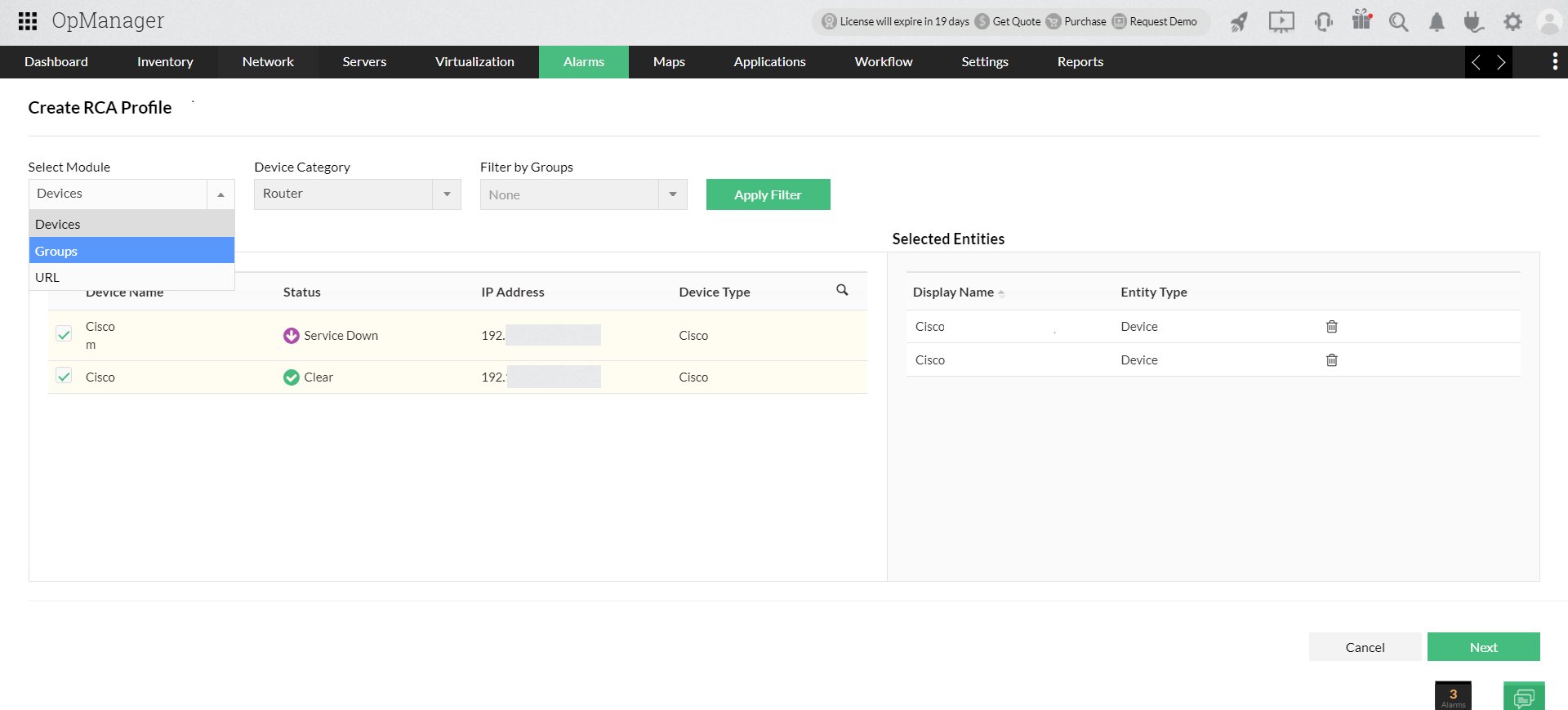
Once the incidents are assorted in an orderly fashion, the IT operations staff gets to the task of investigating and resolving the issue. With a strong knowledge base of past incidents acting as reference , the incident can be investigated and resolved efficiently. Root cause analysis is used to detect the root cause of the problem. The incident management team can then put their efforts into resolving the faulty IT service quickly.
In incident management, the team that automatically responds to an incident is the first-level team. Day-to-day incidents can be largely resolved by the first-level team. But certain incidents will need more attention and expertise, requiring escalation to a more specialized team. Escalation teams will be adept at resolving complex tasks, thanks to more expertise and resources at their disposal.
4. Incident resolution
The technical staff handling an incident focus on resolving it as quickly as possible so the network can come back online. After the problem has been fixed, prompt and clear communication to stakeholders is crucial. This verifies whether all impacted teams can continue with their work. When all stakeholders confirm and are satisfied with the restoration of service, the incident is closed and the resolution is documented.
OpManager: The definitive answer to all of your network incident management needs
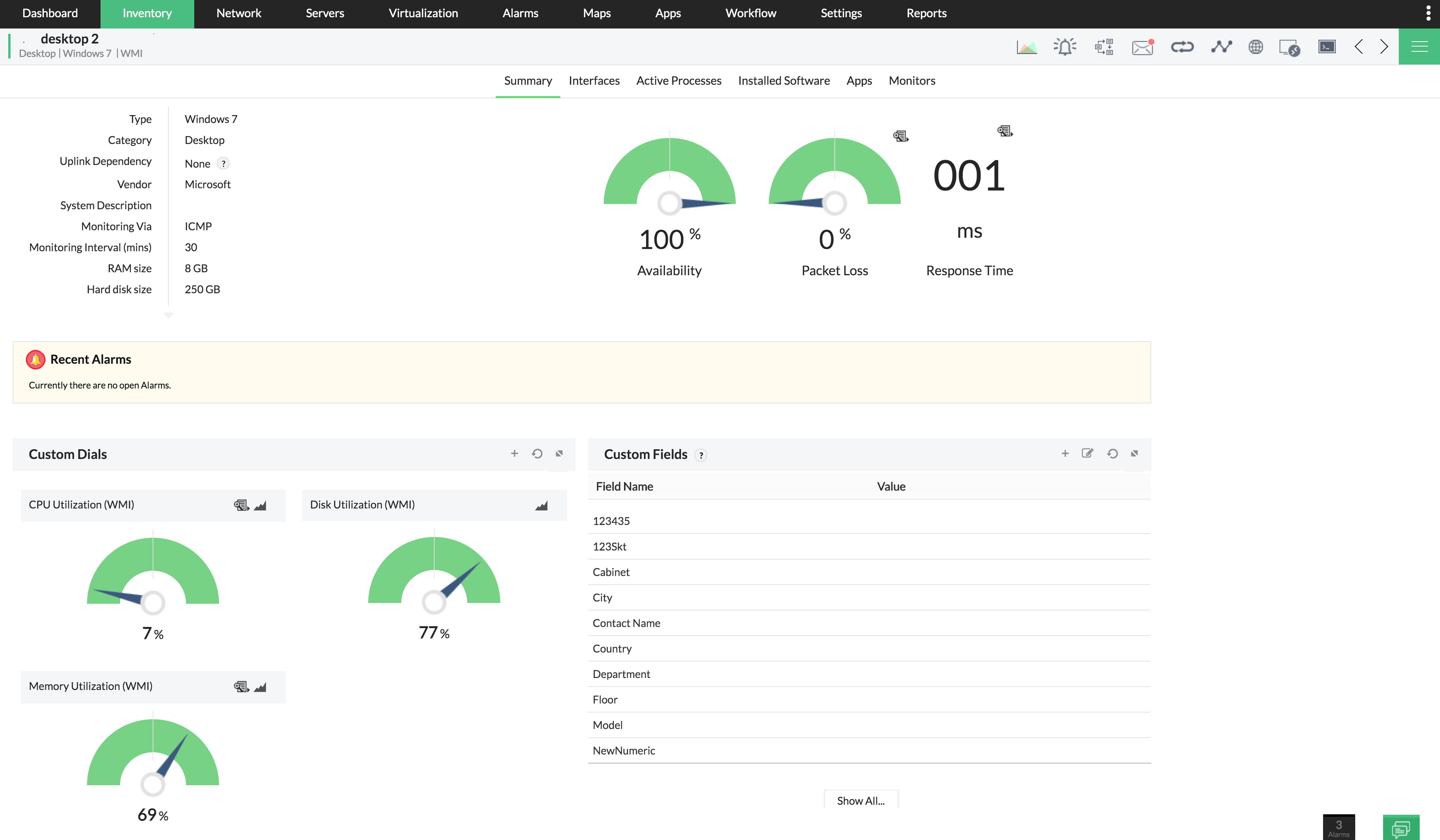
OpManager, with its powerful network monitoring features, provides deep visibility into the performance of your critical network components, including routers, switches, firewalls, load balancers, wireless LAN controllers, servers, VMs, printers, and storage devices.
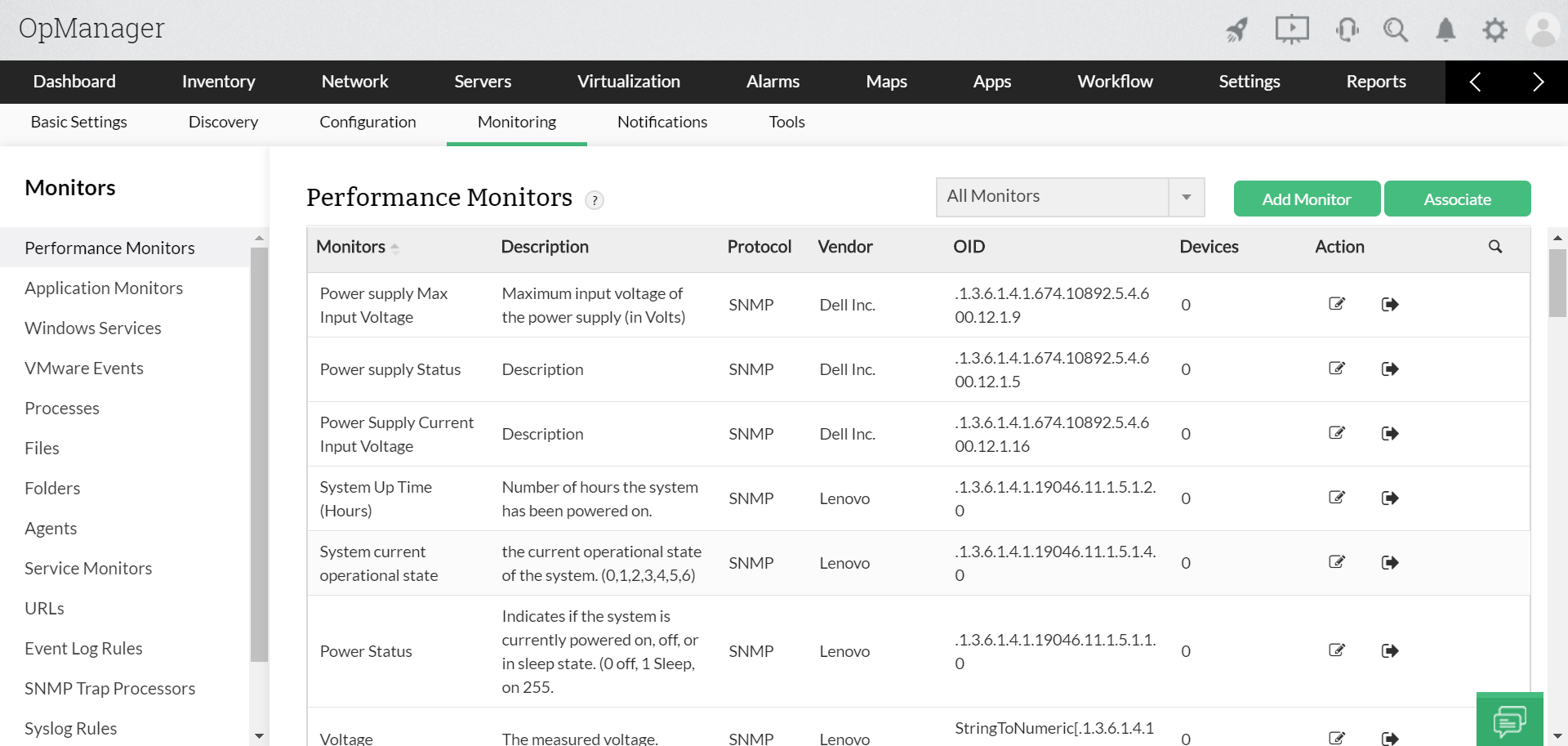
Network monitoring: Gain in-depth visibility with predefined, device-specific monitors. Monitor all your devices for availability, performance, traffic, and other parameters. Multi-level thresholds and instant-notification support facilitates proactive network management.
Physical and virtual server monitoring: Monitor servers' system resources, like CPU usage, memory consumption, disk usage, and processes. OpManager can monitor Hyper-V, VMware, Citrix, Xen, and Nutanix HCI servers.
Root cause analysis (RCA): Create an RCA profile for an issue you want to resolve. OpManager's RCA profile is a central platform that aggregates the performance data of devices, helping you compare, analyze, and get to the root of the issue.
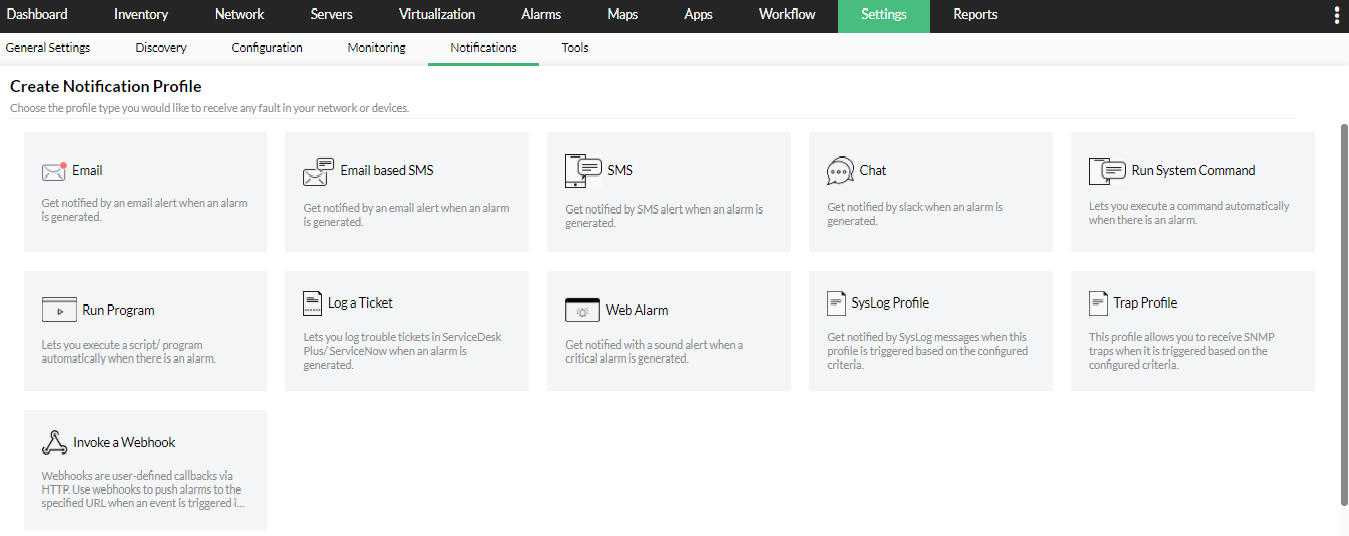
Advanced alerting: Get to know what's happening in your network anytime from anywhere. OpManager's advanced alerting system instantly alerts you on potential outages via various notification profiles such as SMS, email, slack messages, web alarms and more. You can also configure to run pre-defined scripts to automate first level troubleshooting.
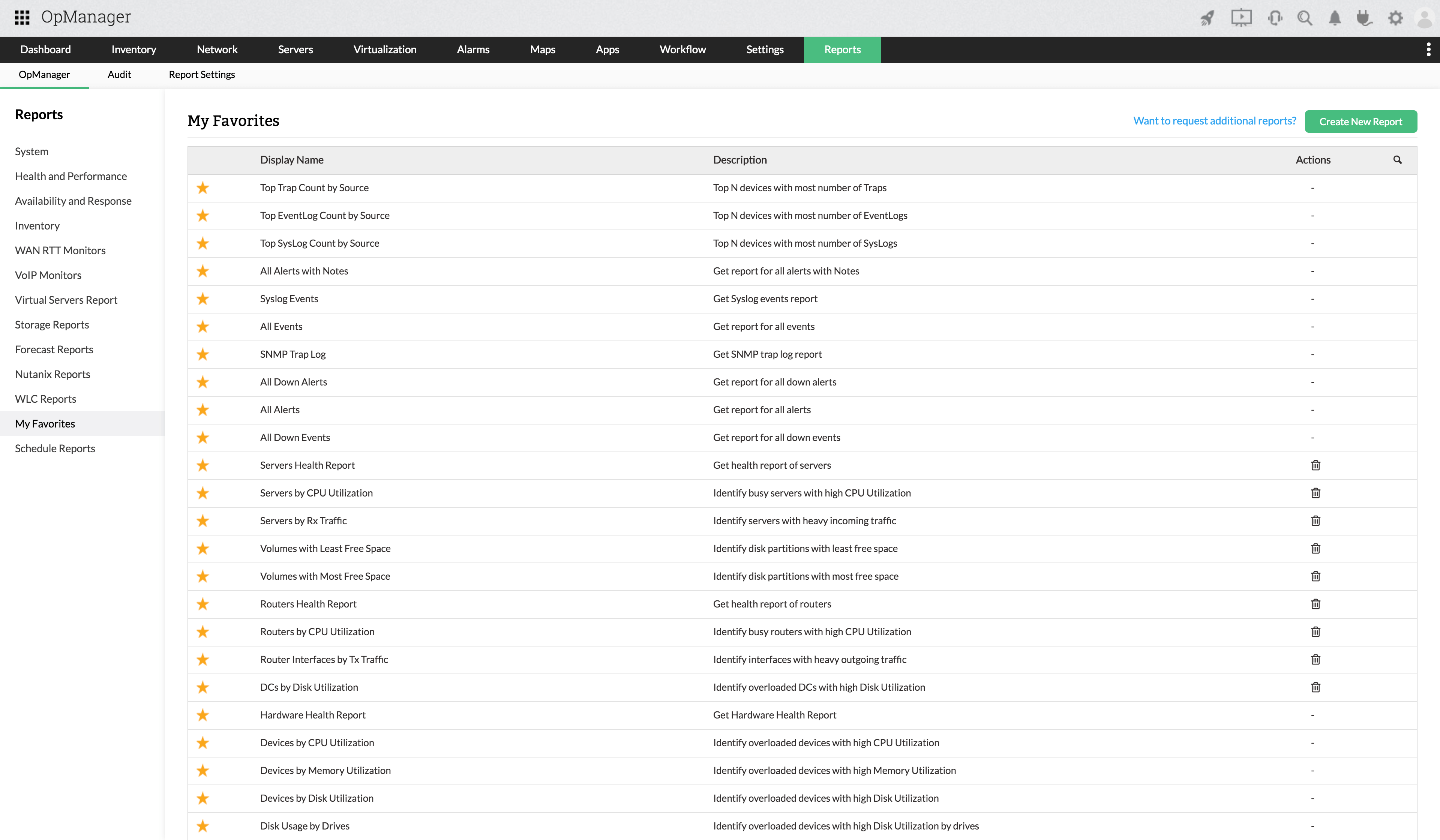
Reporting: OpManager's in-built reporting system helps you understand historical data, analyze growth trends and take a call on resource optimization. These reports help forecast storage issues and perform capacity planning to avert indiscriminate purchases.
Learn more about OpManager's exhaustive list of features, and bolster your network management.
Keep your network incidents under control with OpManager.
Download 30-day free trialCustomer reviews
Case Studies - OpManager
Awards & Honors
- Recognized as a May 2019 Gartner Peer Insights Customers' Choice for Network Performance Monitoring and Diagnostics Software
- Recognised as an April 2019 Gartner Peer Insights Customers' Choice for IT Infrastructure Monitoring Tools.
- Network Management and Monitor Vendor of the Year 2018, 2019
- Entered the 2019 Gartner NPMD Magic Quadrant.
- Ranked #2 in the Infotech Research Software Reviews Data Quadrant 2018.