Help Center
Quick Start
- Overview
- System requirements
- Minimum privileges required
- Default port configuration
- Installing DataSecurity Plus
- Uninstalling DataSecurity Plus
- Starting DataSecurity Plus
- Launching DataSecurity Plus
- Configuring your solution
- Licensing details
- Applying a license
File Auditing
- About File Auditing
- Domain configuration
- File server configuration
- Failover cluster configuration
- NetApp server configuration
- Nutanix server configuration
- Workgroup configuration
- Amazon FSx configuration
Setting up File Audit
Dashboard
Reports
Alerts
Configuration
Storage Configuration
File Analysis
- About File Analysis
- Domain configuration
- File server configuration
- Workgroup configuration
- SMB File Server Configuration
- On-Demand Reports
Setting up File Analysis
Dashboard
Reports
Alerts
Configuration
Data Risk Assessment
- About Data risk assessment
Setting up Data risk assessment
Dashboard
Reports
Ownership analysis
Configuration
Endpoint DLP
- About Endpoint DLP
Setting up Endpoint DLP
Reports
Alerts
Prevention policies
Configuration
Cloud Protection
- About Cloud Protection
- Gateway Server Installation Steps
- Gateway Configuration in Endpoint
- Gateway Cluster Configuration
- Gateway Server Management
- Certificate Authority Configuration
- Two-way SSL configuration
- Manage Certificate Trust Store
- Threat Analytics Database
- Manage Banned Applications
- Manage Authorized Applications
- Regenerating gateway server access key
- Updating gateway server
- Gateway Server Failover
- Load Balancer Configuration
- Global Insight
- Application Insight
- User Insight
- Shadow Application Insight
- Banned Application Insight
- Cloud App Discovery
- File Upload & Download Reports
- Control Policy reports
- General Reports
- Application Insights
- Shadow Domain Insights
- Banned Domain Insights
- GenAI Insights
Setting up Cloud Protection
Dashboard
Reports
Control Policies
Storage Configuration
Administrative settings
- Technician configuration
- Notification filters
- Manage agent
- Agent settings
- SIEM integration
- Business hours configuration
- Two-factor authentication
- Workgroup configuration
- Security policy
Email configuration
General settings
- Connection
- Personalize
- DataSecurity Plus Server
- Privacy Settings
- Disk utilization
- Schedule Retention Policy
Release notes
2026
2025
2024
2023
2022
2021
2020
2019
2018
2017
2016
2015
Troubleshooting
- HTTP communication failure
- Dormant DataEngine
- Secure Gateway server failure
- RPC communication failure
- Cloud Protection Gateway server failure
- Known issues and limitations
- Known errors and solutions
- Report discrepancy in File Analysis
Guides
- Agent document
- How to Migrate/Move DataSecurity Plus
- How to apply SSL certificate
- How to automate DataSecurity Plus database backup
- How to set alerts in DataSecurity Plus
- How to secure your DataSecurity Plus installation
Configuring alerts in the File Audit module
Alerts help stakeholders and administrative users stay on top of critical events in the organization's file storage environment. ManageEngine DataSecurity Plus allows you to create and manage web console and email notifications.
For precise control over alert configuration, DataSecurity Plus supports two types of alerts:
- Global alert profiles, which can be configured for all or a combination of servers.
- Server-specific alert profiles, which are configured individually for specific servers.
Together, these help IT technicians detect access anomalies efficiently while still preventing alert fatigue. Alerts can be created and modified only by administrative technician accounts.
Further, responses can also be automated along with a triggered alert to mitigate the potential damage caused by an incident.
Creating and editing alerts
A) Global alerts
Upon installation of DataSecurity Plus, several built-in global alerts will be automatically activated. These alerts can be configured for events across all the configured servers and domains. For more information, refer to this page. You can also create your own global alerts for specific requirements.
Creating global alerts
To create a global alert:
- Select File Audit from the modules drop-down.
- Go to Configuration > General Settings > Alert Configuration.
- On the Global Alerts tab, click Add Global Alert in the top-right corner.
- Enter a suitable name and description for the alert profile.
- Click the + icon next to the Selected Servers field and choose the servers that you wish to apply this profile to.
- To apply this profile to any new servers that might be added to DataSecurity Plus in the future, check the box next to Apply profile to new servers.
- Classify the alert with an appropriate severity level.
- In the Criteria section, use the following tabs to narrow down the criteria that trigger an alert:
- 8.1. Use the Include tab to select the entities you want to create an alert for.
- 8.2. Use the Exclude tab to exempt trusted entities from the alert.
- 8.3. Use the Threshold tab if you want to configure a threshold-based alert (i.e., to trigger an alert when the number of events occurring within a given duration exceeds the specified value). Click Enable and configure the number of events from a source beyond which the alert should be triggered (for example, 1700 = Events in: = 2 = Minutes by: = Same User).
- 8.4. Use the Response tab to do the following:
- Click Email > Enable email notification.
- Provide the email addresses that you wish to send the alert email to. Separate the addresses with commas. Ensure that there are no spaces in the email addresses.
- Select the option Owner if you want to notify the creator of the file, select Caller if you want to notify the user whose actions have triggered an alert, or select both.
- Assign a Priority level to the email.
- Personalize the email by providing a Subject and Message. By using the Customize option next to each, you can include alert details such as the name of the user, the client, and the IP.
- If necessary, you can limit the number of emails sent to each recipient by configuring an appropriate value in the Send a maximum of section. For example, if you have configured a threshold-based alert for 10,000 access events in one minute, and you set this section to Send a maximum of = 1 = mail(s) in = 1 = Hour(s), after the initial alert, one email will be sent every hour if the unusual access trend continues.
- Click Script > Enable Script.
- In the Script Files field, select the script of your choice. You can choose from the built-in scripts or create your own.
- In the Arguments field, select the arguments in the intended order for the response's proper execution.
- Once you have chosen one or multiple responses, click Save.
8.4.1. To send an email notification to a stakeholder:
8.4.2. To automate a response action when the alert is triggered:
For example, if you want to disable a user who is mass deleting files, the alert configuration will look similar to this:
Include: Action = In = Delete
User Object = In = ALL
Threshold Limit: 50 = Events in: = 1 = Minutes by: = Same User
Script Files: disableADAccount
Arguments: User Name
Modifying global alerts
To modify an existing global alert:
- Select File Audit from the modules drop-down.
- Go to Configuration > General Settings > Alert Configuration.
- On the Global Alerts tab, within the Actions column, you'll find an edit icon for each of the configured alerts. Click the edit icon next to the alert you want to update.
- Update the required details.
- Click Save, then click OK.
B) Server-specific alerts
When earlier installations (prior to build 6060) are updated to the latest build, existing custom alerts will be moved to the Server Specific Alerts tab. When a server is selected in the Server Name field of that tab, both the global alerts and server-specific alerts that apply to the selected server will be displayed in corresponding tables.
Creating server-specific alerts
To create a server-specific alert:
- Select File Audit from the modules drop-down.
- Go to Configuration > General Settings > Alert Configuration.
- Click the Server Specific Alerts tab.
- In the Server Name field, choose the server for which you want to customize the alert.
- Click Add Server Alert in the top-right corner of the tab.
- Enter a suitable name and description for the alert profile.
- Classify the alert with an appropriate severity level.
- In the Criteria section, use the following tabs to narrow down the criteria that trigger an alert:
- 8.1. Use the Include tab to select the entities you want to create an alert for.
- 8.2. Use the Exclude tab to exempt trusted entities from the alert.
- 8.3. Use the Threshold tab if you want to configure a threshold-based alert (i.e., to trigger an alert when the number of events occurring within a given duration exceeds the specified value). Click Enable and configure the number of events from a source beyond which the alert should be triggered (for example, 1700 = Events in: = 2 = Minutes by: = Same User).
- 8.4. Use the Response tab to do the following:
- Click Email > Enable email notification.
- Provide the email addresses that you wish to send the alert email to. Separate the addresses with commas. Ensure that there are no spaces in the email addresses.
- Select the option Owner if you want to notify the creator of the file, select Caller if you want to notify the user whose actions have triggered an alert, or select both.
- Assign a Priority level to the email.
- Personalize the email by providing a Subject and Message. By using the Customize option next to each, you can include alert details such as the name of the user, the client, and the IP.
- If necessary, you can limit the number of emails sent to each recipient by configuring an appropriate value in the Send a maximum of section. For example, if you have configured a threshold-based alert for 10,000 access events in one minute, and you set this section to Send a maximum of = 1 = mail(s) in = 1 = Hour(s), after the initial alert, one email will be sent every hour if the unusual access trend continues.
- Click Script > Enable Script.
- Click the + icon next to the Script Files field to select the script of your choice. You can choose from the built-in scripts or create your own.
- In the Arguments field, select the arguments you want to pass in the intended order of execution. The Sample command-line format of the script text box illustrates the sequence in which the arguments will be executed.
- Once you have chosen one or multiple responses, click Save.
8.4.1. To send an email notification to a stakeholder:
8.4.2. To automate a response action when the alert is triggered:
For example, if you want to disable network access for any machine when a particular file is deleted, configure the alert settings using the details below:
Include: Action = In = Delete
Current File Name = Contains = EmployeeData
Script Files: disableNetwork
Arguments: Host Name
Modifying server-specific alerts
To modify an existing server-specific alert:
- Select File Audit from the modules drop-down.
- Go to Configuration > General Settings > Alert Configuration.
- Click the Server Specific Alerts tab.
- Within the table's Actions column, click the edit icon next to the alert you want to update.
- Update the required details.
- Click Save, then click OK.
Automated alert responses
Users can instruct the File Audit module to execute a response action when an alert is triggered. For this, you must link the desired script file in the Script Files field while configuring alerts. The script files can be PowerShell files, VBScript files, executables, and batch files. These automated, versatile responses help you perform remedial actions the instant a security incident is detected, reducing the damage caused.
To target these commands at specific entities in your network, configure one or more Arguments to provide the necessary inputs in the commands. The selected parameters will be replaced in the commands by the corresponding values from the alert event.
Arguments and their descriptions
The arguments below can be used based on the alert profile configured.
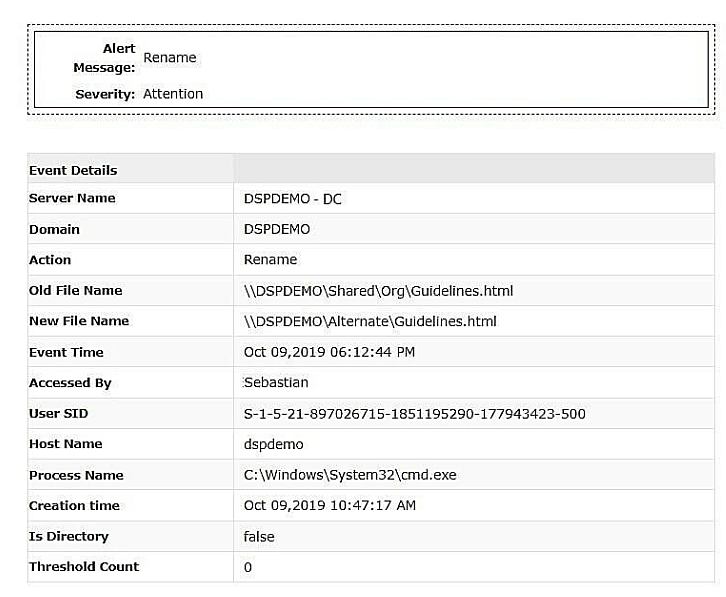
| Argument | What it refers to | Example (How it will be displayed in the alert notification) |
| User Name | The sAMAccountName of the user who performed the action | Sebastian |
| User SID | The security identifier (SID) of the account that generated the event | S-1-5-21-1798521379-1002 |
| Server Name | The name of the file server or machine where the file resides | DSPDEMO, FS01, etc. |
| Local Path | The location of the file or folder on which the action was performed | C:\Program Files (x86)\ManageEngine\DataSecurity Plus\file.txt |
| Process Name | The name and full path of the process that carried out the file action: The Process Name will be collected only for file actions generated locally on the file server | C:\Windows\System32\cmd.exe |
| Old Share Path | The Universal Naming Convention (UNC) path of a file before the action was performed on it: If the action is neither move nor rename, the Old Share Path and the New Share Path will be the same | \\DSPDEMO\Shared\Org\Guidelines.html |
| New Share Path | The UNC path of a file after the action was performed on it: When a move or rename action triggers an alert, the New Share Path shows the new location of the file after the completion of the action | \\DSPDEMO\Alternate\Guidelines.html |
| Client IP | The IP address of the client machine where the file action was generated: It may be either IPv4 or IPv6 | fe80::70c2:7c81:c35f:29c7%12, 192.168.0.33 |
| Client Host | The name of the client machine from which the file action was initiated | dspdemo |
Example of a notification email for a triggered alert
Default script responses
The DataSecurity Plus installation package contains some built-in scripts for commonly used response actions. Some of these are in the table below:
| Script file name | Script action | Applicable arguments in the UI | Sample use case |
| disableADAccount.ps1 | *Disables AD accounts | User SID | This can be used to disable the source user account of the file change that triggered the alert. |
| disableNetwork.ps1 | Disables network access on machines | Client IP, Client Host, or Server Name | This can be used to disable network access on the source machine of the file change that triggered the alert. |
| triggerShutdown.bat | Shuts down computers or servers | Client IP, Client Host, or Server Name | This can be used to shut down the source machine of the alert-triggering file action. In case of a ransomware attack or data breach, the Server Name argument can be used to stop the spread of the incident by shutting down the affected server. |
| ransomwareResponse.ps1 | *Locks out the source user account, ends the user session, and shuts down the host machine, provided the host machine and the DataSecurity Plus server belong to the same network | User Name, Client Host, and Server Name | When a potential ransomware attack is launched, this response script will prevent the ransomware from spreading by isolating the contaminated machine, locking out the user, ending the user's session, and shutting down the host machine. |
*The below services need to be enabled in the machine where DataSecurity Plus is installed for the successful execution of certain script files.
- Windows Remote Management
- Type Services in the Start Menu and open the Services window.
- Select the Windows Remote Management (WS - Management) service.
- In the left pane of the window, under Services (Local), click Start the service.
- RSAT: Active Directory Domain Services and Lightweight Directory Services Tools
- Type Apps & features in the Start Menu.
- Select Optional features and click Add a feature in the top-left corner.
- Type RSAT: Active Directory Domain Services and Lightweight Directory Services Tools in the search bar, select it, and click Install.
Generating a password for alert scripts
We recommend generating an encrypted password for your script files, which is used for authentication when executing the intended scripts. To set a password, follow these instructions:
- Navigate to [installation_directory]\bin\alertScripts > helper folder.
- Execute the generatePassword.bat script to set up authentication.
- In the Windows PowerShell credentials request window, enter your PowerShell credentials beside the User name and Password fields to generate an encrypted password. Ensure that you give the correct password to authenticate the server.
- Click OK.
Disabling alerts
You can disable an alert to temporarily stop it from being triggered. To disable an alert:
- Select File Audit from the application drop-down menu.
- Go to Configuration > General Settings > Alert Configuration.
- If you want to disable a server-specific alert, select that server in the Server Specific Alerts tab. Otherwise, stay in the Global Alerts tab.
- From the table, select the checkbox next to the alert(s) you wish to disable.
- Click the disable icon at the top of the table.
The selected alert(s) will be disabled.
Deleting alerts
To delete an alert permanently:
- Select File Audit from the application drop-down menu.
- Go to Configuration > General Settings > Alert Configuration.
- Select the tab corresponding to the type of alert you wish to delete.
- From the table, select the checkbox next to the alert(s) you wish to delete.
- Click the delete icon at the top of the table.
- Click OK to confirm the action.
The selected alert(s) will be deleted.
For more information on configuring alerts in DataSecurity Plus, refer to this guide.